- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Re: Conditional policies in Azure AD vs. Intune
Conditional policies in Azure AD vs. Intune
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 01 2017 05:30 AM
We would like to implement conditional access policies for a group of our users through Azure AD. Are these policies different from the Conditional access policies available in Intune? Also, I was wondering if there were any pitfalls to enabling modern authentication for EXOL and Skype for business?
- Labels:
-
Conditional Access
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 01 2017 10:14 PM
SolutionI have not found any pitfalls to enabling modern authentication for EXO or Skype for business.
In my experience, it may take a few days before the setting will take effect for the SFB whereas there doesn't seem to be much delay for it to begin working in EXO.
One thing you may run into is your Global Admins may struggle to get remote powershell to work after enabling MFA on their accounts. To solve this, download the latest powershell modules for SFB and Exchange.
Skype Powershell Module Download
http://go.microsoft.com/fwlink/?LinkId=294688
New Exchange PowerShell Module that supports MFA
https://technet.microsoft.com/en-us/library/mt775114(v=exchg.160).aspx
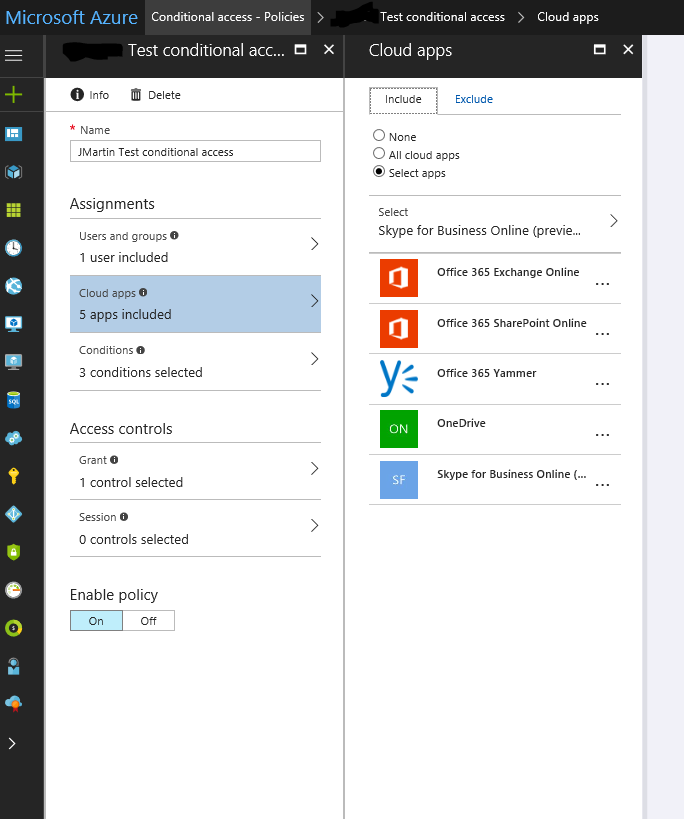
The conditional access for Intune is merging into the Azure AD Premium conditional access in the Azure portal (http://portal.azure.com).
If you have a device enrolled in Intune, conditional access in Azure AD can leverage that to check compliance.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 03 2017 07:07 AM
@Joe Stocker and there is no ADFS requirement for any of this to work correct?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 03 2017 07:12 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 03 2017 07:17 AM
Thanks @Dean Gross. We want to use the Conditional Policies but just use password sync and not ADFS. I just wanted to triple check that turning on Modern Auth which seems to be required for the conditional policies to work was not going to hose any of my users that are still on 2013 apps.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 03 2017 07:26 AM
Making decisions like this is always challenging because the requirements keep changing.
Have you seen this announcement? you can try to keep up with the changes at https://docs.microsoft.com/en-us/intune/whats-new.
Week of June 5, 2017 Microsoft Intune and Conditional Access admin consoles are generally available
We’re announcing the general availability of both the new Intune on Azure admin console and the Conditional Access admin console. Through Intune on Azure, you can now manage all Intune MAM and MDM capabilities in one consolidated admin experience, and leverage Azure AD grouping and targeting. Conditional access in Azure brings rich capabilities across Azure AD and Intune together in one unified console. And from an administrative experience, moving to the Azure platform allows you to use modern browsers
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 03 2017 07:29 AM
Make sure to update Azure AD Connect, there was a Security Advisory last week https://technet.microsoft.com/en-us/library/security/4033453.aspx?f=255&MSPPError=-2147217396
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 03 2017 07:34 AM
Yep that one is on change control for today!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 03 2017 09:30 AM
Robert,
Since you mentioned you have users on Office 2013, you will need to roll out two registry keys as described here:
This is not required for Office 2016, as it supports modern authentication by default.
Note: If you do not roll out these registry keys, but you run the two powershell commands in your tenant for Exchange and Skype to support MFA, it does no harm. Just keep in mind the following sequence:
- enable Modern Auth (MFA) at the tenant level by running the two powershell commands (one for Skype and one for Exchange
- Roll out registry keys for Office 2013
- Enable users for MFA
So as you can see, until you enable a user for MFA, there is no impact to the users. Prior to enabling a user for MFA, just be sure to deploy the reg keys to them.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 24 2018 11:39 PM
@Robert Woods Moreover ADFS and EM+S features are in the same pace. And to manage ADFS and all its proxy servers is a tough job. So EM+S is a cloud platform mainly handled by Microsoft and the best Practice is to remove ADFS as it conflicts in many places like with EM+S features as Azure AD Premium (Conditional Access policy)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 25 2018 01:31 AM
Hi,
Keep in mind that you control modern authentication with Conditional Access, legacy authentication like POP, IMAP, or EWS is not using modern authentication. So you might need to take care of theses workloads. For example turn them off in the services... In the past the recommendation was to use ADFS to block legacy auth:
Block apps that do not use modern authentication (ADAL)
https://docs.microsoft.com/en-us/intune/app-modern-authentication-block
But there is an upcoming feature to allow blocking of legacy auth with Conditional Access. It is in private preview at the time of writing and will be in public preview soon. So keep an eye on Conditional Access announcements. If available you shouldn't need ADFS anymore (except if you have other special requirements for it).
best,
Oliver
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 25 2018 07:41 AM
My tenants got updated today :thumbs_up: and support now Conditional Access for legacy auth:
best,
Oliver
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 11 2018 02:04 AM
Hi!
Did you get this work?
Doesn't work for me.
Regards, Joonas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 26 2018 12:37 PM
Yes it's working for me and several other tenants. It takes a couple of hours to apply but then it's working.
Check out these links for good documentation:
best,
Oliver
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 25 2019 02:50 PM - edited Feb 27 2019 12:42 PM
Crafting CA rules for InTune, noticing there are two app registrations related to InTune, Is the enrollment one literally just the initial call to register and the other more long-term or? Thanks
- Microsoft InTune
- Microsoft InTune Enrollment
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 01 2017 10:14 PM
SolutionI have not found any pitfalls to enabling modern authentication for EXO or Skype for business.
In my experience, it may take a few days before the setting will take effect for the SFB whereas there doesn't seem to be much delay for it to begin working in EXO.
One thing you may run into is your Global Admins may struggle to get remote powershell to work after enabling MFA on their accounts. To solve this, download the latest powershell modules for SFB and Exchange.
Skype Powershell Module Download
http://go.microsoft.com/fwlink/?LinkId=294688
New Exchange PowerShell Module that supports MFA
https://technet.microsoft.com/en-us/library/mt775114(v=exchg.160).aspx
The conditional access for Intune is merging into the Azure AD Premium conditional access in the Azure portal (http://portal.azure.com).
If you have a device enrolled in Intune, conditional access in Azure AD can leverage that to check compliance.