- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Re: Conditional Access - Required Device to be Compliant
Conditional Access - Required Device to be Compliant
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 18 2018 07:24 AM
I have created a conditional access policy to only allow access to an application (Zendesk) where we use Azure AD Single Sign-on. The policy does work if I select MFA or if I exclude my trusted IPs.
Every setting will take effect on the policy with the single exception of the "Require device to be marked as compliant" option under Grant Access. This will simply prevent access because after logging in, the device being use is not recognized as a compliant device... however in Intune and in Azure AD the device is defined as compliant.
This is frustrating because we don't want to prompt for MFA on approved devices, i.e., company provided/managed laptops for our remote employees.
Has anyone been able to use this policy and if so, can you shed any light on why this might be an issue?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 01 2018 12:49 PM - edited May 01 2018 12:49 PM
How do you have Access controls set? which checkboxes are ticked and require one or all selected controls?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 08 2018 01:16 AM
I'm facing now the same issue with LOB app which is trying to connect to Exchange. Based on error it looks like during authorization app is not reporting device ID to Azure, that is why Azure is not able to process request.
Trying to fix that with support for almost a month. No luck yet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 08 2018 05:24 AM
Hi James,
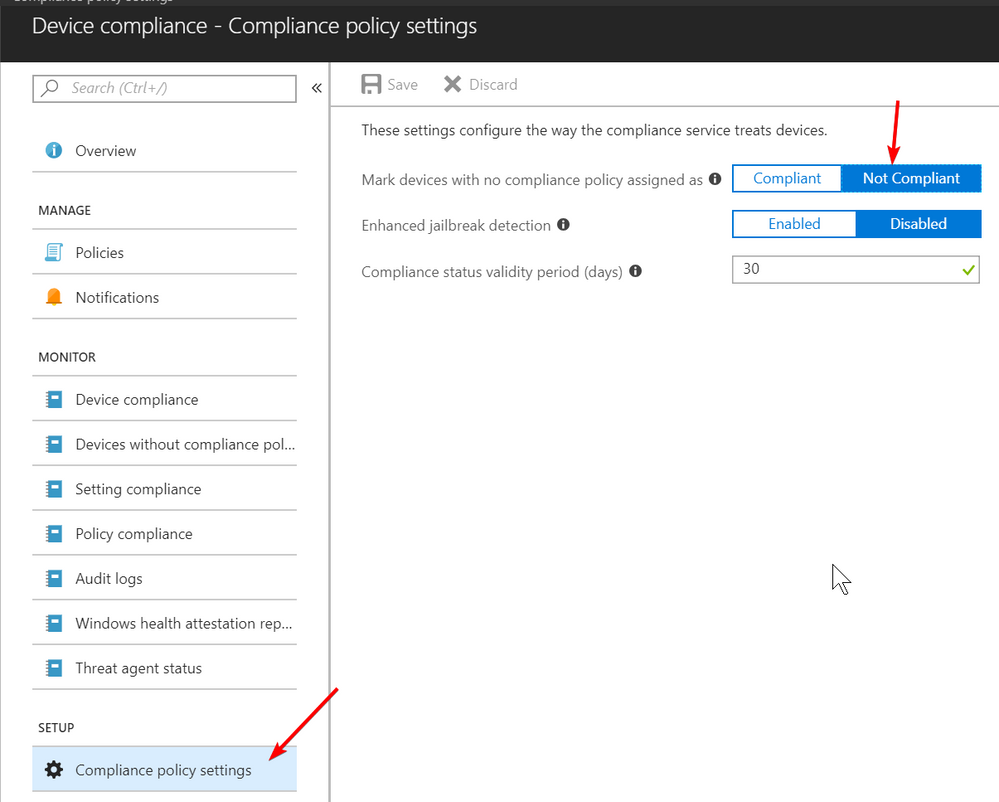
since a few weeks you need to have a compliance policy assigned to your devices otherwise they are treated as non-compliant. So there are to options to get your device to a compliant state. Assign a compliance policy to the user or device or change the default to allow devices without compliance policy to be treated as compliant by default.
best,
Oliver