- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Conditional Access Policy compliant devices on Android devices
Conditional Access Policy compliant devices on Android devices
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 22 2020 05:40 AM
Hello everybody,
has anyone ever set up a Conditional Access Policy that ensures, that only managed devices (marked as compliant) can access Exchange Online?
I tried that and basically it also works for Windows, iOS and Android devices.
Unfortunately there is a problem with managed e-mail profiles on Android devices.
We have configuration profiles that create an exchange online account with Oauth login on the devices. To check the emails, the Gmail app is rolled out on the devices and the Gmail app accesses the managed Exchange Online profile.
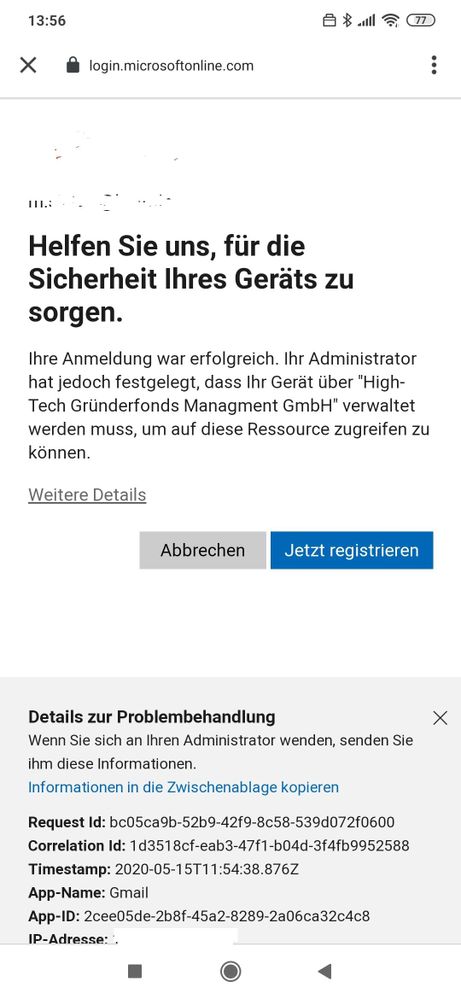
This works well, but as soon as I activate the Conditional Access Policy and an Android user has to authenticate again, e.g. because of a password change or on a new device, the login mask reports that the device is not registered and that the Microsoft company portal app should be downloaded first.
This message is wrong, the device is registered and everything else works. It occurs on different devices. As a temporary solution, I deactivated the policy for Android devices.
Has anyone ever had this problem?
Kind regards
Marco
- Labels:
-
Conditional Access
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 22 2020 07:39 PM - edited May 22 2020 07:44 PM
I know you have CA enabled to allow ActiveSync but you also have Android Profile to use Modern Auth. I suspect the the test will work as expected if you use Outlook app not Gmail.
Hope this helps!
Moe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 25 2020 01:19 AM
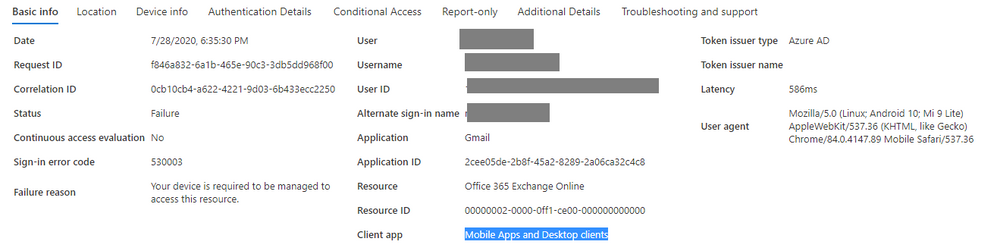
@marcosiefert You might get some info when you have a look in Azure AD at the Sign-ins. If you have a look at the client app which is used, you should be able to see if Gmail is a legacy auth app. Only browser and Mobile apps and desktop is modern, all others are legacy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 30 2020 04:38 AM
Please excuse the late reply.
I checked it in Azure at the sign-ins.
Gmail is shown as "Mobile Apps and Desktop clients", so it should work.
When Gmail connects to Exchange Online, a Modern Authentication login mask is shown. Multi-factor authentication also shows up, but after confirmation the login process stops with the message that the device is not registered, although it is registered. The problem doesn't occur with any other app, just Gmail.
Seems to be a bug, doesn't it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 30 2020 09:01 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 31 2020 08:49 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 26 2020 04:29 AM
@marcosiefert Bit of a longshot on this older thread, but did you manage to get this resolved? I am running into exactly the same issue.
Android device is marked a compliant but the config process does not seem to honor it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 26 2020 05:07 AM
no, unfortunately I never could solve that.
I had opened two cases with Microsoft Support.
The first support agent claimed that we had set up our Intune environment completely wrong. That answer was total nonsense.
In the second case, the support agent was more helpful and even escalated the ticket. A lot of analysis has been done, but the problem could not be solved. The final answer was this:
... GMAIL application is unable to pass the device information for the exchange account added to it so that is the only reason its unable to satisfy the Conditional Access Policy ...
So it looks like it is a bug in the Gmail app.
However, since we want to use the native Android calendar and contacts apps, we cannot switch to the Outlook app, but still have to push the Exchange profile via Intune. If I'm not mistaken, you need the Gmail app for the final setup on the smartphone.
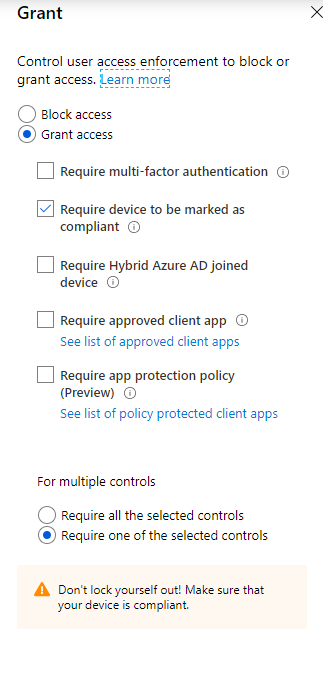
As a workaround we have now changed the conditional access policy. I removed "Office 365 Exchange Online" from the selected cloud apps to which the policy is applied. However, it is applied to "Office 365 SharePoint Online" and "Microsoft Teams".
Since all users also want to use Microsoft Teams on their smartphones, they are forced to register their device in Intune and thus the goal of the policy has been achieved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 05 2021 11:58 AM