- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Cannot Reseal Windows 11 device while pre-provisioning
Cannot Reseal Windows 11 device while pre-provisioning
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 17 2022 02:32 PM
Before I reinvent the wheel, I thought I’ll post the issue here. I have a AP profile configured as below.
Deployment mode User-Driven
Join to Azure AD as Azure AD joined
Language (Region) Dutch (Netherlands)
Automatically configure keyboard Yes ( In know.. please read on)
Microsoft Software License Terms Hide
Privacy settings Hide
Hide change account options Hide
User account type Standard
Allow pre-provisioned deployment Yes
Apply device name template Yes
Enter a name XXXX-%SERIAL%
I know I’ve set the auto keyboard to yes, but here me out. As far as I understood the previously known issue is fixed in Windows 11. Windows Autopilot for pre-provisioned deployment | Microsoft Docs
In Windows 10, version 2004 and later, if the Autopilot deployment profile Language/Region setting is not set to User Select, then OOBE will progress past the language/region/keyboard selection screens. This causes the pre-provisioning technician to arrive at the Azure AD login page, which is too late to enter pre-provisioning. This issue is fixed in Windows 11.
For the pre-provisioning part:
On Windows 10 21H2 (10.0.19044.1645) I can pre-provision the device successfully. The technician flow completes and I have a green screen giving me the option to reseal. After reboot, the normal user flow follows, and the device is ready to go before you know. AAD joined and MDM enrolled with user affinity.
However, on Windows 11 (10.0.22000.675) the technician flow starts OK. I’m presented with the AP profile that is selected, and I can continue pre-provisioning. But it never shows me the green screen and I’m not able to reseal the device. It also does not show any errors what so ever during pre-provisioning. The device simply reboots and ends up at the login screen. The user flow does not seem to start and from the login screen, I’m also not able to sign-in with any account.
At this stage, I checked the device in the AP portal. The interesting thing is, that the device seems to be AAD joined and MDM enrolled. And as expected, there is no primary user yet in Intune.
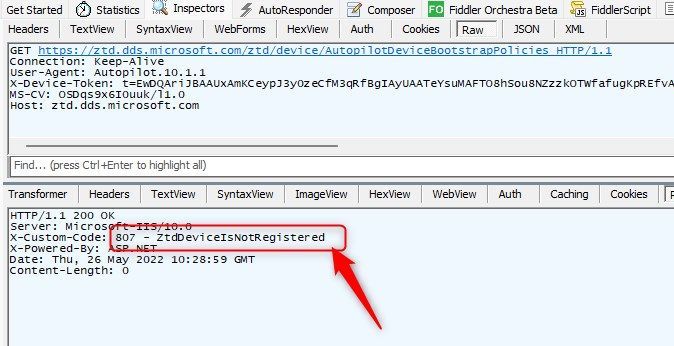
So I looked up the device in Azure AD and confirmed it is AAD joined. Although I don’t believe the info presented. I also looked up the device in MEM/Intune and collected the diagnostics logs from the device.
Still in the process of diving into the logfiles but here are some of my findings:
intunemanagementextension.log shows some interesting things:
- GetAADJoinInfo - Failed to get Azure AD Join information using NetGetAadJoinInformation
-