- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Re: Bitlocker recovery keys not syncing on OnPrem devices
Bitlocker recovery keys not syncing on OnPrem devices
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 03 2022 12:44 PM
Steps U do.
Move devices in SCCM into a collection where Intune controls everything, devices are on-prem.
All policy's work, but the Bitlocker recovery keys does not sync from AD to Intune.
If I manually go to the device I can trigger a Bitlocker key rotation and one key shows up. Fully AAD devices that went thru Autopilot has two recover keys in Intune.
Not sure how everyone is handling this but I did find a remediation script.
https://call4cloud.nl/2021/02/b-for-bitlocker/
But is there any other way of handling this and why is it happening?
- Labels:
-
Intune
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 03 2022 02:06 PM
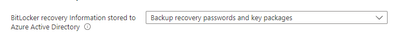
The following option is not present in a Bitlocker policy, but present in a Endpoint protection policy template. Would this actually solve it? And do i have to delete the Bitlocker policy or is there anyway of me setting only that option?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 03 2022 06:57 PM
SolutionHi @JimmyWork
Do you have on premise GPO? If you do, bear in mind it will always win, so make sure its disabled on devices that scoped in Intune policy.
I would also use Intune Endpoint Protection Template (like you mentioned above) and make sure the setting you attached is selected and also the one I attached.
I have used the script below last year to migrate the keys into AAD, hope it helps as well
https://msendpointmgr.com/2021/01/12/migrate-bitlocker-to-azure-ad/
Moe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 04 2022 08:03 AM
https://docs.microsoft.com/en-us/windows/client-management/mdm/policy-csp-controlpolicyconflict
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 04 2022 08:08 AM
Also in your image you are using a Endpoint protection policy template, I have configure Bitlocker policy with a Bitlocker policy template, the option
"Store recovery information in Azure Active Directory before enabling BitLocker" is not available in my config, I do however have "Require device to back up recovery information to Azure AD"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 04 2022 08:50 AM - edited Jun 04 2022 08:58 AM
Got it, thanks for the clarification!
I still think disabling GPO policy would remove some complexity in your case. There are multiple places for Bitlocker in MEM and I would stay on one policy from MEM.
Moe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 04 2022 01:52 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 05 2022 08:57 PM
Azure AD devices should be fine.
Moe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 08 2022 12:01 AM
I did uninstall the SCCM client, the device has the Bitlocker policy applied from Intune, fully managed by Intune now. No bitlocker key still
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 08 2022 04:04 AM
Not surprised by this behavior as the bitlocker policy applied and the device is already encrypted. You can use the powershell to escrow the keys in Azure AD or disable bilocker manually and let the policy encrypt them again.
Moe
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 08 2022 05:46 AM
Thank you again for answering.
What I'm currently trying is that I used the following PS script.
Window- Devices -PowerShell scripts.
Assigned it to a Device, but for some reason it has yet run, after 4 hours.
$BitLocker = Get-BitLockerVolume -MountPoint $env:SystemDrive
$RecoveryProtector = $BitLocker.KeyProtector | Where-Object { $_.KeyProtectorType -eq 'RecoveryPassword' }
BackupToAAD-BitLockerKeyProtector -MountPoint $env:SystemDrive -KeyProtectorId $RecoveryProtector.KeyProtectorID
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 08 2022 11:33 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 08 2022 11:40 AM
PowerShell script
Run this script using the logged on credentials
No
Enforce script signature check
No
Run script in 64 bit PowerShell Host
Yes
Assigned to a device group.
Checked the Device status report on the Script and if any keys actually showed up.
Will check the device tomorrow, maybe ASR rules are blocking the script from running?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 09 2022 02:23 AM
For some reason it was not triggered yesterday, but today it ran when i re-created the powershell script and it's working :)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 03 2022 06:57 PM
SolutionHi @JimmyWork
Do you have on premise GPO? If you do, bear in mind it will always win, so make sure its disabled on devices that scoped in Intune policy.
I would also use Intune Endpoint Protection Template (like you mentioned above) and make sure the setting you attached is selected and also the one I attached.
I have used the script below last year to migrate the keys into AAD, hope it helps as well
https://msendpointmgr.com/2021/01/12/migrate-bitlocker-to-azure-ad/
Moe