- Home
- Security, Compliance, and Identity
- Microsoft Entra
- Intro to querying Azure AD sign-in and audit logs held in Azure Monitor from PowerShell
Intro to querying Azure AD sign-in and audit logs held in Azure Monitor from PowerShell
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 09 2019 04:33 PM - last edited on Nov 09 2023 11:09 AM by
Some questions I'm asked frequently about Azure AD - how can I see and retain more than 30 days of audit events from Azure AD features? And how can I get that audit history programmatically, without needing to sign in as a highly-privileged Azure AD administrator, in order to download records for a report to or answer an auditor’s inquiry?
Last year we announced that organizations with Azure AD Premium and an Azure subscription could start to build custom reports on their Azure AD audit and sign in logs, by configuring Azure AD to send those logs to Azure Monitor. We also built several reports for sign in analysis as Azure AD workbooks, and showed to set triggers for alert notifications.
Once you've configured Azure AD to send logs to Azure Monitor, you can also access those logs through PowerShell, sending queries from scripts or from the PowerShell command line, without needing to be a Global Admin in the tenant. Because Azure services have changed their name in the past few years, it's sometimes challenging to figure out which PowerShell command to use. So I've written down a few steps I used when learning how to query Azure AD logs that have been sent to Azure Monitor.
Before you begin, if you haven't already configured this integration between Azure AD and Azure Monitor, you'll need to follow the steps to Integrate Azure AD logs with Azure Monitor logs.
Next, you'll want to ensure you (or the user or service principal who will be authenticating to Azure AD) are in the appropriate Azure role in the in the Log Analytics workspace, either the Log Analytics Reader role, or the Log Analytics Contributor role.
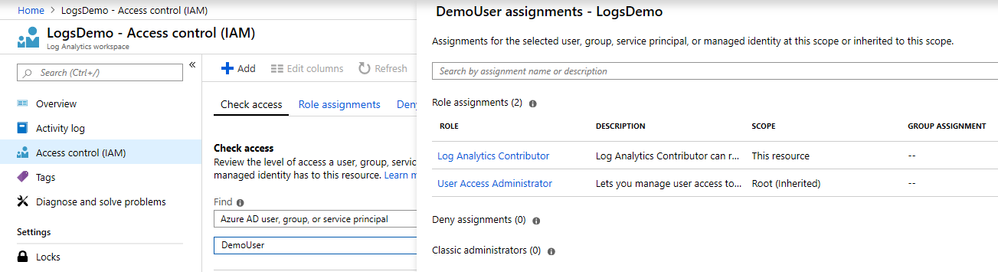
You can set this role assignment in the Azure Portal by locating the Log Analytics workspace, clicking on "Access Control (IAM)" and clicking Add to add a role assignment.
Then, launch PowerShell, and then install the Azure PowerShell module, if you haven’t already, by typing
install-module -Name az -allowClobber -Scope CurrentUser
Now you're ready to authenticate to Azure AD, and retrieve the id of the Log Analytics workspace you’ll be querying. If you have only a single Azure subscription, and a single Log Analytics workspace, then authenticate to Azure AD, connecting to that subscription and retrieving that workspace, by typing
Connect-AzAccount
$wks = Get-AzOperationalInsightsWorkspace
It's important to note that Get-AzOperationalInsightsWorkspace operates in one subscription at a time. If you have multiple Azure subscriptions, then you'll want to ensure you connect to the one which has the Log Analytics workspace with the Azure AD logs. The cmdlets
Connect-AzAccount
$subs = Get-AzSubscription
$subs | ft
displays a list of subscriptions, and then find the id of the subscription which has the Log Analytics workspace. You can re-authenticate and associate your PowerShell session to that subscription using a command such as Connect-AzAccount –Subscription $subs[0].id . (And to learn more about how to authenticate to Azure from PowerShell, including non-interactively, see Sign in with Azure PowerShell. )
If you have multiple Log Analytics workspaces in that subscription, then the cmdlet Get-AzOperationalInsightsWorkspace returns the list of workspaces, so you can find the one which has the Azure AD logs. The CustomerId field returned by this cmdlet is the same as the value of the "Workspace id" displayed in the Azure Portal in the Log Analytics workspace overview.
$wks = Get-AzOperationalInsightsWorkspace
$wks | ft CustomerId, Name
Finally, once you have a workspace identified, you can use Invoke-AzOperationalInsightsQuery to send a Kusto query to that workspace. These queries are written Kusto query language.
For example, you can retrieve old sign in records from the Log Analytics workspace, with a query like
$sQuery = "SigninLogs | where TimeGenerated > ago(3653d) | order by TimeGenerated asc | limit 10"
$sResponse = Invoke-AzOperationalInsightsQuery -WorkspaceId $wks[0].CustomerId -Query $sQuery
$sResponse.Results | ft TimeGenerated,userDisplayName,UserPrincipalName
Or audit records with
$aQuery = "AuditLogs | where TimeGenerated > ago(3653d) | order by TimeGenerated asc | limit 10"
$aResponse = Invoke-AzOperationalInsightsQuery -WorkspaceId $wks[0].CustomerId -Query $aQuery
$aResponse.Results |ft TimeGenerated,Category,OperationName,Result
I hope to find more interesting examples of Kusto queries for the Sign in and Audit logs in future. Thanks!