- Home
- Security, Compliance, and Identity
- Microsoft Entra
- Re: Azure AD Sign-in to Azure VMs fails due to enforced MFA (I think)?
Azure AD Sign-in to Azure VMs fails due to enforced MFA (I think)?
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 26 2022 08:22 AM
Hi,
I have an Azure AD Tenant (Free) and I have connected an Azure VM to it, but find that I cannot login with my Azure AD account (with VM Administrator RBAC role) from my home Win10 machine (that is also connected to the Azure AD Tenant) - I think this must be because my Azure AD account has enforced MFA configured?
If I create another Azure AD account (with VM Admistrator RBAC role), then login via the portal to change the initial password set at user creation, but decline to set MFA (can only do this for 14 days) - I can then use this account to RDP to the Azure VM successfully.
Is this expected behaviour? Is there some way that I can login using Azure AD accounts that have enforced MFA, as it seems all Azure AD accounts in the free AD tenant have enforced MFA (as I have to login to the Azure portal using the account to change the initial password before I can login via RDP with it - and portal access requires enforced MFA)?
Or, am I missing something here...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2022 06:44 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2022 07:09 AM
Hi@joeyvldn thanks for taking the time to reply to my question.
I am signing in to my local Win 10 21/H2 laptop using Windows Hello PIN auth - which I understand is considered a strong authentication method.
I can't remove the MFA requirement for my user account as it is the account that I use as Global Admin for my tenant and also when logging in to Azure portal - On the free Azure AD Tenant, both of these force MFA which can't be turned off.
If I create another user account in Azure AD to use as the login account for the Azure VM, I have to first try and login to the portal with this user account to reset the initial password, before I can login to the Azure VM with it. At this point, as I have tried to login to the Azure Portal with the account, then it sets a timer of 14 days until it will enforce MFA. The account works in the short-term for logging in to the Azure VM, but I presume this will stop working in 14 days.
When I look at the Azure User's sign-in logs, you can see that the Windows Sign-In shows as successful:
But it is the pass-through authentication that is sent to the Azure VM's Windows OS that then fails to login to the Windows session on the VM:
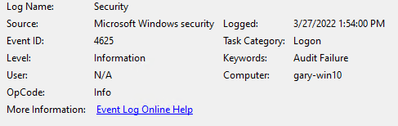
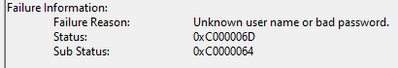
When I look at the security logs on the VM, all I see is a Windows 4625 error which does not give me much of a clue as to why it did not allow the login:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 28 2022 06:29 AM
When u have configured MFA for your user object it should not show the 14 days reminder. So i guess;
1: MFA is not configured for the user account logging in
2: There must be a CA policy requiring MFA?
Could you show your CA policies? What happens if u exclude the user from the CA policies?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 28 2022 07:46 AM
MFA is setup on the account that I don't seem to be able to login to the Azure VM with - and gives the error in my original screenshot.
If I login using another account that is not a global admin, but had to change the user's initial password by logging first into the Azure Portal (as you can't do Azure VM logins with intial temp passwords) - I then get the message saying that I must enable MFA on the account. But, I chose not to do this and it gives you 14 days grace to set it up. This account can login to the Azure VM successfully - this is what leads me to believe that it must be the enforced MFA (not via a CA policy) that is preventing my original user from logging in as this is the only difference I can think exists between the two accounts.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 28 2022 09:08 AM
I have discovered that if I disconnect the Azure VM from Azure AD and then re-join using my Azure AD (Global Admin, Work/School account) - then I can RDP to the Azure VM successfully using the same account (i.e. the one that does not work if the account is joined at deployment time).
It definitely seems to be something to do with MFA being enforced by the "Security defaults" Conditional Access policy (which I can't disable as it is a system policy) - I found this in the Azure AD Sign-In logs, which I think is related to the failure (even though the failure occurs on the Azure VM login screen):
Why is it insisting on MFA and failing the CA policy when joined at deployment time, but not if I join it manually after deployment?
Even if it insists on MFA, shouldn't I pass this OK with the strong authentication of Windows Hello and PIN from my Azure-AD joined home laptop (I have even tried when logged into the laptop as the Azure AD (Global Admin, Work/School account) instead of a local account, but this does not help.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 28 2022 09:41 AM
I have discovered that it is definitely the Azure AD "Security Defaults" that are now enabled by default on new Azure AD Tenants:
If I set this to No - then I can login with the Azure AD (Global Admin, Work/School) account that I could not login with previously.
What I don't understand is why the strong Authentication of Windows Hello and PIN from my Azure AD joined home laptop does not allow this MFA requirement to be passed when the "Security Defaults" is enabled?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 28 2022 09:48 AM
So, your issue is solved?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 28 2022 10:04 AM
With the Azure AD Free tenant, it is not possible to turn off MFA for the Windows Sign-In cloud app (listed as a work-around) as there is no access to CA policies.
Also Windows Hello with PIN should allow the MFA requirement to be passed shouldn't it - but I am not seeing this?
And, why is it if I disconnect the Azure VM from Azure AD and then re-join it manually from within Windows, I can then login successfully with the account that I could not login with before with Security Defaults still enabled on the Azure AD tenant properties?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 22 2022 12:15 AM
sounds like Microsoft is saying you need P1 or higher to work with anything related to azure ad joined resources. You have the same problem with AVD and there is no workaround other disabling default security settings