- Home
- Microsoft 365
- Microsoft 365
- Re: Outgoing emails marked as SPAM and Phishing emails by O365 servers
Outgoing emails marked as SPAM and Phishing emails by O365 servers
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Apr 10 2019
08:51 AM
- last edited on
Feb 01 2023
10:23 AM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 10 2019
08:51 AM
- last edited on
Feb 01 2023
10:23 AM
by
TechCommunityAP
Hi,
Since yesterday, all outgoing emails from our organization using Office365 (fully cloud) are being flagged as either spam or phishing email by Microsoft Outbound email servers. Due to this our Office365 user accounts are getting blocked every hour. We tried contacting Office365 support but they said they cannot help on outbound email spam settings as they do not have any control over the configurations. I spend more than an hour on the phone with the support person and at the end was asked to send 5 sample emails to not_junk@office365microsoft.com and wait for 48 hours. I told O365 support that each user who is blocked sends around 100 emails of which all of them are getting flagged as either spam or phishing email, so sending random samples will not help. No spam or phishing filter settings have been changed since months now so I can only think on some backend updates done by O365 team for tightening the spam filters.
I am not sure whom to contact or escalate this case now so I am posting it in this group to everyone expecting someone who might have experienced the same might help. Any help to resolve this issue will be much appreciated as our users are unable to send emails.
Thanks.
- Labels:
-
Exchange
-
Office 365
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 10 2019 10:42 AM
The issue seems quite strange. How did you know that MS Outbound servers are marking your emails as Spam. Secondly I hope your domain is still able to send emails to other domains, if yes... could you share a message header.. so that I can analyze it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 10 2019 11:13 AM
Hi@Robin Nishad ,
We have edited the default Outgoing Spam rule to copy messages flagged as spam to one of our internal email addresses. I have pasted the header from one such email (apparently we receive almost every outgoing email now) as requested. As you will notice that the Spam Confidence Level is set to 5 by Microsoft and the Phishing Level to 8 for this outgoing email from Office365. We do have even have 2FA enabled for most users and never had any issue till yesterday.
Received: from AM6PR0602MB3589.eurprd06.prod.outlook.com
(2603:10a6:208:aa::49) by AM0PR0602MB3585.eurprd06.prod.outlook.com with
HTTPS via AM0PR06CA0072.EURPRD06.PROD.OUTLOOK.COM; Wed, 10 Apr 2019 17:13:40
+0000
Received: from VI1PR0601CA0005.eurprd06.prod.outlook.com
(2603:10a6:800:1e::15) by AM6PR0602MB3589.eurprd06.prod.outlook.com
(2603:10a6:209:e::26) with Microsoft SMTP Server (version=TLS1_2,
cipher=TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384) id 15.20.1771.19; Wed, 10 Apr
2019 17:13:39 +0000
Received: from VE1EUR01FT025.eop-EUR01.prod.protection.outlook.com
(2a01:111:f400:7e01::209) by VI1PR0601CA0005.outlook.office365.com
(2603:10a6:800:1e::15) with Microsoft SMTP Server (version=TLS1_2,
cipher=TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384) id 15.20.1792.14 via Frontend
Transport; Wed, 10 Apr 2019 17:13:39 +0000
Received: from EUR01-HE1-obe.outbound.protection.outlook.com (52.101.129.90)
by VE1EUR01FT025.mail.protection.outlook.com (10.152.2.232) with Microsoft
SMTP Server (version=TLS1_2, cipher=TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384) id
15.20.1771.16 via Frontend Transport; Wed, 10 Apr 2019 17:13:38 +0000
Received: from DB5EUR01FT040.eop-EUR01.prod.protection.outlook.com
(10.152.4.56) by DB5EUR01TH003.eop-EUR01.prod.protection.outlook.com
(10.152.4.138) with Microsoft SMTP Server (version=TLS1_2,
cipher=TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384) id 15.20.1750.16; Wed, 10 Apr
2019 17:10:53 +0000
Received: from EUR02-AM5-obe.outbound.protection.outlook.com (52.101.131.59)
by DB5EUR01FT040.mail.protection.outlook.com (10.152.5.25) with Microsoft
SMTP Server (version=TLS1_2, cipher=TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384) id
15.20.1771.16 via Frontend Transport; Wed, 10 Apr 2019 17:10:53 +0000
Authentication-Results: spf=none (sender IP is )
smtp.mailfrom=anna.mandia@gmsuae.com;
Received: from AM0PR0602MB3554.eurprd06.prod.outlook.com (52.133.46.17) by
AM0PR0602MB3523.eurprd06.prod.outlook.com (52.133.49.30) with Microsoft SMTP
Server (version=TLS1_2, cipher=TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384) id
15.20.1792.14; Wed, 10 Apr 2019 17:10:45 +0000
Received: from AM0PR0602MB3554.eurprd06.prod.outlook.com
([fe80::9162:6e5e:65c1:9944]) by AM0PR0602MB3554.eurprd06.prod.outlook.com
([fe80::9162:6e5e:65c1:9944%6]) with mapi id 15.20.1771.014; Wed, 10 Apr 2019
17:10:44 +0000
Content-Type: application/ms-tnef; name="winmail.dat"
Content-Transfer-Encoding: binary
From: Anna Mandia <anna.mandia@gmsuae.com>
To: Calum Berkley <calumberkley@aol.com>, "reservations@milansuites.com.sa"
<reservations@milansuites.com.sa>, "ayman@milansuites.com.sa"
<ayman@milansuites.com.sa>, IBIS Abu Dhabi Gate FO3 <H6949-FO3@accor.com>,
NOVOTEL Abu Dhabi Gate RE1 <H6948-RE1@accor.com>
CC: Paula Cercel <paula.cercel@gmsuae.com>, William Escondo
<william.escondo@gmsuae.com>, Amit Dagar <amit.dagar@gmsuae.com>
Subject: FW: Calum Berkley/Sharqi/12 Apr [Email Ref. #1457448]
Thread-Topic: Calum Berkley/Sharqi/12 Apr [Email Ref. #1457448]
Thread-Index: AQHU7g3sNf9KY9rzwEKdxrIlBbZyQaYySW2+gAAUiICAAtK0IA==
Date: Wed, 10 Apr 2019 17:10:44 +0000
Message-ID: <AM0PR0602MB35543E59377335E66B1F11119D2E0@AM0PR0602MB3554.eurprd06.prod.outlook.com>
References: <AM0PR0602MB35549FA31C962DC1097B472A9D2C0@AM0PR0602MB3554.eurprd06.prod.outlook.com>
<AM0PR0602MB3554B2DF88EFB2AD15FCC0699D2C0@AM0PR0602MB3554.eurprd06.prod.outlook.com>
<46AED3F05A1011E9B957005056BF25F3@focalscope.com>
In-Reply-To: <46AED3F05A1011E9B957005056BF25F3@focalscope.com>
Accept-Language: en-GB, en-US
Content-Language: en-US
X-MS-Has-Attach: yes
X-MS-Exchange-Organization-SCL: 5
X-MS-TNEF-Correlator: <AM0PR0602MB35543E59377335E66B1F11119D2E0@AM0PR0602MB3554.eurprd06.prod.outlook.com>
MIME-Version: 1.0
X-MS-Exchange-Organization-MessageDirectionality: Originating
X-MS-Exchange-Organization-AuthSource: AM0PR0602MB3554.eurprd06.prod.outlook.com
X-MS-Exchange-Organization-AuthAs: Internal
X-MS-Exchange-Organization-AuthMechanism: 04
X-Originating-IP: [217.164.74.77]
X-MS-Exchange-Organization-Network-Message-Id: 1516fec6-bb59-4dad-acf3-08d6bdd77816
X-MS-PublicTrafficType: Email
Return-Path: anna.mandia@gmsuae.com
X-MS-Exchange-Organization-ExpirationStartTime: 10 Apr 2019 17:10:45.0518
(UTC)
X-MS-Exchange-Organization-ExpirationStartTimeReason: OriginalSubmit
X-MS-Exchange-Organization-ExpirationInterval: 2:00:00:00.0000000
X-MS-Exchange-Organization-ExpirationIntervalReason: OriginalSubmit
X-MS-Office365-Filtering-Correlation-Id: 1516fec6-bb59-4dad-acf3-08d6bdd77816
X-Microsoft-Antispam: BCL:0;PCL:0;RULEID:(2390118)(7020095)(4652040)(8989299)(4534185)(4627221)(201703031133081)(201702281549075)(8990200)(5600139)(711020)(4605104)(2017052603328)(49563074)(7193020);SRVR:AM0PR0602MB3523;BCL:0;PCL:8;RULEID:(3031054)(100001)(3032054)(3034054);SRVR:DB5EUR01TH003;
X-MS-TrafficTypeDiagnostic:
AM0PR0602MB3523:|AM0PR0602MB3523:|DB5EUR01TH003:|DB5EUR01TH003:|DB5EUR01TH003:|DB5EUR01TH003:|DB5EUR01TH003:|DB5EUR01TH003:|DB5EUR01TH003:|DB5EUR01TH003:|DB5EUR01TH003:|DB5EUR01TH003:|DB5EUR01TH003:|DB5EUR01TH003:|AM6PR0602MB3589:
X-MS-Exchange-PUrlCount: 3
X-Microsoft-Antispam-PRVS: <AM0PR0602MB352364002DE092CC23D543D69D2E0@AM0PR0602MB3523.eurprd06.prod.outlook.com>
X-Forefront-PRVS: 00032065B2
X-Forefront-Antispam-Report: SFV:SPM;SFS:(10009020)(136003)(39850400004)(396003)(346002)(366004)(376002)(199004)(189003)(9686003)(3846002)(236005)(52536014)(76176011)(4326008)(606006)(66066001)(25786009)(107886003)(102836004)(53546011)(6506007)(26005)(186003)(11346002)(476003)(71190400001)(66574012)(71200400001)(6116002)(790700001)(68736007)(486006)(44832011)(33656002)(5660300002)(5024004)(446003)(14444005)(97736004)(256004)(81156014)(81166006)(2201001)(54906003)(8936002)(8676002)(508600001)(14454004)(110136005)(7696005)(53946003)(2906002)(6306002)(2473003)(413944005)(99286004)(99936001)(316002)(229853002)(74316002)(7736002)(2501003)(105586002)(6436002)(733005)(106356001)(53936002)(55016002)(86362001)(54556002)(54896002)(59010400001);DIR:OUT;SFP:1501;SCL:5;SRVR:AM0PR0602MB3523;H:AM0PR0602MB3554.eurprd06.prod.outlook.com;FPR:;SPF:None;LANG:en;PTR:InfoNoRecords;A:1;MX:1;
Received-SPF: None (protection.outlook.com: gmsuae.com does not designate
permitted sender hosts)
X-MS-Exchange-Organization-ExpirationInterval: 0:04:00:00.7865921
X-MS-Exchange-Organization-ExpirationIntervalReason: SpamEngine
X-MS-Exchange-AtpMessageProperties: sap=1;slp=1;
X-MS-Exchange-Transport-CrossTenantHeadersStamped: AM0PR0602MB3523
X-MS-Exchange-Transport-CrossTenantHeadersStripped: DB5EUR01FT040.eop-EUR01.prod.protection.outlook.com
X-MS-Exchange-Organization-ACSExecutionContext: 04/10/2019 17:10:53;04/10/2019
17:13:38;{"SubmissionInfo":{"SubmissionToken":"PFRva2VuIFRva2VuVHlwZT0iU3VibWlzc2lvblRva2VuIiBJZD0iYjAyN2FkZWYtYjM1Yi1lOTExLWIwNzYtOWNkYzcxNTBlYjYyIiBSb2xlPSJTdWJtaXR0ZXIiIEVuZHBvaW50PSJodHRwczovL0hFMVNFVTA0VFAxMDUuZW9wLXNldTA0LnByb2QucHJvdGVjdGlvbi5vdXRsb29rLmNvbS9zb25hcmFwaS8iIFNpZ25hdHVyZT0iRmg4aFlxVGszUkhDTDQ4S0NpK1haNEFWNlRBPSIgLz4","Identity":"9960c8bc-7008-4852-a218-286be1ec6672"}};SC;S;0;04/10/2019
17:13:24;0|0|0|1|;
X-EOPAttributedMessage: 0
X-OriginatorOrg: gmsuae.com
X-MS-Exchange-Organization-SafeAttachmentProcessing:
X-MS-Exchange-Transport-EndToEndLatency: 00:02:55.2749479
X-MS-Exchange-Processed-By-BccFoldering: 15.20.1771.000
X-Microsoft-Antispam-Mailbox-Delivery:
ucf:0;jmr:0;ex:0;auth:0;dest:I;ENG:(20160513016)(750119)(520011016)(706158)(944506303)(944610083);
X-Microsoft-Antispam-Message-Info:
DAPEWkLz3LKrnttMLdcI98FZqSXR7MZz4OAxsAZSkiO6Gu6jwVcQ8UY2dnhlI4Er0hSFzRtjFw1ahUoSQuNcF8JkUWZwJKBsg22Xejcz94WydHdk/2gZ33UC9IjWff1BjQEkPJAxGAHyXXRwia3hCxqrFuM4MkRlX3wyAl+K67mNK5XXrlbmJta1I4mm2IRumAgmngf4loOkKGF7eNyYO9VBQEImTYKVEimogNG/Gb1ZyvX+/Kxix7uGzdtR/9HQvQ4cvuIkEjoVIivTdX8XgPt0TH6nwFdG/kzjpCD4ufYIAb3HxGjsgrIgX7pGgKRgzg6xVOdyFiihOo9Rr1+rxrU2/FdhsIbuKHPJM66JC02Yld6Fot5bPkNgOSDDYBicG0HxUwsbDMHbuE81ik85yTQrDCAx0lzwH4X6pWWIKzrCpVkclW79BujtKE1oPIb5WoPVj7n+WiNIWDC59kEGqYYjX3BArXj3ohDEkRI2NMmfZMt2Sy6h0i6fPpcL/YngqxwQ2+pfxDnWFJOCt4wNregwhu4gev2eR7CtduQohvInuqvP/rO62VOcX96b5HV5kmnTFZlQwr2OnnHNEKI85GXpIn9qvwxwxlS6g8TFl0EWpN4XRc0F0E8LA+k53Qmj/Zq64uvKj55GIRE9AF4YmodBgxemEV6NdlF8t3xaM2FVEVC3pXGFthJ10VjUWzi2k5oeJSFYVvmHHleLS61IiPLiwic14OtMTvh8TgKTInvvcOuhxFY6SlQLcrIMEgjsF1KaqPtTbkyrdu+yY+raGdWajsnFM6lM7GETgaX/f90=
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 10 2019 11:49 AM - edited Apr 10 2019 11:50 AM
social.technet.microsoft. com/wiki/contents/articles/36402.exchange-online-troubleshooting-high-risk-delivery-pool.aspx
Try to delist the IP on sender.office. com
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 10 2019 12:05 PM
I noticed in the Message Header -
| Received-SPF | None (protection.outlook.com: gmsuae.com does not designate permitted sender hosts) |
So would suggest to check if the sender domain is added in the allowed domain settings in Security and Compliance center.
1. Sign in to O365 Admin Portal
2. Navigate to Security & Compliance center > Threat management > Policy.
3. Find Anti-spam, open it. Expend Allow lists. Add the sender’s domain to the Allow domain setting.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 10 2019 12:40 PM
Hi@Robin Nishad ,
Thanks for the suggestion. We already have the domain added in the Allow list of Anti-Spam policy.
Could it be that the domain is showing as SPF not designated because it is still an internal email within Office365 servers ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 10 2019 12:52 PM
if the Domain is added in the Allow list, then I would suggest to submit the message to MS and let them know that it is not Spam. I know & understand that you are already working with MS on this however I would like you to refer to the steps given in the below article....
(Submit messages that were tagged as junk but should have been allowed through)
Secondly the proof that MS Servers are marking your email as Spam is that in the header - Anti Spam Report - It has SFV-SPM that means the email is marked as Spam because of the EOP Spam filters.
Reference Article - https://docs.microsoft.com/en-us/office365/SecurityCompliance/prevent-email-from-being-marked-as-spa...
Moreover do check if the emails that you are sending has any HTML Signatures or they are simple text.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 11 2019 11:35 AM - edited Apr 11 2019 11:55 AM
@ALV_Work We got exactly the same problem yesterday, I opened a ticket but Microsoft seems to have no clue about what happened.
We worked on it a while and this is what we could figure out about our case :
- It started around 7am CET and ended around 8pm CET
- It has nothing to do with SPF or whatever
- EOP was giving a SFV:SPM SCL:5 to outbound emails ONLY IF they were replies or forwards to external email addresses, so they were using the High Risk Delivery Pool and we were getting a BCC in our IT mailbox as our Outbound spam Policy specifies it. I can see in your header that it was the same for you : DIR:OUT;SFP:1501;SCL:5
- When an external person was answering one on these emails they were coming back with SFV:SPM and CAT:PHSH, so we got PLENTY of emails yesterday ending up in junk folder
- Every Outbound Spam BCC in our IT mailbox arrived twice, the second time with a huge delay (6+ hours), and message stayed in "Getting Status" for very long time in traces, maybe because they were going through the High Risk Pool.
We didn't make any changes in our SPF or policies, it just randomly happened and ended.
I'm still waiting for an explanation from Microsoft.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
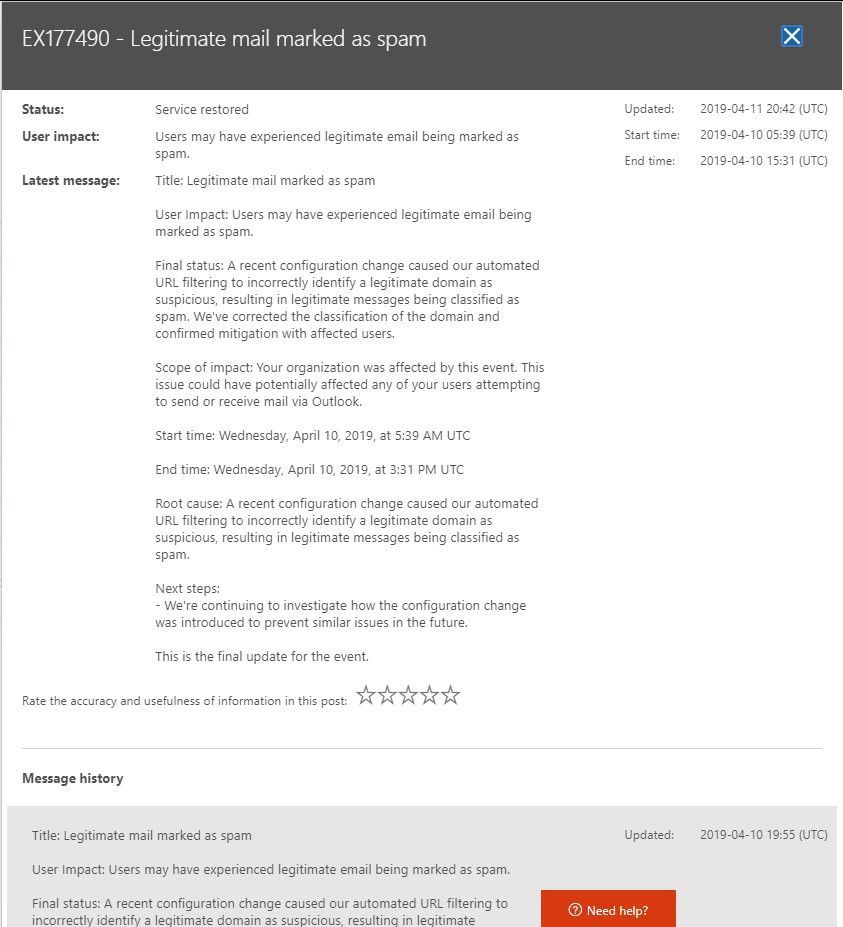
Apr 12 2019 12:05 AM
Solution
You might want to read the following article on the "health" tab in the office portal...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 12 2019 12:30 AM - edited Apr 12 2019 12:32 AM
@Rafmoerkens Thanks for this, It doesn't appear in my portal, I only have the "EX176985 - Can't see message traces" ...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 12 2019 12:33 AM
@Philippe_RAYNAUD: you might have been "out of scope"? ;)
@ALV_Work: please see above as you were the one that had the issue :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 12 2019 01:02 AM - edited Apr 12 2019 01:02 AM
Hi@Rafmoerkens @Philippe_RAYNAUD ,
Negative. Had a call from O365 support guy(not direct MS staff) and he has confirmed that my domain is having a service incident but I still donot see anything on my office portal. But looks like the issue is not happening now.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 12 2019 01:08 AM
Hi @@Philippe_RAYNAUD ,
All the scenarios mentioned by you is the same for me too. Got a lot of emails tagged as PHISH by AntiSpam policy and all went into quarantine due to our Antispam settings. Had to release them manually to the users. Also we got a lot of duplicate emails send as BCC to our IT email address since outgoing emails where getting tagged as SPAM. But now the issue seems to be have stopped. Looks like MS Team has reverted the changes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 12 2019 01:30 AM
@Rafmoerkens Their article is weird though, I don't understand what this has to do with "URL filtering"! Happened with every single message.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 12 2019 10:50 AM
Hi @Philippe_RAYNAUD @Rafmoerkens
May be something to do with links in signature of outgoing emails.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 12 2019 03:29 PM
@ALV_Work Nope we tried with blank messages was the same, I think we will never know what really happened :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 16 2019 05:32 AM
We are facing same issues from past week. Did create a ticket with MS and is still being worked on.
We didn't make any recent changes to any of our policies and wondering what is the reason behind it. Its been a week that we are exchanging mail headers and extended message traces and didn't reach to isolate the issue yet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 16 2019 05:58 AM
Hi @Sujesh1415 ,
Only Microsoft Team can resolve this issue. It mostly due to an issue at their servers which tags outgoing emails as spam. This affects not everyone i guess just random tenants.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 23 2020 09:17 AM - edited Jan 23 2020 09:26 AM
I'm having a similar issue with a client who has Office 365 for email.
Their domain name was categorized as CAT:HPHISH due to their website being hacked. Once cleaned up they started having emails being quarantined. They put their domain name in their signature. So any customers they emailed with Office 365 wouldn't get the email, it would be quarantined. When a customer who wasn't on Office 365 got the email and replied, the client wouldn't get the email.
We've reached out to Microsoft Support, however, they're unable to understand what needs to happen. And there is no system in-place to change/remove domain names from this categorization. Even though they have https://sender.office.com for de-listing IP addresses, there is no way to submit domain names.
Other vendors like PaloAlto, FortiNET and Sohpos provide the means to submit evidence for delisting domain names categorized as Phishing or Spam.
EDIT: The only method I see to report the domain name as a false positive or have the category changed or removed is through the Office 365 Protection Portal under the “Quarauntine Queue", by clicking “Submit Message” with no information on where it’s going or if I will get notified if any action was taken.
The other method is in a Microsoft article https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/submit-spam-non-spam-and... which states “Use the same procedure as described in the "Use email to submit junk (spam) or phishing scam messages to Microsoft ," but send the message to not_junk@office365.microsoft.com.”
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 23 2020 02:22 PM
We are having the exact same problem. Tomorrow will be our 3rd day of being mostly down and working with 0365 who can't figure out the problem or even understand that it is bigger than analyzing a couple email headers.
Is there a way to get in contact with higher tier support that has more to say than " tell your recipients to whitelist you."?
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 12 2019 12:05 AM
Solution
You might want to read the following article on the "health" tab in the office portal...