- Home
- Microsoft 365
- Microsoft 365
- DLP policies take too long to tag new files uploaded to OneDrive
DLP policies take too long to tag new files uploaded to OneDrive
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Jun 04 2020
04:39 PM
- last edited on
Feb 01 2023
01:18 PM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 04 2020
04:39 PM
- last edited on
Feb 01 2023
01:18 PM
by
TechCommunityAP
I work at a financial institution (Bank) and securing information is critical. We are trying to apply DLP policies for when employees begin sharing with external users.
We are running tests to see how responsive is the system and one thing that we saw that could potentially scrap the whole idea of sharing with externals is the fact that DLPs take too long to tag a file with more than 50 SSNs.
During the time that it takes for the DLP policies to kick in, the damage is done. We tested this and from the external's side, they were able to access the list of 50 SSNs without an issue. After the DLP kicks in, the external user no longer has access to the file, but again...the damage is done by this time.
So if an employee finds out about this, they can potentially leak a lot of high sensitive documents and the external can download them within the time limit without issues.
I know there was an older thread from 2017 which had the same issue and the answers were not really convincing. Just wanted to know what exactly does Microsoft recommend when it comes to situations like these?
Right now we have a need that unfortunately MS cannot provide due to limitations of the features and we use O365 for everything.
Any ideas are welcomed!
Was this issue addressed?
- Labels:
-
Compliance
-
Office 365
-
OneDrive
-
Security
-
SharePoint
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 05 2020 12:06 AM
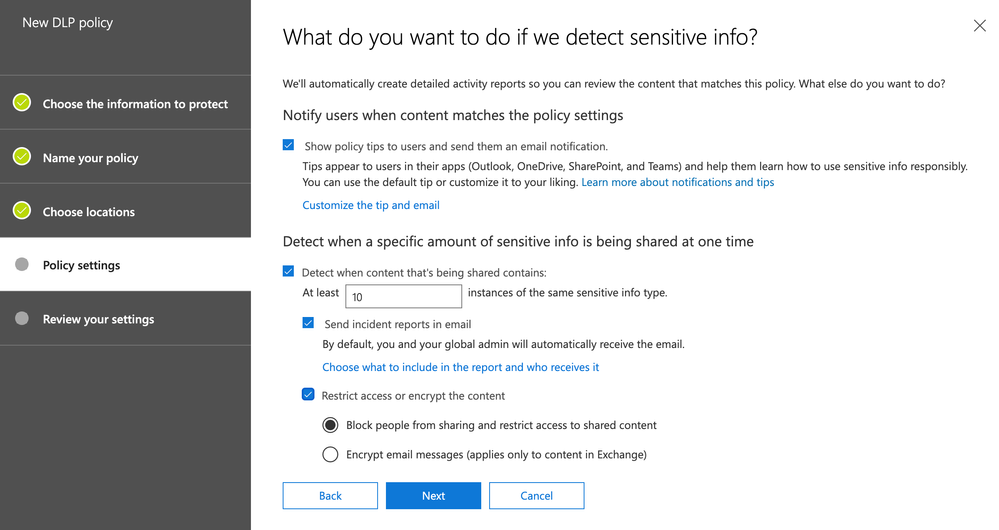
Hi, would a DLP policy setup as below not achieve what you want? It will show the users policy tips when there is a match, if there are more that 10 SSN's in the document or email it will trigger the policy and block people from sharing.
Is this along the lines of what you are trying to setup?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 05 2020 11:40 AM
Well we are using a default DLP that Office 365 offers which is the GLBA DLP. That one has two rules. one for low volume and one for high volume. They work fine.
The issue here is that it just take too long for the DLP policy to identify a newly uploaded sensitive document in order to tag it and restrict external access to it.
This means that if I (as employee) uploaded a list of 50 SSNs in an Excel to my OneDrive, then shared it to an external user (my own gmail for example) then I can access that content from my gmail within the time limit before the DLP finally tags the document.
I can have within seconds lists of SSNs from the bank's customers which is a big deal in terms of cybersecurity!
So I don't know what can be done to lower the speed at which the DLP goes in identifying sensitive documents.
This is just with 1 external user, imagine if hundreds of users were doing this at the same time, I don't know how long the DLP can last before tagging
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 06 2020 10:52 AM
I don't know of any way that it is possible to manipulate DLP in the way you are suggesting I believe. I am near enough certain that this is not something that is possible.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 10 2020 10:35 PM
This will mark files as sensitive immediately at upload and only remove DLP once deemed safe. It doesn’t speed up processing as now you may need to wait in order to share. But it will prevent data leakage from occurring before DLP has a chance to process the files.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 10 2020 11:24 PM
Oh now that it nice. Not something I had heard of yet but will definitely be checking it out.
@Odenkaz - if this does what you are looking to achieve (which I think it will), please can you mark @Ben Steginks reply as the best response in order that others can easily find this solution. ![]()
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 12 2020 06:53 AM - edited Jun 12 2020 06:59 AM
I tested it out and the external user was still able to see the contents of the document.
I ran this cmd from the linked documentation you posted:
Set-SPOTenant -MarkNewFilesSensitiveByDefault BlockExternalSharing
Update: Re-read the documentation and this solution doesn't cover OneDrive yet.
"Note
This cmdlet applies to newly added files in all SharePoint sites. It doesn't block sharing if an existing file is changed.
The cmdlet doesn't cover files added to OneDrive. We're working to bring this functionality to OneDrive."
My issue is strictly with OneDrive external collaboration. We do not have SharePoint enabled for external sharing yet.
Is there an estimate of how long this new cmd will be able to cover OneDrive?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 12 2020 08:12 AM
@Odenkazgot it. As for OneDrive, I'm not sure on a time frame there. I haven't seen anythign on this fucntionality being extedned into OneDrive as well unfortuantely. If I can get some information or can find a time frame I'll let you know.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 12 2020 11:02 AM
Greatly appreciated! hopefully it's not far too long!
Will keep myself tuned in to this thread for any updates
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 17 2023 11:36 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 17 2023 11:39 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 18 2023 07:23 PM
Set-SPOTenant -MarkNewFilesSensitiveByDefault BlockExternalSharing