- Home
- Microsoft 365
- Identity & Authentication
- MFA Shows Disabled, But Being Used
MFA Shows Disabled, But Being Used
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 17 2020 03:43 PM - last edited on Nov 09 2023 11:10 AM by
When I visit Azure Active Directory -> Users -> Multi-Factor Authentication, our initial accounts show "Multi-Factor Auth Status" as "Disabled", but we are seeing MFA prompts. I find it confusing that something shows "disabled" that is really turned on somehow??? Is there more than one type of MFA?
We just received a trial for G1 as part of building a use case for moving to Office 365. I setup the tenant space by confirming our identity and I am a Global Administrator. I was prompted to setup MFA on my second logon, but I don't recall being offered any option other than text message. My understanding is that I had to turn on MFA for our accounts so I just setup SMS to get logged on the second time.
- Labels:
-
Authentication
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 18 2020 03:33 AM
1. Go to https://portal.azure.com
2. Use the search bar on the upper middle part of the page and search of "Azure Active Directory".
3. Under Azure Active Directory, search for Properties on the left-hand panel. It is in-between of User Settings and Security.
4. Under the Properties, click on Manage Security defaults.
5. Under the Enable Security defaults, toggle it to NO.
6. Wait for few minutes for propagation then try to sign-in using InPrivate or Incognito.
Let me know what will happen.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 18 2020 08:12 AM
Yes, our tenant space is setup to use the security defaults as mentioned on this page https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/concept-fundamentals-security-d.... If you turn off Security Defaults, the multi-factor authentication page still shows that no accounts have MFA setup, even though they are setup for MFA. It really seems like when Security Defaults was implemented they must have setup things to ignore the existing MFA settings altogether. I would really like to see that MFA is turned on for a user whether using the fancy Conditional Access that I am reading about or Security Defaults.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 18 2020 10:28 AM
Have you turned the security defaults off now? If so, it may take a while for the settings to take effect throughout your tenant.
Once you can verify that these settings are no longer applying, I'd recommend using Conditional Access Policies for MFA instead of relying on the Security defaults as these apply blanket settings. You can find this at https://portal.azure.com under Azure Active Directory > Security > Conditional Access.
You will see some Baseline policies there. Don't enable those as they also apply blanket settings, and they are due to be deprecated. I'd highly suggest you create your own CA Policies. I'd recommend at the minimum a policy to require MFA for all privileged admin roles, but don't forget to exclude your permanent break glass account(s) from this policy as you don't want to get locked out.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 18 2020 10:30 AM
This MFA page (often referred to as Office 365 MFA), is the old way of implementing MFA.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 19 2020 07:26 AM
@Germaum Thankyou this resolved my issue after wasting way too much time trying to find the cause.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 10 2020 08:53 AM
@Germaum Sorry to bring a dead thread back but we're having a similar issue with Security Defaults disabled. Though it's not every user. We're currently tracking one high profile user. Our tenant responds that MFA is disabled when checked via powershell. (The script works properly for other users so we know the script is good). The users still gets MFA prompts and his account allows for additional security settings even though the MFA is "Disabled".
Any clues as to why this might happen to a small number of users and why it may happen even though default security settings are/have been off?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 10 2020 08:57 AM
Office 365
If your tenant was created on or after October 22, 2019, it is possible security defaults are already enabled in your tenant. In an effort to protect all of our users, security defaults is being rolled out to all new tenants created. (referenced from https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/concept-fundamentals-security-d...)
Try this:
1. Go to https://portal.azure.com
2. Use the search bar on the upper middle part of the page and search of "Azure Active Directory".
3. Under Azure Active Directory, search for Properties on the left-hand panel. It is in-between of User Settings and Security.
4. Under the Properties, click on Manage Security defaults.
5. Under the Enable Security defaults, toggle it to NO.
6. Wait for few minutes for propagation then try to sign-in using InPrivate or Incognito.
(referenced from https://techcommunity.microsoft.com/t5/identity-authentication/mfa-shows-disabled-but-being-used/m-p...)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 10 2020 09:00 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 21 2020 09:41 PM
@wannapolkallama Any luck with this. I have a similar situation. Everything is turned off, yet still getting the MFA prompt
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 10 2021 10:16 AM
Hi,
I had the same problem. I already had disabled the security default settings.
I solved the problem with deleting the saved information.
This means:
- Go to the "Multi-Factor authentication"-Page (https://account.activedirectory.windowsazure.com/UserManagement/MultifactorVerification.aspx?BrandCo...)
- Select the user and click "Manage user settings" on the link on the right side
- In the new popup, select "Require selected users to provide contact methods again". This will remove the saved settings, also the MFA-Settings of the user.
- After this, the user can login, but has to provide the security info (phone and alternative mail address) again.
Afterwards, the login in a incognito window was possible without asking for MFA.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 27 2021 09:47 PM
We are having this issue with a new tenant.
All users have MFA Disabled and Enable Security defaults are also set to No, yet as I am adding each account to Access work or school on new PC I get prompted to setup MFA. I just click Next and then close the window. It's a pain, but the account is successfully added and credentials are used to open O365 etc.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 28 2021 03:36 AM - edited Apr 28 2021 03:39 AM
This is all down to a new and ill-conceived UI from Microsoft. They've basically combined MFA setup with account recovery setup. Prior to this change, if you had self-service password reset enabled, on first login users would be prompted to setup a recovery phone and email. If MFA was enabled, they'd be prompted to setup MFA.
The combined approach is highly confusing when not wanting MFA. It still allows a user to setup MFA even when it's disabled on the account in Azure. Indeed it's designed to make you think you have to set it up. Just more nonsense from unskilled product managers and developers with little experience of the real world and zero common sense.
Same with the Security Defaults. These force use of MFA for all accounts, despite Microsoft's own recommendation to have at least one GA account not using MFA in case of MFA issues. Indeed a non-MFA GA account is needed for hybrid operation as well as for any 3rd party services that need access to the 365 tenant.
Anyhow, the solution is to ignore the initial presentation of the setup. For option 1, select Phone instead of Authenticator App from the dropdown. Then complete the phone verification as it used to be done. Then select Email for option 2 and complete that. Account is now setup with password reset info needed but without MFA enabled.
That still leaves the issue that, if the user chose to enable MFA during initial account setup, this won't reflect in AAD. That still shows MFA as disabled!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 18 2021 10:20 AM
What we found is that you can enable MFA through MyAccount.Microsoft.com > Security Info > Update Info. If it is enable here, the Azure portal continues to show that it is not enabled yet if functions. If set up this way, then changing it in Azure has virtually no effect (except your powershell reporting will be correct again).
Let me know if I am wrong on any points, but it seems to hold true for us.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 02 2022 09:49 AM
If anyone sees this again, log into Azure, search for conditional access to bring up that conditional access interface, and see if you have a conditional access policy applied. It likely will have one intitled "Require MFA for Everyone." If that policy is in the list of conditional access polices listed, delete it. Problem solved. Or at least in my case. Whether or not you have MFA enabled at the user level is superseded by this policy, and it won't even show MFA as enabled at the user level even thought this policy is forcing it. Again this was the case for me. Milage may vary. @Eddie78723
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 22 2022 11:33 AM
Doesn't matter what the User's MFA settings say, MFA has to be set up for the user in order to use Self Service Password Reset. Requiring the user to register when signing in will trigger that registration prompt if they don't have MFA set up.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 19 2022 03:15 AM
@Eddie78723 it is sorry to hit this point again. Even the users were set Disable in MFA set up but when user login, it still requires to MFA. Some users require to login without the MFA. How can we set it? I did both in Properties and Condition Access but it seemed not work. Thank you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 12 2022 01:46 AM
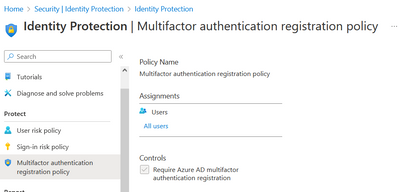
I'm really sorry to flog a dead thread about this but I haven't seen anyone mentioning the MFA Registration Policy settings sitting under ID Protection
I'm unable to edit this, probably because I haven't subscribed to their Premium AD license and therefore am not permitted to make the necessary changes here.
I believe this is the root of the notifications but as I said, I'm not able to make changes here.
I've gone through all the comments here, security defaults are set to no, no CA policy created and this MFA Reg Pol is the only place I can see the policy being enabled.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 14 2022 02:14 PM
So after a few hours on the phone with Microsoft it was discovered that Self Service is the culprit. It is enabled for all users once you switch it to "None" it will not trigger MFA and allow users to logon without MFA challenge when MFA itself is disabled.