- Home
- Healthcare and Life Sciences
- Healthcare and Life Sciences Blog
- Microsoft Purview - Paint By Numbers Series (Part 2e) – Using Multiple Sensitivity Labels
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Before we start, please not that if you want to see a table of contents for all the sections of this blog and their various Purview topics, you can locate the in the following link:
Microsoft Purview- Paint By Numbers Series (Part 0) - Overview - Microsoft Tech Community
Disclaimer
This document is not meant to replace any official documentation, including those found at docs.microsoft.com. Those documents are continually updated and maintained by Microsoft Corporation. If there is a discrepancy between this document and what you find in the Compliance User Interface (UI) or inside of a reference in docs.microsoft.com, you should always defer to that official documentation and contact your Microsoft Account team as needed. Links to the docs.microsoft.com data will be referenced both in the document steps as well as in the appendix.
All of the following steps should be done with test data, and where possible, testing should be performed in a test environment. Testing should never be performed against production data.
Target Audience
The Information Protection section of this blog series is aimed at Security and Compliance officers who need to properly label data, encrypt it where needed.
Document Scope
This document is meant to guide an administrator who is “net new” to Microsoft E5 Compliance through.
We will be discussing multiple Sensitivity Labels and how they work.
- How multiple Sensitivity labels work together
- Examples of how to multiple Sensitivity labels can be laid out.
It is presumed that you already have a Sensitive Information Type that you want to use in your Information Protection policy. For the purposes of this document, I will use a copy of the U.S. Social Security Number (SSN) called “U.S. SSN – Numbers Only” that I created in Part 1 of this blog series.
It is presumed that you already have multiple Sensitivity labels created for your testing.
This document is only meant to be an introduction to the topic of multiple Sensitivity labels. Always refer back to official Microsoft documentation or your Microsoft account team for the latest information.
Out-of-Scope
This document does not cover any other aspect of Microsoft E5 Compliance, including:
- Sensitive Information Types
- Exact Data Matching
- Data Protection Loss (DLP) for Exchange, OneDrive, Devices
- Microsoft Cloud App Security (MCAS)
- Records Management (retention and disposal)
- Overview of Advanced eDiscovery (AeD)
- Reports and Analytics available in of Advanced eDiscovery (AeD)
- Insider Risk Management
- Privacy Management
It is presumed that you have a pre-existing of understanding of what Microsoft E5 Compliance does and how to navigate the User Interface (UI).
It is also presumed you are using an existing Information Types (SIT) or an Exact Data Match (EDM) that you have created for your testing.
We will not be covering the auto-labeling of data at rest. That will be covered in another blog post and those auto-labeling policies should not be done until after you have locked down your Sensitivity labeling of all “net new” data.
If you wish to set up and test any of the other aspects of Microsoft E5 Compliance, please refer to Part 1 of this blog series (listed in the link below) for the latest entries to this blog. That webpage will be updated with any new walk throughs or Compliance relevant information, as time allows.
Overview of Document
- How multiple Sensitivity labels work together
- Examples of how to multiple Sensitivity labels can be laid out.
Use Case
- Using multiple Sensitivity labels in a single tenant
Definitions
- Sensitivity Label – a metadata tag
- Publish Label – making the metadata tag available to your tenant
- Policy – The monitoring and applying of Sensitivity labels through the Microsoft tenant
Notes
- How are conflicts resolved when it comes to Sensitivity labels?
- The best way to understand this is the official chart and link below
Pre-requisites
- You have read Part 2 of this blog series
- You have created multiple Sensitivity labels for your testing.
Overview of Prioritization of Multiple Sensitivity Labels
- Once you have published your Sensitivity label you will prioritize the policies based on what is the least restrictive label versus the most restrictive label.
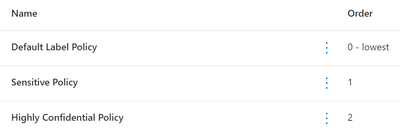
- What to know – In the Policies tab, the policy with the lowest “Order” number is listed at the top and the highest at the bottom. Here is a screenshot from the Compliance Portal that explains this in a different way.
- How to apply this –
- You should place your lowest priority Sensitivity label policy at the top of the list of Sensitivity labels policies. This will create a baseline of label.
- You should then place your highest priority Sensitivity label policy at the bottom of the list.
- Tip #1 – The trick is to remember that the higher the number in the “Order” column the stricter the label. This is a challenge because the order starts with 0 at the top and then as you go down, the “order” becomes greater.
- Tip #2 – Place your Labels in the same order as your Policies so that no matter which tab you are on, you will know the priority of your labels
- Example, the Sensitivity label policy positioned at Order #2 will be a more restrictive label than the Sensitivity label policy with positioned at Order #1
- The following 3 examples will attempt to flesh this out.
Example #1 – 4 Sensitivity labels
Here is an example of how you might lay out 4 Sensitivity labels from the least restrictive to the most restrictive Sensitivity label.
Note – These applications labels will be based on which Sensitive Information Types (SITs) are associated with each. We will not be covering these at this time because we are presuming you have configured your labels previously.
Look at the following screenshot of 4 Sensitivity label policies and their order
- The chart below lays out how the order of these will affect the docuement
|
Order |
Label name |
Priority of Sensitivity Label policy |
|
0 |
Public Document Policy |
Least Restrictive |
|
1 |
Internal Document Policy |
Second Least Restrictive |
|
2 |
Secret Document Policy |
Second Most Restrictive |
|
3 |
Top Secret Document Policy |
Most Restrictive |
Example #2 – 3 labels with a one being a “Default” Sensitivity label
Here is an example of how you might lay out a “default” Sensitivity label policy and then layer on stricter Sensitivity labels policies based on the amount of Sensitive Information Types (SITs) found in a file/email.
Regard the following screenshot of 3 Sensitivity label policies and their order
- The Default Label policy above will be applied to all new files/emails by default.
- If the end user adds 1 piece of PHI data (ex. a social security number) to the file/email, then the “Sensitive” label will be applied.
- If the user adds 2 piece of PHI data (ex. a social security number and a credit card number) to the file/email, then the “Highly Confidential” label will be applied.
- The chart below shows how the Order column will map to both the label and the quantity of Sensitive Information Type (SIT) information in a file/email.
|
Order |
Label |
Numbers pieces of PHI data |
|
0 |
Default |
0 |
|
1 |
Sensitive |
1 |
|
2 |
Highly Confidential |
2 |
- Tip – you should never have more than 1 “default” Sensitivity label and it should always be set at an “Order” of 0 in your policy list. This is to avoid possible labeling conflicts of this particular type of label. See blog Part 2a tk for more information on “default” Sensitivity labels. Link is in the Appendix and Links below
Appendix and Links
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.