- Home
- Exchange
- Exchange Team Blog
- September 2020 Hybrid Configuration Wizard Update
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Today we are happy to announce an update to the Exchange Hybrid Configuration Wizard (HCW) which enables either a Full or Minimal Hybrid deployment from a single on-premises organization to more than one cloud tenant. Edit: Hybrid Modern Authentication (HMA) can now be configured for Hybrid deployment with multiple tenants. To configure HMA, use the steps mentioned here.
In this release we allow admins to enable Hybrid deployment with up to 5 tenants simultaneously.
Free/Busy configuration between tenants is not available by default. You can refer to this article for setting it up if you require it.
You can download the HCW version supporting this feature from aka.ms/hybridwizard.
Configuration Pre-Requisites
The updated version of Hybrid Configuration Wizard requires Exchange Server 2016, CU18 or higher or Exchange Server 2019, CU7 or higher to enable this functionality.
Identity
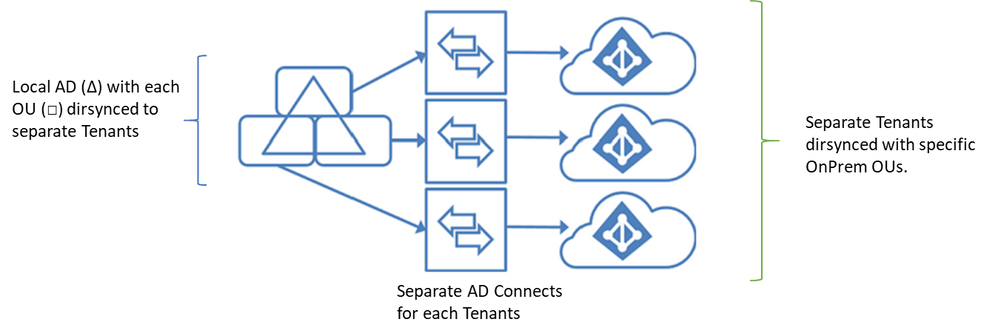
Users in the on-premises Active Directory must not be synchronized to more than one tenant, and so Azure AD Connect must be configured using the Domain/OU filtering option to filter users from your on-premises directory to ensure they appear only in a single online Exchange tenant.
You must also ensure that "Exchange Hybrid" checkbox is selected in Optional Features while configuring directory sync for each tenant. You’ll end up with a sync topology that will be similar to the following:
You can of course synchronize multiple on-premises OU’s to the same tenant, there are many ways to set this up based upon your local AD, but the hard rule is not to overlap the scope of these synchronization relationships, which will ensure on-premises users are associated with only one cloud tenant. (Don't cross the streams!)
For additional information about supported topologies for Azure AD Connect take a look at this page
Separate Certificate for each Send connector sending to each tenant
For proper email attribution to each tenant, make sure you are using separate certificate for each Send connector sending to each tenant. If same certificate is used, then the email to one tenant may attribute to the other tenant. The Certificate that will be used by a Send Connector is controlled by the TlsCertificateName parameter. To know more about message attribution, please refer to the following articles:
- (550 5.7.64 TenantAttribution; Relay Access Denied SMTP) error when users send mail externally in Of...
- Office 365 Message Attribution
SMTP Domains
Add all domains, whether custom tenant SMTP domains or tenant coexistence domains as Accepted Domains into your Exchange On-Premises Organization using the Exchange Control Panel (ECP) or Exchange PowerShell.
Create a separate Email Address Policy for each tenant/OU pair. Do this on the email address policy tab in ECP, create a new policy (name it descriptively, unlike our example below), then add the email address format you use and carefully choose the target recipient OU in request container for the tenant.
Running the Wizard
Now you are ready to run the wizard. On a domain joined machine install the HCW wizard just as you normally would. The credentials you provide for Exchange Online determine if you are adding a tenant or configuring an existing tenant.
When you run the HCW you can select either the Classic or Modern mode. If you choose the Modern option for any or all of the tenants, the Hybrid Agent must be installed on a domain joined machine or on an Exchange 2016 or 2019 server with the Mailbox role. Separate Agents are required for each tenant configured with Modern Hybrid as it’s not possible to install two different agents on the same server.
In you have two or more accepted domains for any particular online tenant you must choose the domain that you want to be configured for Autodiscover. This option will be presented to you while configuring the Hybrid Wizard on the Hybrid Domains page.
That’s it. You simply re-run the HCW for all the tenants you want configured for Hybrid.
Known Issues and Workarounds
There are two issues we want to call out just in case you hit them.
Issue: Creation of Remote User via ECP picks the last configured tenant domain for RemoteRoutingAddress attribute. This will affect free/busy discovery of users.
Workaround: Use a PowerShell cmdlet to create the remote users with the correct RemoteRoutingAddress or set the right RemoteRoutingAddress after creation of the remote mailbox.
New-RemoteMailbox -Name "Megan Bowen" -FirstName "Megan" -LastName "Bowen" -OnPremisesOrganizationalUnit "tailspintoys.com/T1" -UserPrincipalName "meganb@tailspintoys.com" -Password $password -ResetPasswordOnNextLogon $False -RemoteRoutingAddress "meganb@tailspintoys.mail.onmicrosoft.com"
Issue: While enabling remote archive for on-premises users using ECP it picks the last configured Tenant domain for ArchiveDomain attribute.
Workaround: Do not enable the remote archive property from ECP for on-premises users, use the following PowerShell cmdlet for this:
Enable-Mailbox -Identity "meganb" -RemoteArchive "True" -ArchiveDomain "tailspintoys.mail.onmicrosoft.com"
Summary
You can download the HCW version supporting this feature from aka.ms/hybridwizard.
We hope you enjoy this latest addition to the HCW. It’s been something we get asked about a lot, and we want to hear your feedback.
The Exchange Hybrid Configuration Wizard Team
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.