- Home
- Exchange
- Exchange Team Blog
- Basic Authentication Deprecation in Exchange Online – September 2022 Update
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
One month from today, we’re going to start to turn off basic auth for specific protocols in Exchange Online for customers who use them.
Since our first announcement nearly three years ago, we’ve seen millions of users move away from basic auth, and we’ve disabled it in millions of tenants to proactively protect them.
We’re not done yet though, and unfortunately usage isn’t yet at zero. Despite that, we will start to turn off basic auth for several protocols for tenants not previously disabled.
Starting October 1st, we will start to randomly select tenants and disable basic authentication access for protocols in scope.
Protocols that are in scope for disablement:
- MAPI
- RPC
- Offline Address Book (OAB)
- Exchange Web Services (EWS)
- POP
- IMAP
- Exchange ActiveSync (EAS)
- Remote PowerShell
Not in scope for this disablement (we are not making changes to):
- SMTP AUTH
We will post a message to the Message Center 7 days prior, and we will post Service Health Dashboard notifications to each tenant on the day of the change.
If you have removed your dependency on basic auth, this will not affect your tenant or users. If you have not (or are not sure), check the Message Center for the latest data contained in the monthly usage reports we have been sending monthly since October 2021. The data for August 2022 will be sent within the first few days of September.
What If You Are Not Ready for This Change?
We recognize that unfortunately there are still many tenants unprepared for this change. Despite multiple blog posts, Message Center posts, interruptions of service, and coverage via tweets, videos, conference presentations and more, some customers are still unaware this change is coming. There are also many customers aware of the deadline who simply haven’t done the necessary work to avoid an outage.
Our goal with this effort has only ever been to protect your data and accounts from the increasing number of attacks we see that are leveraging basic auth.
However, we understand that email is a mission-critical service for many of our customers and turning off basic auth for many of them could potentially be very impactful.
One-Time Re-Enablement
Today we are announcing an update to our plan to offer customers who are unaware or are not ready for this change.
When we turn off basic auth after October 1st, all customers will be able to use the self-service diagnostic to re-enable basic auth for any protocols they need, once per protocol. Details on this process are below.
Once this diagnostic is run, basic auth will be re-enabled for those protocol(s). Selected protocol(s) will stay enabled for basic auth use until end of December 2022. During the first week of calendar year 2023, those protocols will be disabled for basic auth use permanently, and there will be no possibility of using basic auth after that.
Avoiding Disruption
If you already know you need more time and wish to avoid the disruption of having basic auth disabled you can run the diagnostics during the month of September, and when October comes, we will not disable basic for protocol(s) you specify. We will disable basic for any non-opted-out protocols, but you will be able to re-enable them (until the end of the year) by following the steps below if you later decide you need those too.
In other words – if you do not want basic for a specific protocol or protocols disabled in October, you can use the same self-service diagnostic in the month of September. Details on this process below.
Diagnostic Options
Update 1/1/2023: we are in the final stages of basic authentication deprecation in Exchange Online. Re-enablement of basic authentication or opting out of disablement by invoking the Microsoft 365 admin center Diag: Enable Basic Auth in EXO diagnostic is not possible anymore. Please update your clients to use modern authentication.
Starting January 1, 2023, the self-serve diagnostic will no longer be available, and basic auth will soon thereafter be disabled for all protocols.
Summary of timelines and actions
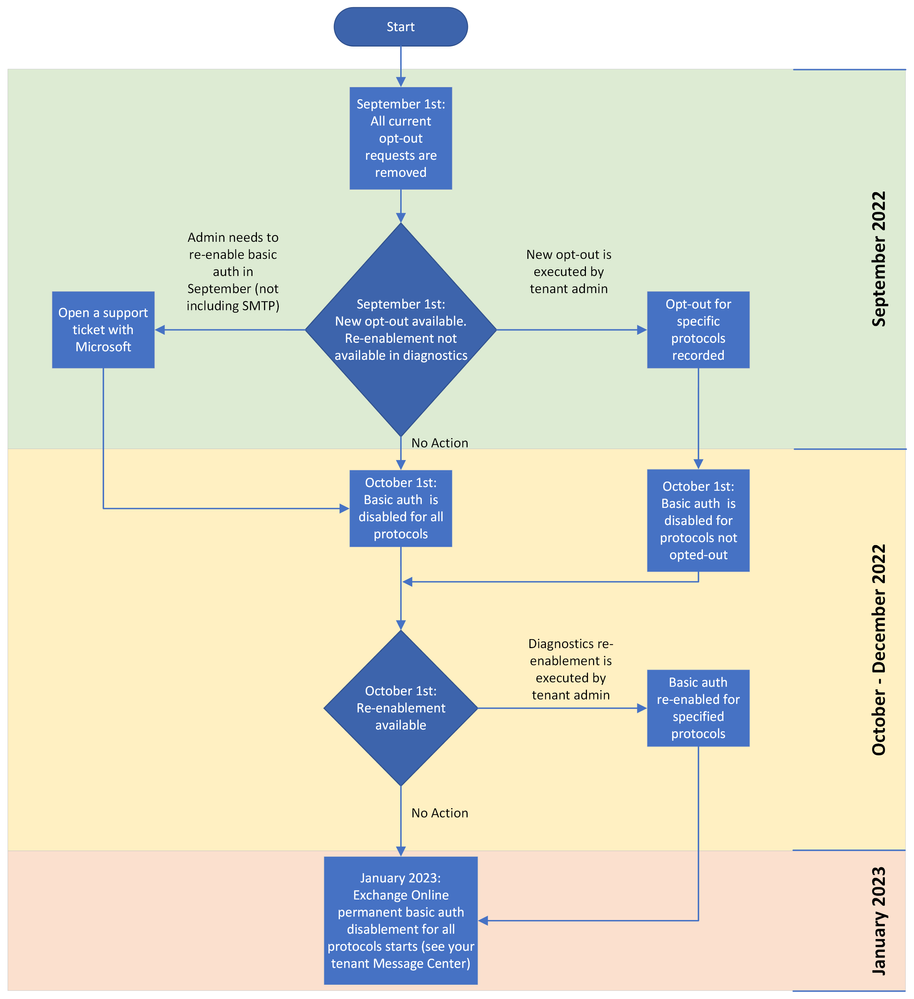
Please see the following flow chart to help illustrate the changes and actions that you might need to take:
Blocking Basic Authentication Yourself
If you re-enable basic for a protocol because you need some extra time and then afterward no longer need basic auth you can block it yourself instead of waiting for us to do it in January 2023. The quickest and most effective way to do this is to use Authentication Policies which block basic auth connections at the first point of contact to Exchange Online.
Just go into the Microsoft 365 admin center, navigate to Settings, Org Settings, Modern Authentication and uncheck the boxes to block basic for all protocols you no longer need (these checkboxes will do nothing once we block basic for a protocol permanently, and we’ll remove them some time after January 2023).
Reporting Web Service Endpoint
For those of you using the Reporting Web Service REST endpoint to get access to Message Tracking Logs and more, we’re also announcing today that this service will continue to have basic auth enabled until Dec 31st for all customers, no opt-out or re-enablement is required. And, we're pleased to be able to provide the long-awaited guidance for this too right here.
EOP/SCC PowerShell
Basic authentication will remain enabled until Dec 31st, 2022. Customers using scripts and automated tasks should migrate to certificate based authentication. Follow the Instructions here: App-only authentication.
Exchange Online PowerShell
Basic authentication for Exchange Online PowerShell will follow the opt-out and re-enablement guidance and timelines mentioned above. Note that after January 2023, Exchange v1 module without MFA will stop working permanently as it does not support modern auth. Please see Understanding the Different Versions of Exchange Online PowerShell Modules and Basic Auth for more information.
One Other Basic Authentication Related Update
We’re adding a new capability to Microsoft 365 to help our customers avoid the risks posed by basic authentication. This new feature changes the default behavior of Office applications to block sign-in prompts using basic authentication. With this change, if users try to open Office files on servers that only use basic authentication, they won't see any basic authentication sign-in prompts. Instead, they'll see a message that the file has been blocked because it uses a sign-in method that may be insecure.
You can read more about this great new feature here: Basic authentication sign-in prompts are blocked by default in Microsoft 365 Apps.
Office Team is looking for customers to opt-in to their Private Preview Program for this feature. Please send them an email if you are interested in signing up: basicauthdeprmailer@microsoft.com.
Summary
This effort has taken three years from initial communication until now, and even that has not been enough time to ensure that all customers know about this change and take all necessary steps. IT and change can be hard, and the pandemic changed priorities for many of us, but everyone wants the same thing: better security for their users and data.
Our customers are important to us, and we do not want to see them breached, or disrupted. It’s a fine balance but we hope this final option will allow the remaining customers using Basic auth to finally get rid of it.
The end of 2022 will see us collectively reach that goal, to Improve Security – Together.
The Exchange Team
- « Previous
-
- 1
- 2
- 3
- 4
- 5
- Next »
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.