- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- Vista Remote Desktop Connection Authentication FAQ
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Update: Some additional improvements are coming in this area. Please see this article .
There has been a lot of feedback about the new authentication features introduced in the latest version of the Remote Desktop Connection client. These features are part of our efforts to improve security for Terminal Services (TS) in Windows Vista and Windows Server code name “Longhorn” , however some users have run into a variety of problems that have caused frustration. In order to alleviate some of the frustrations, below is an FAQ on various symptoms users have run into, along with solutions and workarounds.
- Prompted for Authentication Twice when connecting to TS in Windows Server 2003
- Prompted for Authentication Twice when connecting to TS in Windows 2000 Server
- Credentials Entered in TS client rejected when connecting to Windows Server 2003
- Saved credentials do not work
- Cannot use smart card credentials to logon when running Remote Desktop on XP or Windows Server...
- How to remove invalid pre-populated domain names
- The pre-populated username in the credentials dialog does not match the username that is in th...
- Can’t change domain name when running Vista Remote Desktop Connection client.
- How to eliminate the ‘Remote Desktop Cannot verify the identity of the computer you want to c...
- When to use the “enablecredsspsupport:i:0” RDP file option.
Prompted for Authentication Twice when connecting to TS in Windows Server 2003
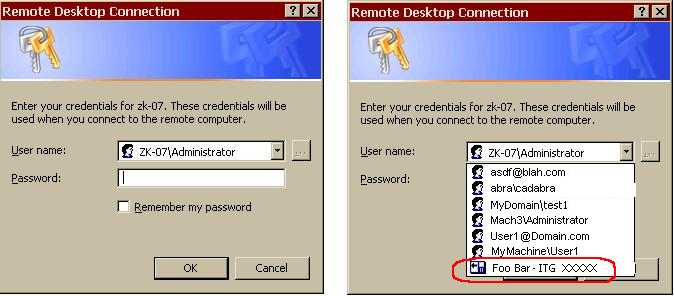
When using Remote Desktop Client 6.0 to connect to a Windows 2003 machine, some users have to enter credentials twice. Once before connection they will see Picture 1 below if they have Windows XP or Windows Server 2003 as the client or Picture 2 if they are using Windows Vista as the client.
Picture 1 - Windows XP - Windows Server 2003

Picture 2 - Windows Vista

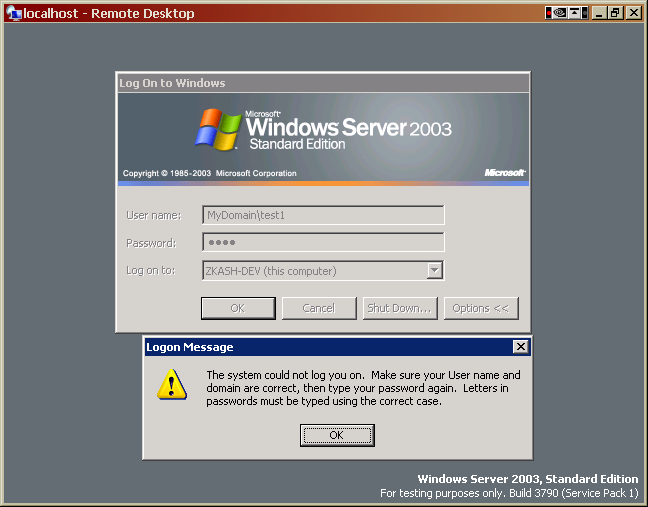
The second time they will be prompted as the remote servers logon screen (picture 3)
No error messages will be shown.

Picture 3
Answer : This is most likely the result of the way the remote server is configured. There are two possible settings that may be causing this:
-
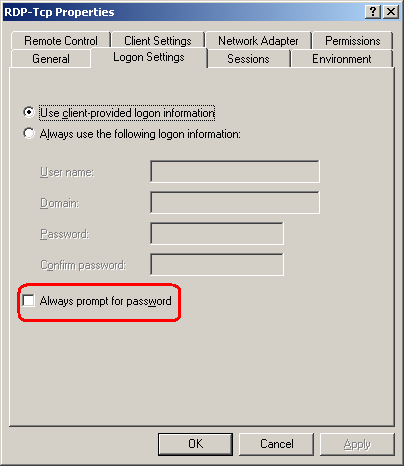
The most likely is the “Always prompt for password” setting is enabled on the server. In order to disable the setting, the administrator of the server you are connecting to must run Terminal Server Configuration administrative tool (tscc.msc) and double click on RDP-Tcp. In the “Logon Settings” tab, there is an option labeled “Always prompt for password” (see the option circled in red below).
- Alternatively: For Windows Server 2003, an administrator may have set the group policy located at: “Administrative TemplatesWindows ComponentsTerminal ServicesEncryption and SecurityAlways prompt client for password upon connection”. For Vista, this same policy is located “Administrative TemplatesWindows ComponentsTerminal ServicesTerminal ServerSecurityAlways prompt client for password upon connection.” Note: This policy is set as not configured by default; if this has been set remember it could have been configured either on the local group policy or a domain based group policy.
When either the option in Terminal Server Configuration administrative tool (tscc.msc) is selected or the group policy is enabled, the TS server will always show a winlogon prompt, regardless of what version of the Remote Desktop Client the user is running.
Prompted for Authentication Twice when connecting to Terminal Services in Windows 2000 Server
Why do users always have to enter credentials twice on Windows 2000 Server?
Answer : The setting in tscc.msc mentioned in the first question is enabled by default on Windows 2000. The administrator should disable this setting to fix the undesired behavior. Afterwards, the user can expect to not run into the winlogon screen or duplicate prompts.
Credentials Entered in TS client rejected when connecting to Windows Server 2003
Why is it that when connecting to Windows Server 2003, the credentials entered in the credentials dialog are rejected as follows:
Answer : The above behavior is caused when winlogon on the TS server cannot validate your credentials. This may be from a number of reasons: For example, the password or username may be incorrect. Other times, (and this may be the most frustrating to users), the domain may be in a format that is not recognized by the TS server. The best thing to do, when entering credentials into the credentials dialog, is to make sure that the domain, username, and password are all in a format that the server will accept. For example, let’s say one tries to connect to MyServer and you intend to log in with the MyUserName account from the MyDomain domain. If the user will just type in “MyUserName” in the User Name field in Credentials Dialog, the Windows 2003 Server will automatically pick “MyServer” as the domain value for login and the login will fail. But if the user provides “MyDomainMyUserName” as input for the User Name, logon will complete successfully.
Saved credentials do not work
Despite having saved credentials, users are still prompted to enter credentials on the remote server’s winlogon screen.
Answer : This can be due to one of two reasons. Either one of the policies mentioned in the answer to the first question are enabled, or the credentials that have been saved are not valid.
In instances where the saved credentials are not valid, there is one possible scenario that may lead to this behavior and cause user confusion. Consider the following:
- User tries to connect to server. His username is “MyDomaintest1” and his password is “LogMeOn”
- In the credentials dialog, user mistypes his credentials. For his password, instead of typing “LogMeOn”, he types “LogMeO”.
- User hits connect, and hits the winlogon screen. There is an error on the server stating “The system could not log you on. Make sure your User name and domain…”, just as in the example above
- User properly types his credentials into winlogon, and gets his session.
- The next time he goes to connect to the server, the saved credentials will not work.
This is because the credentials that have been saved on the client side are:
Username: MyDomaintest1
Password: LogMeO
Note that the password saved is not correct. This happens because whenever the user selects “Remember my credentials” in the credentials dialog, the credentials that are saved are whatever was typed in the credentials dialog. If the credentials are updated after connecting to the server, the correct credentials are not propagated back to the TS client and updated.
If the saved credentials are not correct, you may edit or delete them in Remote Desktop by clicking on the “Options” button. The dialog below should appear. Clicking “delete” will delete the saved credentials, and clicking “edit” will allow you to modify them.

Note that if the text “The saved credentials for this…” do not appear, then credentials are not saved.
Cannot use smart card credentials to logon when running Remote Desktop on Windows XP or Windows Server 2003?
Some users are having trouble using smart card credentials to logon.
Answer : To ensure that you can connect to Windows XP or Windows Server 2003 with smartcards, make sure that smartcards redirection is enabled.
-
Smart cards must be redirected. To redirect smart cards, click “Options” and select the “Local Resources” tab. In the tab, click on the button labeled “More”. In the dialog that pops up, make sure “Smart Cards” is clicked, as shown below:
-
Use the drop down box in the credentials dialog to select your smart card credentials. In the example below, the user has the credentials “ZK-07Administrator” selected. Instead, he needs to select the smart card credentials “Foo-Bar - ITG XXXXX” that is circled in red below.
How to remove invalid pre-populated domain names
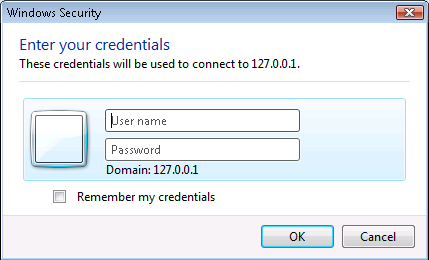
Some users have noticed that an invalid pre-populated domain name is placed in front of the user name in the credential dialog. Users are frustrated at having to delete this bad domain on every connection. The sequence of steps causing this behavior is as follows:
- User wants to connect to a machine via IP address, say 127.0.0.1.
- He enters the correct password and username “Administrator”. He successfully logs on.
- The next time he attempts to connect to 127.0.0.1, he sees in the “User name” field of the credentials dialog “127.0.0.1Administrator”. The user deletes the text “127.0.0.1” from the user name field and logs on. On successive connections, he is forced to keep deleting this extraneous text.
Answer : When a domain is not presented for the username, Remote Desktop assumes by default that a local server account will be used and the domain name is pre-filled accordingly. In this case, the server name entered was “127.0.0.1”, and as a result, the domain entered was the same. This was done for various reasons in Vista that are too complicated (and irrelevant) to go into detail here.
The best workaround for this behavior is to always enter a proper domain into the credentials dialog. If you are connecting to machine “MyMachine” using the “Administrator” account, do not just enter “Administrator” as the username, enter “MyMachineAdministrator”. From there on out, the proper domain and username will be prepopulated in the credentials dialog. Alternatively, if the user account is an account named “DomainUser” in the domain “MyDomain”, use “MyDomainDomainUser” instead of just “DomainUser”.
The pre-populated username in the credentials dialog does not match the username that is in the RDP file?
Despite having a string in the RDP file “username:s:MachineAdministrator”, the pre-populated username in the credentials dialog is something different (or maybe even blank).
Answer : This is a result of a design change. Instead of populating the credentials dialog with the last username used to connect to any server, we felt (and received positive feedback) that we should populate the credentials dialog with the last username used to connect to the specific server the user is connecting to . We felt this would provide a better experience. The downside is that users connecting to various machines with the same username would now have to reenter the username once upon their first connection to a machine. From then on, the username will be pre-populated on subsequent connections.
Can’t change domain name when running Windows Vista Remote Desktop Connection client:
In the dialog below, some users don’t see how to change the domain from “127.0.0.1” to “MyDomain”
Answer : To change the domain used in the credential dialog box show above you simply put a fully qualified domain username or UPN. For example if the domain is called “MyDomain”. Simply enter “MyDomain<username>” or username@domain.<fqdn> into the username field and the domain will automatically be updated, as shown in the two examples below.


How to eliminate the ‘Remote Desktop cannot verify the identity of the computer you want to connect to…” messages
When you connect to server with the ‘always connect, even if authentication fails’ setting set you will see the following notification dialog:

Answer : Before connecting, in Remote Desktop, do the following:
- Click on “Options”
- Click on the “Advanced Tab”
-
In “Authentication Options”, select “Always connect, even if authentication fails, as seen below:
This will disable the warning prompt. Please be aware that selecting this option makes it possible for attackers to intercept and modify the data exchanged between client and server.
When to use the “enablecredsspsupport:i:0” RDP file option.
Several other forums on the internet have suggested placing “enablecredsspsupport:i:0” in the RDP file used by the Remote Desktop client.
Answer : This option does disable the new credential prompting behavior, but it also disables support for Network Level Authentication for Vista (and Longhorn Server) RDP connections; Network Level Authentication requires credentials to be provided by the client before a session is created on the server side.
This option is meant for dealing with unexpected failures on connections using Network Level Authentication.
We strongly recommend users avoid using this flag unless none of other fixes described in this post work and no other alternative is available. If this setting is used try to limit its scope as much as possible by using it only those RDP files meant for connections to specific servers (i.e. avoid setting it in your Default.rdp file).
Deploying this configuration option widely will cause hard to diagnose issues when connecting to Vista and Longhorn Server computers that require Network Level Authentication.
Update: Some additional improvements are coming in this area. Please see this article .
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.