- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 18 2020 12:15 PM
I had a look at the community pages, but can't find a section specific to Lighthouse, so pardon me for posting here. If there is a dedicated space, I would appreciate a link.
I have an issue pulling customer log information from Log Analytics into our Lighthouse tenant.
I have a group that gets assigned Contributor rights to the customer environment at subscription level. I am able to browse all resources, and I have verified that I can create resources. However, when I access the Log Analytics workspace(s), I am unable to run any queries (or query any VM performance data through Azure Monitor), and it's as if it just hangs there trying to retrieve the log data. Attached is a snip of what I see.
Logging in to the customer tenant directly with Owner permissions I am able to successfully query the logs and view VM performance data.
Please advise if there are any specific considerations in terms of permissions. I assumed Contributor role at subscription level would have sufficed.
Thanks
Sebastiaan
- Labels:
-
monitoring
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 06 2020 02:06 PM
Apply "Log Analytics Reader" role. "Contributor" rights will not give access to read/query logs.
Hope this helps!
-Azeem
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 23 2020 08:10 AM
Thanks for the guidance.
I've changed this, and I now get the LA Reader role assigned (at subscription level). Whenever I run any query, I still get the following error:
{"statusCode":"Unauthorized","serviceRequestId":null,"statusMessage":"{\"error\":{\"code\":\"AuthorizationRequiredError\",\"message\":\"Valid authentication was not provided\"}}","eventCategory":"Administrative"}
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 30 2020 06:06 PM
@SebastiaanR Did you get a resolution for this?
I've mirrored your scenario by setting up my provider with ONLY log analytics reader access to a test customer subscription, and I can successfully query log analytics (via Lighthouse delegation) with no errors. This suggests it's something specific to your provider tenant, which would require a support ticket for Microsoft to investigate.
-Sonia
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 30 2020 06:15 PM
Also note the doc on managing access to Log Analytics workspaces states at the bottom that if a user is granted the global Reader or Contributor roles, they will be granted access to all log data:
https://docs.microsoft.com/en-us/azure/azure-monitor/platform/manage-access?WT.mc_id=modinfra-5682-s...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 11 2020 01:28 AM
Hi @Sonia Cuff
Same error in my case. I gave Sentinel Contributor and Logs Analytics Reader (also tried w/ Contributor) access to the same PrincipalId through Lighthouse. I can see alerts/incidents but not perform queries or see tables from the managing tenant.
Managed tenant did enable Microsoft.Insights. Any idea on how to debug this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 11 2020 05:18 AM - edited Sep 11 2020 05:19 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 15 2020 06:38 PM
Great detective work @milkmix_
I've reached out internally to see if we can get the Doc updated to mention this pre-req.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 27 2020 01:25 AM
@milkmix_ Thanks for this feedback. This, however, did not resolve my problem.
The tenant I am accessing the customer subscriptions from does not have its own subscription associated, and the registered providers are added at subscription level, so not entirely sure how to then go about that.
Is this perhaps something I am doing wrong? Do I need to have a subscription (albeit even an unused one) in the managing tenant for this to work?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 27 2020 04:23 PM
Solution@SebastiaanR I never even thought of a scenario where the managing tenant wouldn't have a subscription! Add even an Azure Free Account sub to it and see if that works.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 27 2020 11:30 PM
@Sonia Cuff Bingo! This sorted it right out! It is a little vague, although I suppose I could have mentioned this configuration from the get go.
Thanks again @milkmix_ for nudging the thought process in this direction. Much appreciated!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 08 2022 01:48 AM
Hi @Sonia Cuff,
maybe you can help me out with some similar situation.
We have a managing tenant without subscription.
I saw the updated docs Monitor delegated resources at scale - Azure Lighthouse | Microsoft Docs with the section to add New-AzADServicePrincipal for the managing tenant without subscription.
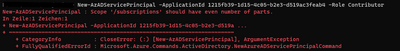
But we cannot get it to work. We always get the following:
We were then able to set it like this:
After that we onboarded a customer. But when we try to access some logs we still get the error:
So it seems that we will forcely need a subscription within the managing tenant?
Any hints?
Thanks for your help
Regards,
Ben
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 03 2023 01:26 PM
From your managing tenant context, try to register all the 1st party service principals that the Microsoft.Insights resource provider registers.
Example:
Connect-AzAccount -Tenant managingtenant.onmicrosoft.com
New-AzADServicePrincipal -ApplicationId 6bccf540-eb86-4037-af03-7fa058c2db75
New-AzADServicePrincipal -ApplicationId 11c174dc-1945-4a9a-a36b-c79a0f246b9b
New-AzADServicePrincipal -ApplicationId 035f9e1d-4f00-4419-bf50-bf2d87eb4878
New-AzADServicePrincipal -ApplicationId f5c26e74-f226-4ae8-85f0-b4af0080ac9e
New-AzADServicePrincipal -ApplicationId b503eb83-1222-4dcc-b116-b98ed5216e05
New-AzADServicePrincipal -ApplicationId ca7f3f0b-7d91-482c-8e09-c5d840d0eac5
New-AzADServicePrincipal -ApplicationId 3af5a1e8-2459-45cb-8683-bcd6cccbcc13
New-AzADServicePrincipal -ApplicationId 6a0a243c-0886-468a-a4c2-eff52c7445da
New-AzADServicePrincipal -ApplicationId 707be275-6b9d-4ee7-88f9-c0c2bd646e0f
New-AzADServicePrincipal -ApplicationId 461e8683-5575-4561-ac7f-899cc907d62a
New-AzADServicePrincipal -ApplicationId 562db366-1b96-45d2-aa4a-f2148cef2240
New-AzADServicePrincipal -ApplicationId e933bd07-d2ee-4f1d-933c-3752b819567b
New-AzADServicePrincipal -ApplicationId f6b60513-f290-450e-a2f3-9930de61c5e7
New-AzADServicePrincipal -ApplicationId 12743ff8-d3de-49d0-a4ce-6c91a4245ea0
New-AzADServicePrincipal -ApplicationId 58ef1dbd-684c-47d6-8ffc-61ea7a197b95- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 04 2023 01:47 AM
I've recheck again on our managing tenant and it seems to work now.
Even without your additional ServicePrincipals.
Thanks again
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 27 2020 04:23 PM
Solution@SebastiaanR I never even thought of a scenario where the managing tenant wouldn't have a subscription! Add even an Azure Free Account sub to it and see if that works.