- Home
- Azure
- Azure Virtual Desktop
- Insider Preview: Single sign-on and passwordless authentication for Azure Virtual Desktop
Insider Preview: Single sign-on and passwordless authentication for Azure Virtual Desktop
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 24 2022 03:41 PM - last edited on Sep 29 2022 02:28 PM by Eva Seydl
Today we’re announcing the Insider preview for enabling an Azure AD-based single sign-on experience and support for passwordless authentication, using Windows Hello and security devices (like FIDO2 keys). With this preview, you can now:
- Enable a single sign-on experience to Azure AD-joined and Hybrid Azure AD-joined session hosts
- Use passwordless authentication to sign in to the host using Azure AD
- Use passwordless authentication inside the session
- Use third-party Identity Providers (IdP) that integrate with Azure AD to sign in to the host
Getting started
This new functionality is currently available in Insider builds of Windows 11 22H2, available in the Azure Gallery when deploying new session hosts in a host pool.
- Want a quick overview of the new functionality? Watch this intro video on Azure Academy!
- To get started with single sign-on, follow the instructions to Configure single sign-on which will guide you in enabling the new authentication protocol.
- To start using Windows Hello and FIDO2 keys inside the session, follow the instructions for In-session passwordless authentication to use the new WebAuthn redirection functionality.
- Learn more about the supported authentication methods supported by Azure Virtual Desktop, including single sign-on on our Identities and authentication page.
Stay tuned for news about the upcoming public preview which will add support for Windows 10 and current Windows 11 hosts.
- Labels:
-
AVDUpdate
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 26 2022 06:22 AM
@David Belanger
First of all, This is great. We were awaiting this feature for some time now.
Great to see it coming to light. We of course went right ahead and deployed it to our test pool.
- VM Login AAD only
- Azure Files AAD only
- Intune enabled
- now running 22h2 :)
We had a small issue though, we are allowing the Azure Virtual Desktop application outside of the compliant device policies. However it seems like the exemption we made for the Enterprise application "Azure Virtual Desktop" doesn't include this, the application is called.
- Microsoft Remote Desktop (app ID a4a365df-50f1-4397-bc59-1a1564b8bb9c), which applies when the user authenticates to the session host when single sign-on is enabled.
Please add this to the FAQ :)
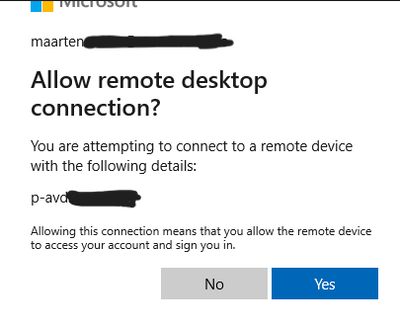
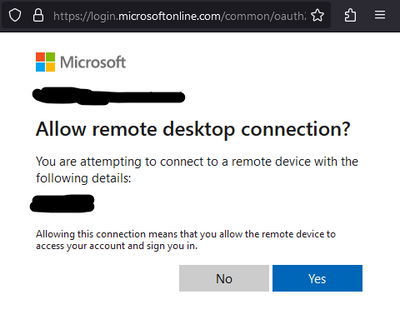
Also I seem to need to give consent my login on the VM.
I cannot find the admin consent button for the Enterprise application.
please provide instructions on this :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 16 2022 03:55 AM
How about MAC?
Apps : a4a365df-50f1-4397-bc59-1a1564b8bb9c
The above apps is not working for MAC and web
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 16 2022 06:02 AM
@Andrew_Woo I think this SSO feature is only working for Windows atm yeah
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 16 2022 09:48 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 21 2022 03:27 PM
In the Azure AD sign-in logs we see a sign-in failure saying "The user or administrator has not consented connecting to the target-device: '{identifier}'. Send an interactive authorization request for this user and target-machine." and the user is prompted with a message saying "Because you're accessing sensitive info, you need to verify your password." I have not found any way of getting Seamless SSO to work with this and I am wondering if others are seeing the same issue or there is something I am missing.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 21 2022 03:32 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 22 2022 07:57 AM
Does this support AADDS joined AVD ? Specifically where users sign in with "email address removed for privacy reasons" and the AVD are joined to AADDS "domain.onmicrosoft.com"?
The key here being joined to AzaureAD Directory Services, with users coming in from AzureAD, no Hybrid, no syncing on on-prem users.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 22 2022 07:58 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 22 2022 03:55 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 22 2022 03:58 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 23 2022 12:59 AM
@David Belanger Hi, I got some feedback on the feature regarding the SSO feature for Azure AD joined devices.
How SSO to on-premises resources works on Azure AD joined devices - Microsoft Entra | Microsoft Lear...
Since the authentication protocol has changed. We do not receive a Kerberos ticket from the onPrem DCs anymore. breaking some fileservers and other resources that are needed for the end users.
Are you guys aware of this change? and is it going to be a supported scenario when this will go into GA?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 23 2022 04:16 PM
@dikkekip20 Was the Kerberos Server Object created to provide access to on-prem resources?
Configure single sign-on for Azure Virtual Desktop - Azure | Microsoft Learn
David
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 24 2022 05:21 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 13 2022 10:40 AM
I am wondering if this is because we have allowed the RDP access in the main region and in the new it is trying to ask for it again. Do you have any thoughts? When I look at the log for the attempt I see the below text under the authintication details, but can find no documentation on what a "Results Detail" of other is
Date Authentication method Authentication method detail Succeeded Result detail Requirement
12/9/2022 Password Password in the cloud false Other
12/9/2022 Mobile app notification true MFA completed in Azure AD
So again any thoughts?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 15 2022 09:08 AM
@Roger1175 I am seeing your issue but only on VM's that we have failed over as part of D/R testing.
I put a comment in as well to David B asking if there is a missing config to address the D/R AVD once a failover has been triggered for AVD have not see a response yet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 27 2023 08:32 AM - edited Jan 30 2023 02:46 AM
Regarding reply from: @dikkekip20 Any updates regarding consent login on the VM? We are getting the same prompt which is new.
Can we give admin consent to this client_id=a85cf173-4192-42f8-81fa-777a763e6e2c so that users won't be bothered with this?
We already consented server & client app with Welcome Admin - RDWeb (microsoft.com)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 12 2023 11:57 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 23 2023 07:22 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 23 2023 11:44 PM