- Home
- Azure
- Azure Virtual Desktop
- Re: FSLogix profile container using Azure Files and domain controller step by step
FSLogix profile container using Azure Files and domain controller step by step
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 15 2020 04:32 PM - edited Apr 15 2020 10:56 PM
This guide walks an IT administrator through the steps needed to configure an existing Windows Virtual Desktop (WVD) hostpool with profiles stored on an Azure Files storage account. Authentication will be via a domain controller (aka native AD).
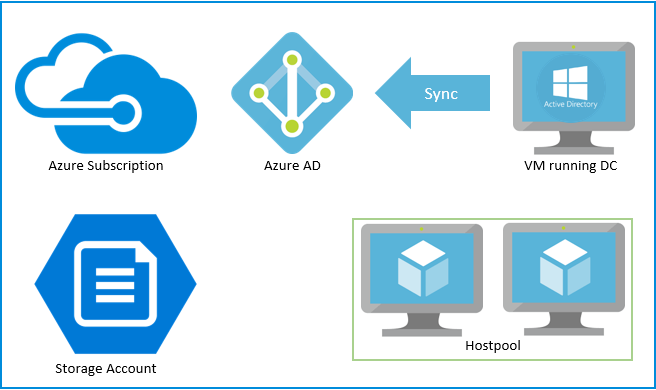
The diagram below represents the environment we are starting with:
- Azure subscription tied to Azure AD
- Virtual machine acting as active directory with Azure AD connector synching to Azure AD
- WVD hostpool
- Storage Account (this guide starts with setting up this storage account (SA))
The full guide for setting up Active Directory (AD) authentication over SMB for Azure file shares (AFS) is available here.
Prerequisites
Global administrator on Azure AD is required to be able to assign RBAC permission. Contributors cannot assign permission to other users, as outline here.
Account with Owner permissions on the Azure subscription.
Account that is part of Active Directory (AD). This account needs to be able to sing into VM that is joined to the domain and have permission to create new accounts.
Note: Please note all prerequisites must be met.
There are certain policies that may block creating and using the account that represents the storage account (for example, if maximum password length is set to less than 80 characters the AD will not accept the new account). Such policies need to be disabled for the OU where the AD account representing the storage account is to be created.
Selecting Azure Files tier
Prior to creating a storage account Azure Files tier must be selected. Azure Files offers two different tiers of storage, premium and standard, to allow you to tailor your shares to the performance and price requirements of your scenario:
- Premium file shares: Premium file shares are backed by solid-state drives (SSDs) and are deployed in the FileStorage storage account type. Premium file shares provide consistent high performance and low latency, within single-digit milliseconds for most IO operations, for IO-intensive workloads.
- Standard file shares: Standard file shares are backed by hard disk drives (HDDs) and are deployed in the general-purpose version 2 (GPv2) storage account type. Standard file shares provide reliable performance for IO workloads that are less sensitive to performance variability such as general-purpose file shares and dev/test environments. Standard file shares are only available in a pay-as-you-go billing model.
Depends on the target performance, cost, and regional considerations, you can select the most appropriate performance tier for storing the user profile data. We have included our recommendation based on the performance of the typical remote desktop workloads types.
|
File Tiers |
|
|
Light |
Less than 200 concurrent active users: Standard file shares |
|
More than 200 concurrent active users: Premium file shares. You may also consider using Standard file shares with multiple shares if you are scaling up from existing Standard file shares or plan to manage scale out for cost efficiency. |
|
|
Medium |
Premium file shares |
|
Heavy |
Premium file shares |
|
Power |
Premium file shares |
You can leverage the guidance above and further optimize for your WVD scenario. Detailed information of Azure Files on performance targets (Standard, Premium) and pricing is available to help you further fine tune the file share solution.
Setup storage account
- Sign into Azure portal
- In the search box enter Storage account
- Click +Add and in the Create storage account enter
- Create a new resource group
- Enter unique storage account name
- Location, must be the same location as the WVD Hostpool
- Performance standard (as this is a test deployment with less than 200 users)
- Account kind – StorageV2
- Replication – Read-access geo-redundant (RA-GRS)
- Click Review + create and the Create once validation has passed
Create an Azure file share
- Once the storage account is deployed, click Go to resource
- On the Overview screen click File shares
- Click +File shares and create a new named profile
- Enter Quota of 30 GB
- Click Create
Enable AD authentication for your SA
These steps need to be ran from a machine that is already domain joined. In our environment this will be done from the VM running the domain controller.
- RDP into the domain controller VM
- Download the AzFilesHybrid module from here
- Unzip to a local folder
- Open PowerShell and navigate to the folder from step #3
- (optional) Set execution policy to Unrestricted via
Set-ExecutionPolicy -ExecutionPolicy Unrestricted -Scope CurrentUser
- Install NuGet via
Install-PackageProvider -Name NuGet -MinimumVersion 2.8.5.201 -Force
- Import the downloaded PS module AzFilesHybrid
Import-Module -Name .\AzFilesHybrid.psd1
- Connect to our Azure via PowerShell
Connect-AzAccount
- Sign in when prompted
- (optional) If there are multiple Azure subscription select the correct one via
Select-AzSubscription -SubscriptionId <subscription name>
- Connect the SA with active directory via command below. Replace <rg-name> and <sa-name> with values from section Setup storage account.
Important: the below command supports capability for adding new account to an organization unit via the switches -OrganizationalUnitName and -OrganizationalUnitDistinguishedName. For more details, please visit.
Join-AzStorageAccountForAuth -ResourceGroupName "<rg-name>" `
-Name "<sa-name>" `
-DomainAccountType "ComputerAccount" `
-OrganizationalUnitDistinguishedName "<ou-distinguishedname-here>"
- Verify the setup is correct
# Grab the storage account info (creates an array)
# $storageaccount = Get-AzStorageAccount `
# -ResourceGroupName "<resource-group-name>" `
# -Name "<storage-account-name>"
$storageaccount = Get-AzStorageAccount -ResourceGroupName <RG> -Name <storageacct>
# Verify - List the directory service of the selected service account
$storageAccount.AzureFilesIdentityBasedAuth.DirectoryServiceOptions
# Verify - List the directory domain information if the storage account has enabled AD authentication for file shares
$storageAccount.AzureFilesIdentityBasedAuth.ActiveDirectoryProperties
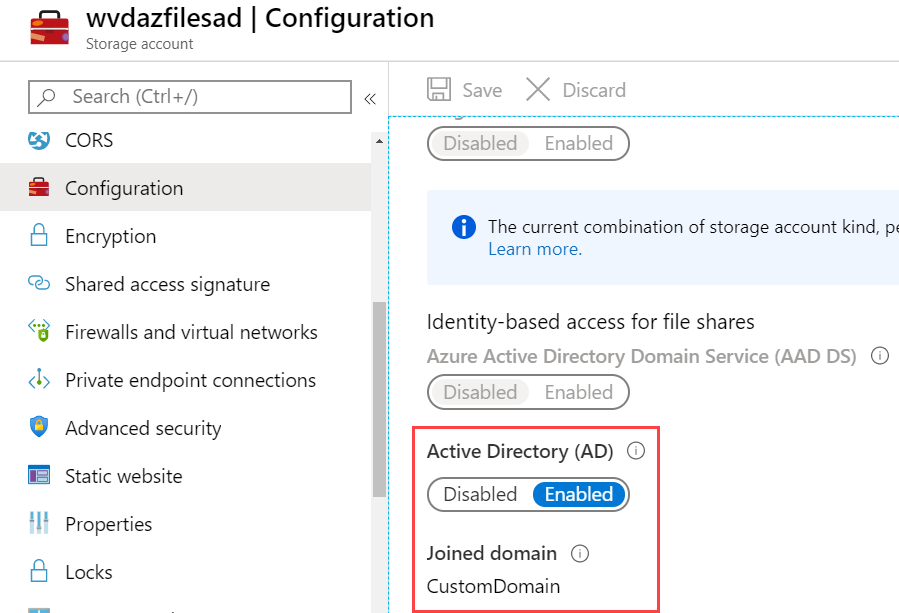
- Navigate to the Azure portal open the storage account that was created, click on Configuration and confirm Azure Directory (AD) is enabled
Assign Azure RBAC permission to storage account
At least one user, likely and administrator will need to be assigned Storage File Data SMB Elevated Contributor. The administrator will be used to assign NTFS permissions on the files share.
For all users that need to have FSLogix profiles stored on the SA assign Storage File Data SMB Share Contributor. It is a best practice to create an AD group for all users that need to have FSLogix profiles.
To assign RBAC permissions:
- Navigate to the Azure portal
- Open the storage account created in the Setup storage account section
- Click Access Control (IAM)
- Click Add a role assignment
- In the Add role assignment blade, select Storage File Data SMB Share Elevated Contributor for the administrator account.
- Click Save
Repeat the above steps for all users that need to have FSLogix profiles but change the role to Storage File Data SMB Share Contributor.
Note: the accounts being used here must be create in the domain controller and synched to Azure AD. Accounts sourced from Azure AD are not appropriate.
Configure NTFS permissions over SMB
Once RBAC permission have been assigned the next step is to configure the NTFS permission. There are two pieces of information we need from Azure portal to complete the NTFS permission:
- UNC path
- SA key
Obtaining the UNC path
- Navigate to the Azure portal
- Open the storage account created in the Setup storage account section
- From under Settings select Properties
- In the following screen locate the Primary File Service Endpoint and copy it to a text editor
- Modify the URI to become UNC by:
- Remove https://
- Replace forward slash / with a back slash \
- Append name of the file share created in the Create an Azure file share section
For example: \\customdomain.file.core.windows.net\<fileshare-name>
Obtaining SA key
- Navigate to the Azure portal
- Open the storage account created in the Setup storage account section
- From the storage account blade select Access keys
- Copy key1 or key2 to a local file
Configure NTFS permissions
From the VM running the domain controller open the command prompt.
Run command below to mount the Azure files share and assign it a drive letter
net use <desired-drive-letter>: <UNC-pat> <SA-key> /user:Azure\<SA-name>
Use Windows File Explorer to grant full permission to all directories and files under the file share, including the root directory.
- Open Windows File Explorer and right click on the file/directory and select Properties
- Click on the Security tab
- Click on Edit... button to change permissions
- You can change the permission of existing users, or click on Add... to grant permissions to new users
- In the prompt window for adding new users, enter the target user name you want to grant permission to in the Enter the object names to select box, and click on Check Names to find the full UPN name of the target user.
- Click on OK
- In the Security tab, select all permissions you want to grant to the newly add user. Details on what permissions are optimal for FSLogix is available here.
- Click on Apply
Configure FSLogix on session host VMs
In this section we cover the steps needed to configure a VM with FSLogix. These steps need to be completed on all VMs. There are multiple ways to deploy in bulk and configure FSLogix that do not require work on each individual VM. More information on those available
- RDP to the session host VM part of the WVD Hostpool
- Download FSLogix agent from
- Unzip and execute and run FSlogixAppsSetup.exe
- Agree with the conditions and click Install
- Configure profile container registry settings, more details here:
- Navigate to Computer\HKEY_LOCAL_MACHINE\SOFTWARE\FSLogix
- Create key Profiles
- Create Enabled, DWORD with value of 1
- Create VHDLocations, MULTI_SZ
- Set the value of VHDLocations to the UNC path generated in the section Obtaining the UNC path
- Restart the VM
Testing
Once the VM has been restarted sign in with a user that has permission on the session host and on the file share.
When the session has been established and start menu is visible:
- Navigate to the Azure portal
- Open the storage account created in the Setup storage account section
- Click on the share create in the Create an Azure file share
Note: For troubleshooting FSLogix please follow the guide here.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 20 2020 09:57 AM
@Christian_Pedersen Robocopy and latest AzCopy 10.4.0 can help migrate from standard to premium while preserving ACLs.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 20 2020 10:24 AM
@Nagorg-Terralogic We are close. Our current target for AD integration GA is June of this year. (Subject to change).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 20 2020 10:26 AM
@Gunjan Jain great news... Will keep my eye's open for this!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 20 2020 10:27 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 22 2020 01:56 AM
Has anybody benchmarked login performance with this setup? I'm currently seeing 25-45sec login times since enabling FSLogix (Premium SA with 1024gb quota).
The "Please wait for FSLogix" bit seems to take the lions share of that. Login times are <10sec with FSLogix disabled.
Is this normal?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 29 2020 01:04 AM
Is this happening on every log on? or just on profile creation
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 29 2020 01:13 AM
@Stefan Georgiev Every logon, I've got the times down to around 25sec now (15 of that is the loading FSLogix Profile bit) by ramping up the storage account to 1024GB (we only need 80gb, so seems a bit of a waste) so storage performance does seem to have an ever diminishing benefit.
Just trying to understand if this is normal/acceptable - if it is, the 'costs' are almost certainly worth the benefits of using FSLogix anyway.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 29 2020 03:22 PM - edited May 29 2020 03:24 PM
@townendk For small # of users and size, you probably be OK with the standard tier. Benefits for premium comes from a larger scale, when users can pool resources and get benefits of higher IOPS/throughput of a large premium share. Did you try with standard tier? Please make sure large file shares is enabled to get increased scale for the standard tier.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 31 2020 02:28 AM
@Gunjan Jain Yes We tried Standard initially and it was borderline unusable. Login times of 3-5minutes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 12 2020 01:04 AM - edited Jun 15 2020 03:37 AM
@Stefan Georgiev recently I've tried to set it up, with a tenant which uses a 3rd party tool to sync the on-premises accounts. (for evaluating better SSO options)
The fact that the users then are shown as "Azure Active Directory" seems to effectively prevent the access to the ad-integrated storage account.
This is more to inform others that it seems that you must use Azure AD-Sync.
See attached screenshot from Debug-AzStorageAccountAuth
Regards,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 12 2020 09:02 AM
@Benjamin Graus TY Benjamin, I am not surprise but it is excellent that you have validate
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 12 2020 11:25 AM
- « Previous
-
- 1
- 2
- Next »