- Home
- Azure
- Azure Virtual Desktop
- AVD sign-on issue Azure Hybrid joined devices
AVD sign-on issue Azure Hybrid joined devices
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 22 2022 12:58 AM
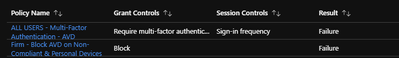
Hi, starting yesterday we have been having issues signing into AVD. We have a CA policy in place restricting only hybrid joined devices access, when accessing AVD we are presented with error "You cannot get there from here. This application contains sensitive information and can only be accessed from Company XXX. Company XXX domain joined devices. Access from personal devices is not allowed.
This only started yesterday evening.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 22 2022 01:03 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 24 2022 07:23 AM
Since Thursday night this has been failing and stating the user satisfied the requirement but doesn't have permission. When checking the device in Azure AD or Intune/Endpoint the device is showing compliant. We've not changed anything on our end so there's clearly something Microsoft has failed to acknowledge.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 24 2022 07:38 AM
@DBR14 I rang Microsoft this morning, after waiting 15 minutes for them to answer I gave up. It's now say with our CSP to try and work out what's happened. Nothing has changed our side either, for now though I've had to disable the Hybrid joined CA policy otherwise no one can login!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 24 2022 07:43 AM
@mdayton11 The workaround for us is when the user goes to sign in is to select "Use another Account" rather than the one cached and it works. But if you select the cached account, which is their work account it bombs on the CA Policy. I can't tell if this is the CA policy malfunctioning or if there's some health attestation issues. Everything looks peachy when I check the endpoint's status, fully compliant and marked Corporate so it should be a non-issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 24 2022 07:49 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 24 2022 07:52 AM