- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- Ignore alerts if Entities Match previous within the last 24 hours
Ignore alerts if Entities Match previous within the last 24 hours
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 15 2020 08:39 AM
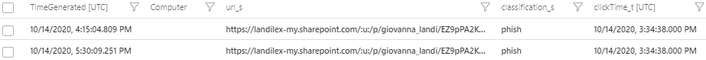
I have a Proofpoint TAP connected to Sentinel. When a User clicks on a Malicious link in an email, one of our remediation steps is to have the user change their password. I have encountered a situation whereby Proofpoint generated one alert, but Sentinel generated two of the same alerts, an hour apart and triggered a playbook twice, to reset a user's password on both occasions. As in the image
I am seeking to create a solution, where by if a new alert is generated and has the entities match a previously created alert within 24 hours, the 2nd would be ignored and would not trigger the playbook. If there is a dynamic way of preventing these duplication of alerts, that would be the preferred rout.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 15 2020 08:45 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 15 2020 10:02 AM
@LodewykV I have configured to group the alerts if the entities match. I have a question about that function though. So I have configured my query to run every 5 minutes. If I set to limit the group to alerts created within 1 hour and After the first alert is generated the first query run, will the subsequent alerts be added to the 1st, and won't they trigger an automated playbook? I get that the alerts generated within the hour will be grouped. My question however is how will that affect the automation? The first query runs and generates an alert which triggers a playbook. Query runs again after 45 minutes and generates another alert with same entities, will that trigger the playbook, or it will just be added to the first alert and not trigger the playbook?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 15 2020 11:54 AM
There is a new possibility in private preview, which will only trigger once per incident. This would be a solution for you, but it's not GA yet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 15 2020 12:01 PM
@Thijs Lecomte You might be referring to "When Azure Sentinel incident creation rule was triggered"?
Thank you for the response
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 15 2020 12:05 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 15 2020 12:30 PM
@Thijs LecomteThank you! But is there a way to stop alerts from generating for the same entities repeatedly, especially if the source is only generating one of such alerts?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 15 2020 12:35 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 15 2020 12:46 PM
@Thijs Lecomte Nice Lead.. Do you have an example you can show me please? This is what I have so far.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 17 2020 02:51 PM
2. create your main query and use "entities !in~ (the_list_you_created)".
If you have more than one entities, you can extend a new column and concatanate them into one field both for creating the list and using it in the main query.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 18 2020 11:21 AM
https://docs.microsoft.com/en-us/azure/data-explorer/kusto/query/joinoperator?pivots=azuredataexplor...
You should join on the 'HostCustomEntity, FileHashCustomEntity and SenderCustomEntity'