- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- Re: Detailed Email Alerts
Detailed Email Alerts
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 15 2020 01:16 PM
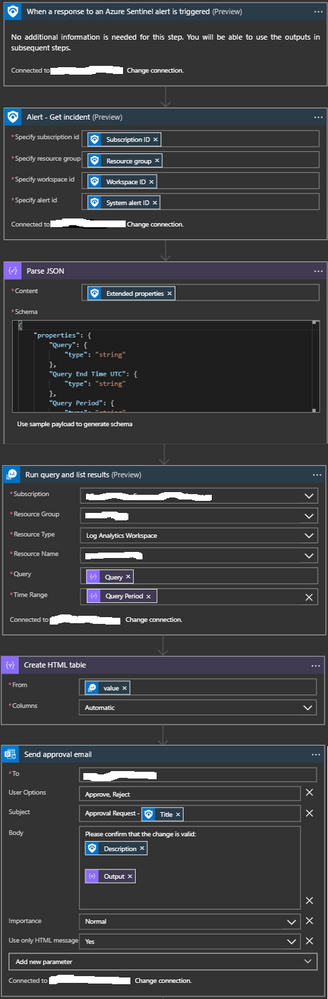
One area that I haven't seen covered is how to get more detail into email alerts that may be generated as the result of a playbook execution. You can get basic alert information but no information on the event data.
I configured this playbook which will run the query that is part of the analytic rule and send those in an email formatted as an HTML table.
This is the JSON schema:
{
"properties": {
"Query": {
"type": "string"
},
"Query End Time UTC": {
"type": "string"
},
"Query Period": {
"type": "string"
},
"Query Results Aggregation Kind": {
"type": "string"
},
"Query Start Time UTC": {
"type": "string"
},
"Search Query Results Overall Count": {
"type": "string"
},
"Total Account Entities": {
"type": "string"
},
"Total Host Entities": {
"type": "string"
},
"Total URL Entities": {
"type": "string"
},
"Trigger Operator": {
"type": "string"
},
"Trigger Threshold": {
"type": "string"
}
},
"type": "object"
}Hope this is helpful for some of you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 16 2020 09:45 PM
- https://azsec.azurewebsites.net/2020/01/19/notify-azure-sentinel-alert-to-your-email-automatically/
- https://azsec.azurewebsites.net/2020/01/19/parse-extendedproperty-in-azure-sentinel-alert-for-logic-...
These give you step-by-step guidance and sample HTML format.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 04 2020 04:35 AM
@mperrotta This was priceless. I am sure it will help many people who have been desperately searching for a breakthrough..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 01 2021 10:52 PM
Thanks @mperrotta
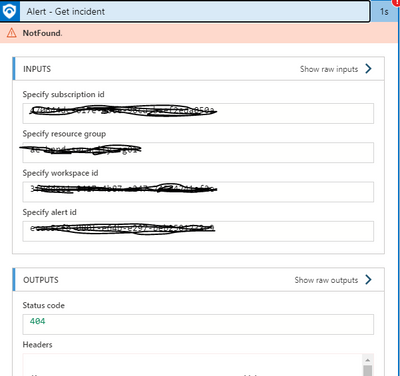
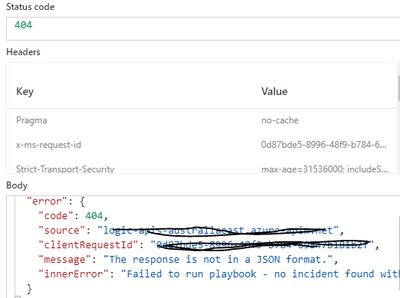
Its works intermittently for me . I keep getting an error. Fails on "Alert - Get Incident" step.Any ideas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 06 2021 01:05 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 06 2021 03:21 PM
@GraceAA A couple of things
1) Put in a time delay for 5-10 seconds between the trigger and when you load the incident. There is sometimes brief delay creating the incident.
2) Rewrite the playbook to use to the Incident trigger that gets used with the new Azure Sentinel Automation features. All the alert and incident information will still be available (although there may be some name changes)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content