- Home
- Security, Compliance, and Identity
- Microsoft Defender for Cloud Blog
- Microsoft Defender for Cloud Monitoring Agent Deployment Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Introduction
Microsoft Defender for Cloud is segmented as a Cloud Security Posture Management (CSPM) and Cloud Workload protection Platform product (CWPP). CWPPs is defined by workload-centric security protection solutions, which are typically agent-based. To be able to protect IaaS VM's, on-premises servers and other clouds server’s Defender for Cloud uses agent-based monitoring.
In this blogpost, we want to help you understand the options available to protect your resources and the advantages and disadvantages.
Types of Agents & Methods to Deploy
There are two types of agents:
- Direct Agent (MMA Setup file)
- Log Analytics Agent extension
Direct agent:
The direct agent is a standalone installation. This installation is an MSI\EXE file hence, organizations can leverage a deployment tool such as System Center Configuration Manager or other scripted way to deploy it.
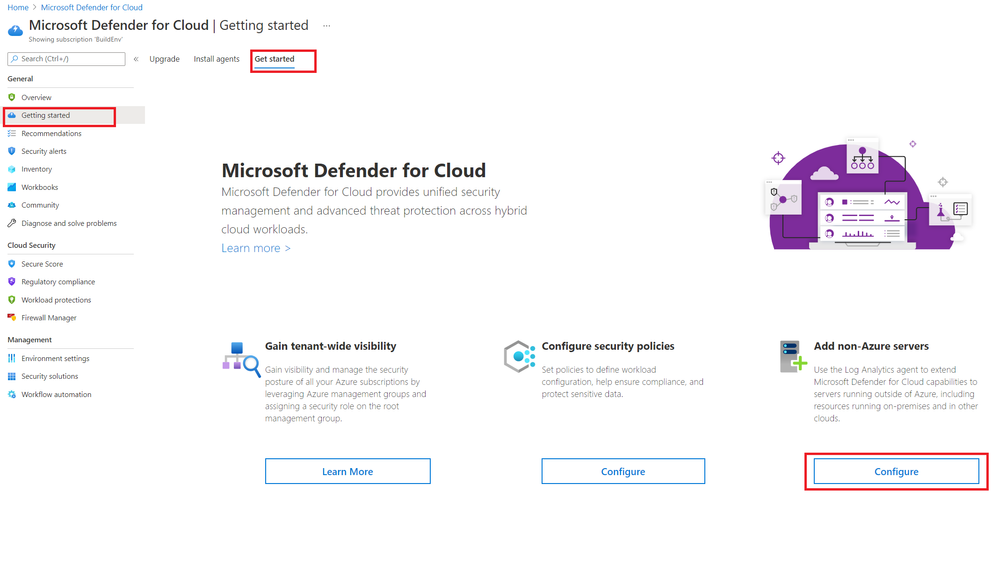
To extend visibility and Defender for Cloud capabilities, we can install the agent on computers running outside of Azure, including resources running on-premises and in other clouds.
When installing the direct agent, we will need to supply two parameters:
- Workspace ID to connect the VM to your respective log analytics workspace
- Workspace secret key, for authentication
Here is how you obtain and install the Direct Agent from the Microsoft Defender for Cloud portal:
For additional details on how to extend visibility for resources running outside of Azure, please refer to the following links:
Onboard Windows Computers to Microsoft Defender for Cloud
Onboard Linux Computers to Microsoft Defender for Cloud
Log Analytics Agent Extension
The extension installs the Log Analytics agent on Azure virtual machines and enrolls virtual machines into an existing Log Analytics workspace.
For details on supported Windows and Linux operating systems, check out the following documents:
https://github.com/Microsoft/OMS-Agent-for-Linux#64-bit
Methods to deploy the Log Analytics Agent extension
- Microsoft Defender for Cloud automatic provisioning - In reality, with auto provisioning, Defender for Cloud creates a new resource group and default workspace in that geolocation and connects the agent to that workspace. The naming convention for the workspace and resource group is:
Workspace: DefaultWorkspace-[subscription-ID]-[geo]
Resource Group: DefaultResourceGroup-[geo]
For additional details, read the data collection document.
Advantages:
- The automatic installation process run every ~15mins, your resources are quickly secured
- Automatic discovery of any new and existing VM’s - Any new or existing VM without the Log Analytics agent extension, will have it provisioned and connected.
- Microsoft Defender for Cloud can automatically create a new workspace if you choose to use default workspace. However, you also have the option to use an existing workspace.
- Data collected from Azure VMs will be stored in the workspace created by Defender for Cloud or the workspace specified.
Disadvantages:
- Does not work with VMSS server (virtual machine scale set)
- Does not support VM exclusion – if you do not want to install the agent on specific VM for some reason, this method will not let us, and it will try to install it time after time.
- Manual installation – you can only install the agent on single VM by opening log analytics relevant workspace, select one VM's and connect it to the workspace, by doing so you will install the extension on the VM.
Advantages:
- Time to deploy - the installation process starts as soon as you click on the connect button.
- VM Exclusion – flexibility and control to choose which resources you want to onboard and those you want to exclude
Disadvantages:
- Does not support scalability, will need to deploy separately on each resource
- No mechanism to discover new resources
- Does not work with VMSS server (virtual machine scale set)
- Azure policy – you can assign a built-in policy at the management group, subscription, or resource group level that will deploy a new Log Analytics agent extension on a new resources.
Log Analytics Agent Extension Policy Definitions
Below is an example of Linux policy assignment
Linux Policy Assignment
Advantages:
- Automatic Discovery
- Provisioning process is very quick (It is quick for the deployment, but the policy evaluation runs every 30 min, give or take :smiling_face_with_smiling_eyes:Visibility into agent compliance
- Supports Virtual Machine Scale Sets (VMSS)
Disadvantages:
- You will need to define a workspace within the policy assignment as a target workspace (Microsoft Defender for Cloud will not create the default workspace in this method)
- Does not work for existing VM’s - only in a green field scenario.
4.ARM template – We can integrate the Log Analytics agent extension to a VM creation process by leveraging ARM template.
Template Example for Log analytics agent (MMA extension) installation of Windows VM, this part should integrate in VM deployment template:
Advantages:
- Automated fashion
- Virtual Machines are protected from the creation time
- Full integration with your existing CI/CD tools.
- If you have used ARM template before, it is very straightforward process
Disadvantage:
- If you have never used ARM template, it requires expertise to build an ARM template
PowerShell installation - Link for example scripts
5. System Center Configuration (SCCM)
Advantages:
- Deployment at large scale
- Able to retrieve rich reports about installation status
- Seamless process to update the agent
Disadvantage:
- Certain versions of SCCM lack support of Linux machines
6. SCOM Agent
- If you already have an existing deployment of SCOM agents that are connected to a SCOM management serve, you can leverage the same agents and connect the SCOM management server to the log analytics workspace.
Benefits of Using the Log Analytics agent extension
The recommended practice is to utilize the Log Analytics VM extension. The Log Analytics VM extension has the following advantages over using the Direct Agent:
- The lifecycle of the VM extension can be managed through ARM templates, Azure CLI and PowerShell, including installing, updating and removal of the VM extension
- Installing the Direct Agent requires interacting with the VM, manually or through an Enterprise Management Solution, like System Center Configuration Manager.
- The Log Analytics VM extension will be automatically updated and will therefore always run the latest version of the agent
In this blogpost, we provided details on the options available to provide protection for your hybrid resources and the advantage and disadvantage. For more information on how Microsoft Defender for Cloud provides co visit our documentation below:
Microsoft Defender for Cloud Documentation
Kudos to @Yaniv Shasha for the great collaboration! ![]()
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.