- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity Blog
- Apply M365 Sensitivity Labels across your data assets in Azure Purview
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
One of the biggest challenges organizations face in ensuring compliant and governed data usage is knowing where and what types of sensitive data exists in their environment. Data continues to grow at exponential rates as does the demand for data-driven business insights. Concurrently, the rising slate of industry regulations and security threats makes this understanding a critical requirement for businesses to survive and thrive in these unprecedented times!
Sensitive information could live in a PDF or a Word document file, within SharePoint or OneDrive; or in operational and analytical data stores. Until the advent of Azure Purview, sensitivity labels in Microsoft Information Protection was a reliable way to tag and protect your organization's productivity data, such as emails and files, while making sure that user productivity and their ability to collaborate isn't hindered.
With Azure Purview, you can now extend the reach of Microsoft 365 sensitivity labels to operational and analytical data! Label Power BI workspaces and database columns with the same ease as labelling a word doc, thanks to Azure Purview!
Interested in getting started? Read on!
Page 1: Define labels in Microsoft Information Protection.
1. If your organization is a Microsoft 365 E5 customer, you already have the right licenses in place. Also likely that your compliance team already has a set of sensitivity labels defined that you can find in the Microsoft 365 Security and Compliance Center.
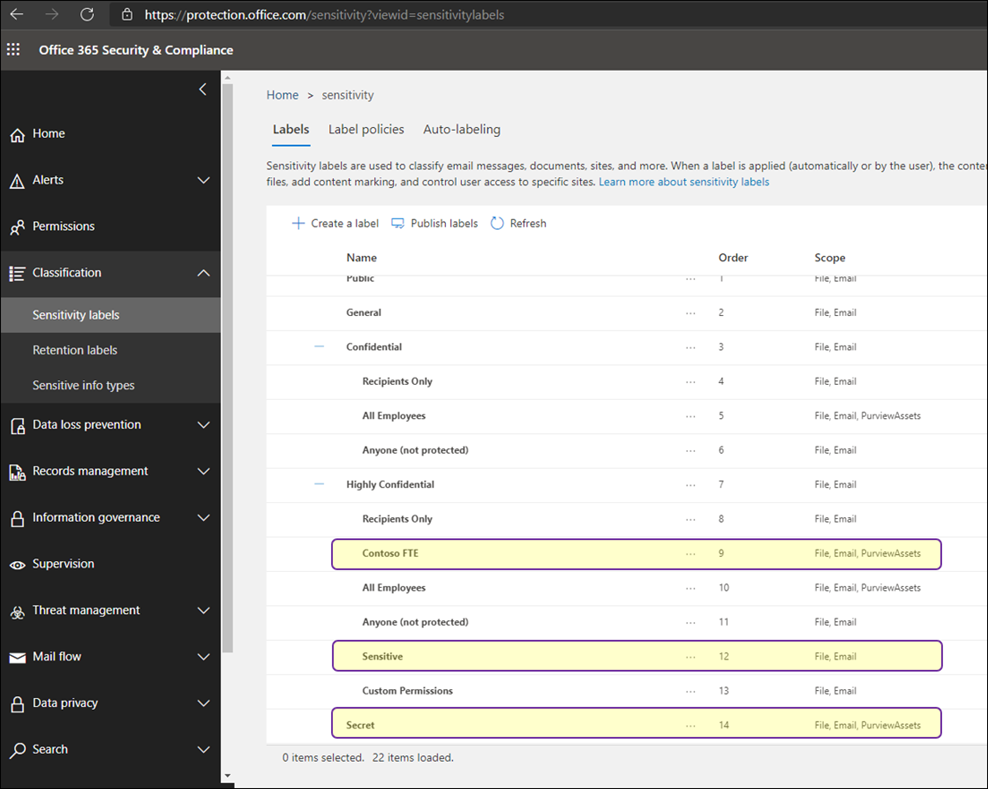
2. Identify your existing labels or create new labels if you don't have any Sensitivity Labels in M365. Create and name your sensitivity labels according to your organization's classification taxonomy for different sensitivity levels of content. Use common names or terms that make sense to your users. If you don't already have an established taxonomy, consider starting with label names such as Personal, Public, General, Confidential, and Highly Confidential. You can then use sublabels to group similar labels by category. When you create a label, use the tooltip text to help users select the appropriate label.
Examples of Sensitivity Labels:
Personal, Public, General, Confidential, Highly Confidential
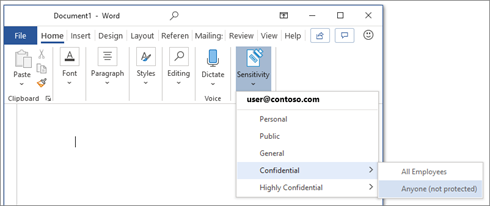
3. Once labels are published through a policy for all or certain users, they can assign them to the files and emails.
You can also edit or remove existing labels or create your own custom labels such as Highly Confidential\Contoso FTE and Highly Confidential\Sensitive and Secret in the example below.
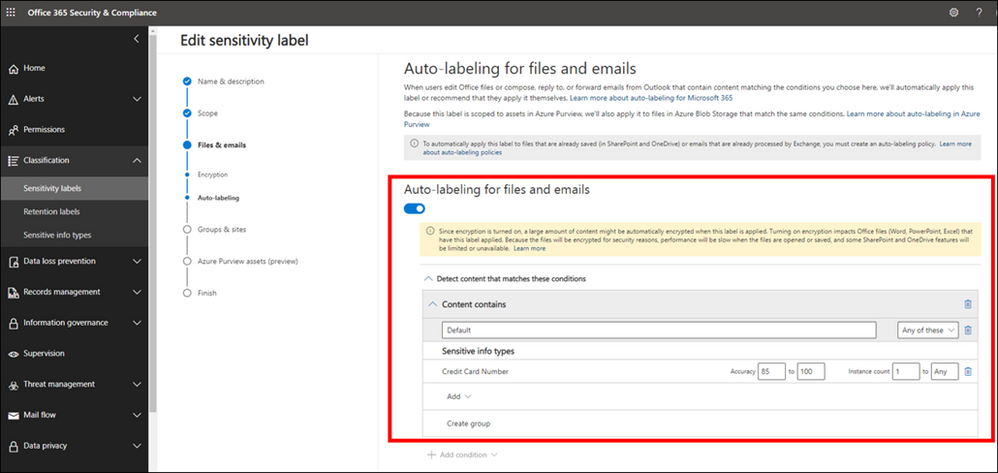
While you can give the option to users to assign published labels to their files themselves, you can also configure auto-labeling rules to assign a label to a file based on certain conditions. For example, make the file labeled as Sensitive if they contain Credit Card Number. You can also define priority for your labels, the most generic labels on the top of the list and more restrictive labels on the bottom.
Page 2: Extend M365 Sensitivity Labels in Azure Purview
1. Prerequisites
- An Azure Active Directory tenant
- A Microsoft M365 E5 active license
- An Azure Purview Account in your Azure Subscription
2. To start using your M365 Sensitivity Labels in Azure Purview, you need to follow few steps.
- In Azure Portal: Make sure you have an Azure Purview account or create a new Azure Purview Account in your Azure Subscription.
- In Azure Purview Studio: Register your data sources. Common supported data sources in Azure Purview that also support automatic labeling are:
- On-premises SQL Servers
- Azure SQL Database
- Azure Storage
- Azure Data Lake Storage Gen 1 and Gen 2
To apply Labels to OneDrive and SharePoint you still need to use Microsoft 365 Sensitivity Labels directly.
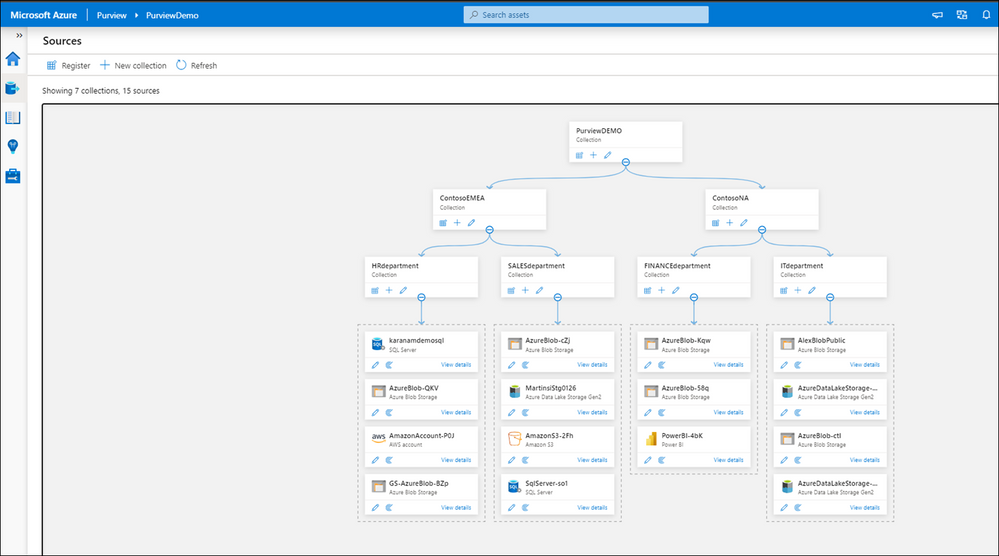
3. After registering your data sources you should be able to see existing sources and update your data catalog through Azure Purview Studio.
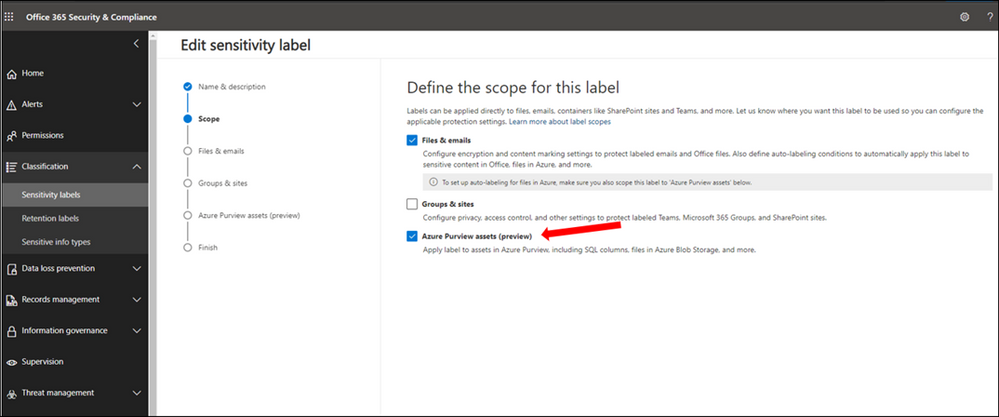
4. In Microsoft 365 Security and Compliance Center consent extending labels to Azure Purview. This is a one-time action and needed before any labels can be used in Purview:
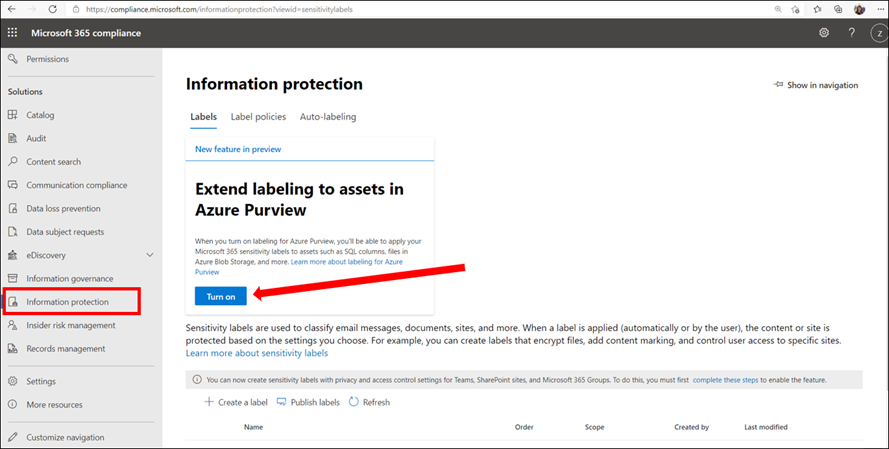
6. Configure Auto-labeling Rules
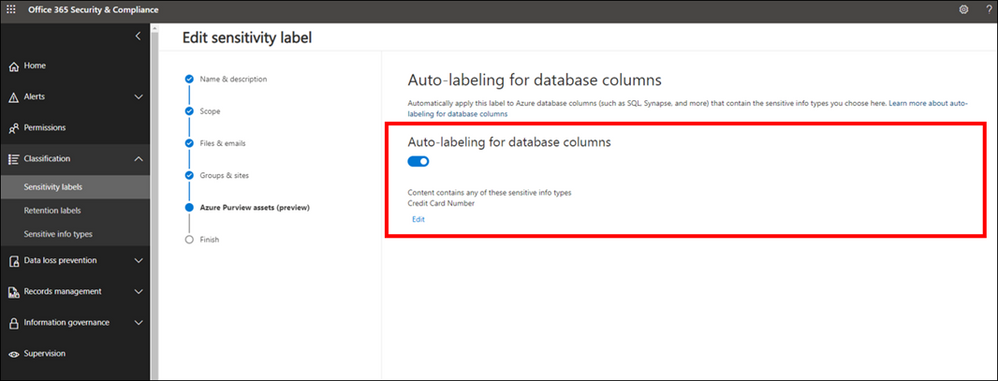
7. Turn on Auto-labeling for database columns
8. In Azure Purview Studio, Start a new scan of your assets in Azure Purview. The new scan is needed so Azure Purview can detect and automatically assign the labels to the metadata if they meet the extended any Sensitivity Labels conditions. You can launch a manual scan or schedule a regular scan of your data sources. It is highly recommended to schedule regular automatic scans, so any changes in data state is detected by Azure Purview and reduce manual overhead for your data curators.
9. Search the Azure Purview Data Catalog or use Sensitivity Labels Insights to view data assets and their assigned sensitivity labels.
Page 3: Explore Sensitivity Labels in Azure Purview
We are now set up and ready to navigate data and their Sensitivity Labels in Azure Purview Studio. Azure Purview Data Map powers the Purview Data Catalog and Purview data insights as unified experiences within the Purview Studio.
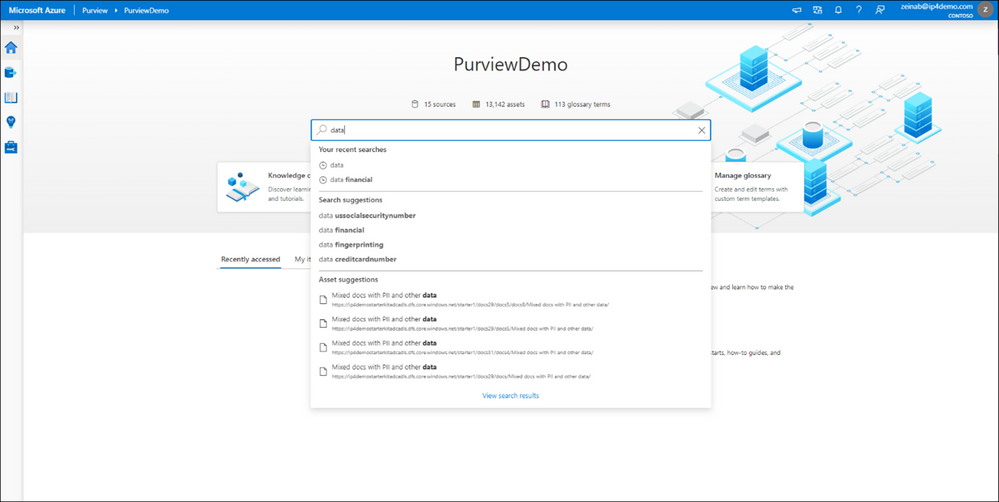
Option 1: Search the Azure Purview Data Catalog
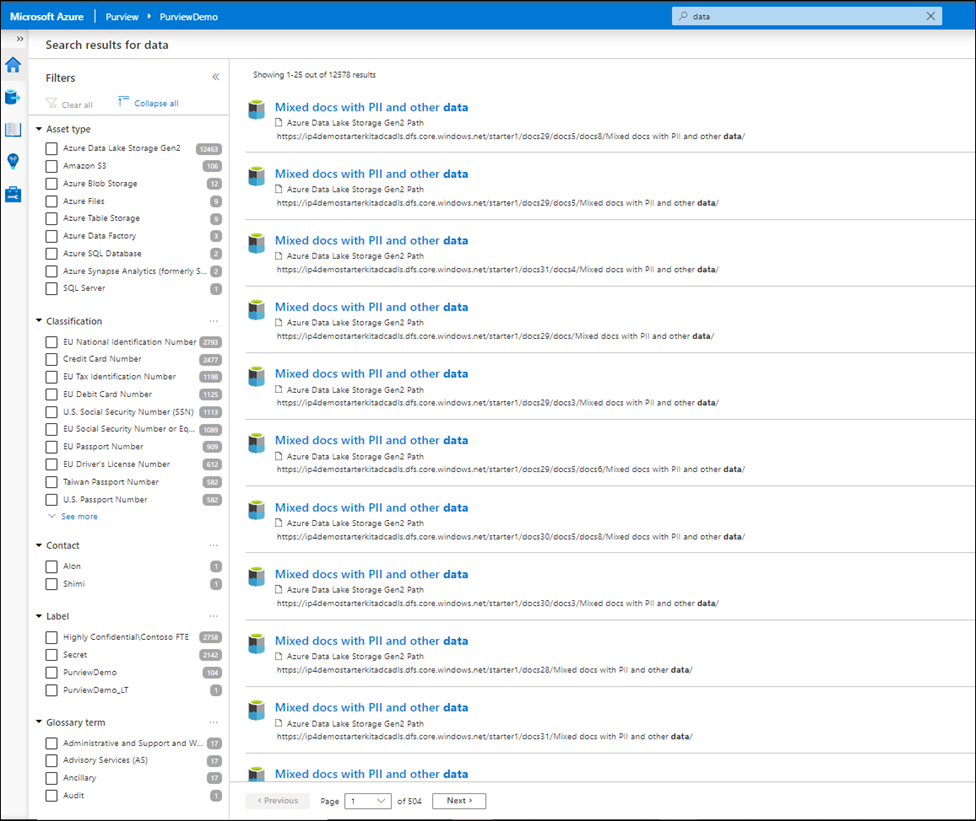
Once you register your data sources and the scan is completed, you can use Search Data Catalog from Azure Purview Studio to lookup for data assets using any terms or keywords. Let's take a look and search for data. As you type the characters, the data map provides recent searches and a list of matching search terms as Search Suggestions.
Awesome! There are over 12,000 results and it took just few seconds to get the results. To narrow down the search, you can apply one or multiple filters using any of these categories:
- Asset Type
- Classification
- Label
- Contact
- Glossary term
For subject matter experts, data stewards and officers, the Purview Data Catalog provides data curation features like ability to search and browse assets by any business or technical terms in the organization and gain visibility across data assets in your organization quickly!
Narrowing down the filter you can select any listed label and the search result automatically gets updated accordingly.
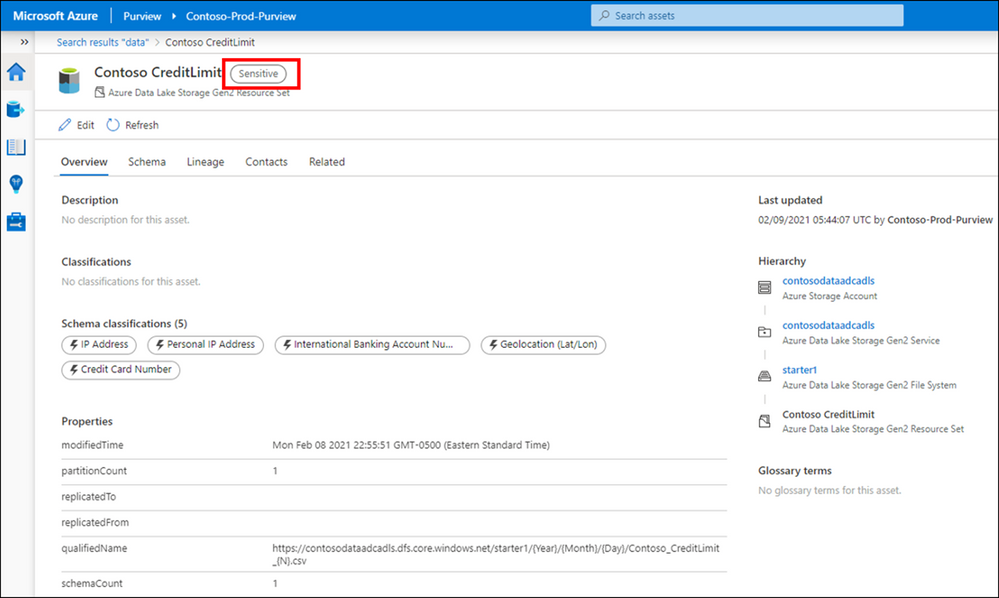
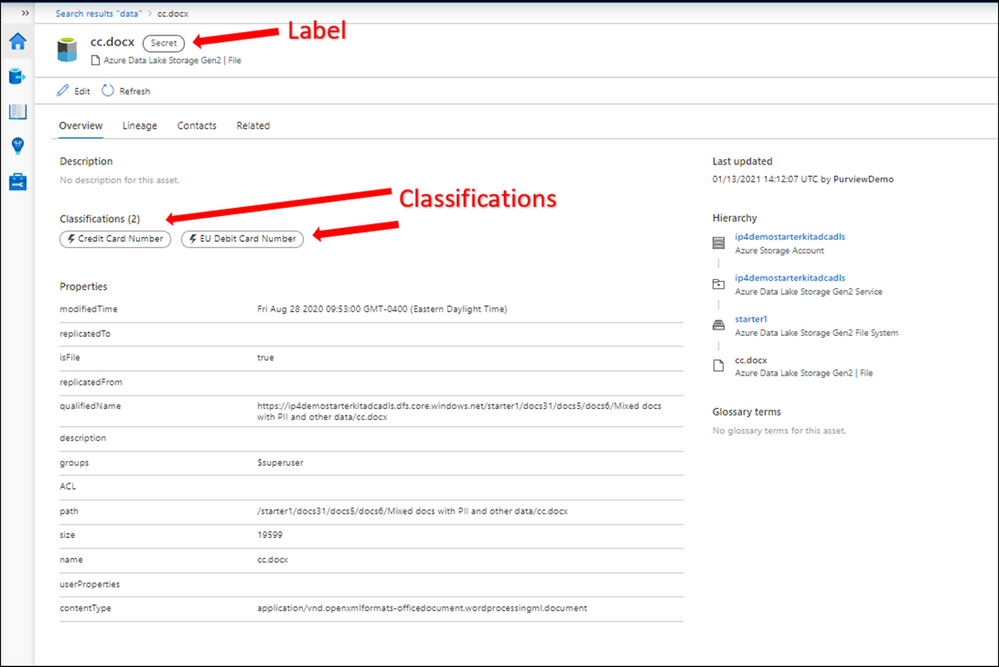
Let’s select a label such as Secret and then select one of the assets from the results to navigate into its metadata. The data is automatically labeled as Secret and the reason is because it contains a piece of information that matches with the M365 labeling rule. In this case Credit Card Number. You can use Edit button to modify the Classifications, Glossary terms and Contact, however you cannot modify labels as they are assigned automatically based on the condition. Please note that Labels for files are only applicable in the catalog and not in the original location at this point!
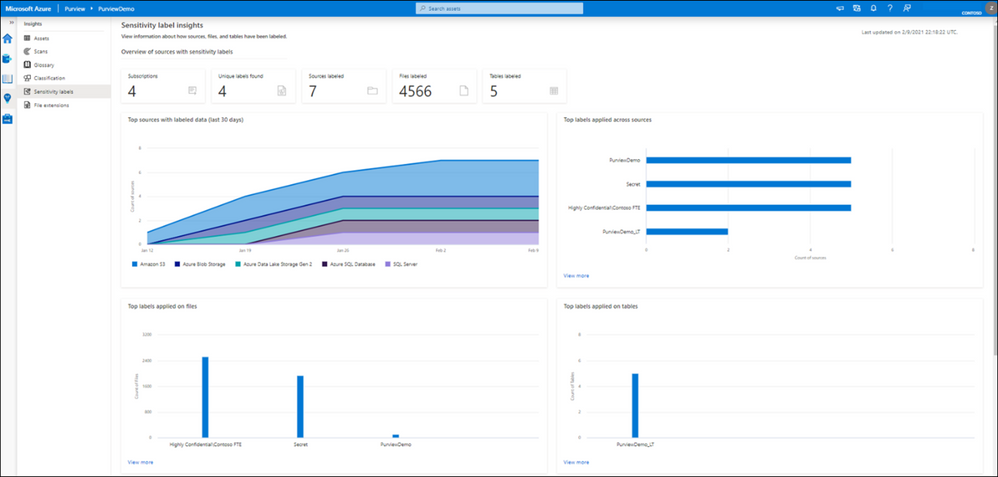
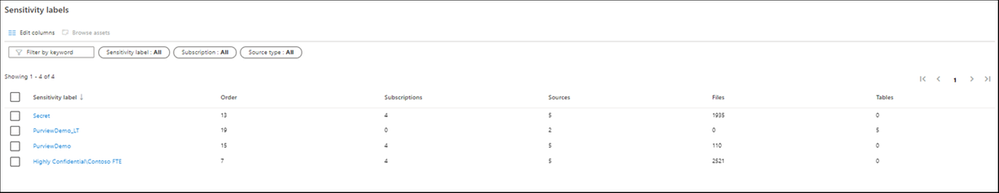
Option 2: Use Sensitivity Labels Insights
If you are looking for a bird's eye view of your data estate, you can use Azure Purview Insights. Data and security officers can get an overview and telemetry around data sources and sensitivity labels across data estate and get an answer for these questions:
- How many unique labels are found?
- How many sources, files and tables are labeled?
- What are the top sources with labeled data?
- What data types labels are applied to?
- What are the common labels used across data?
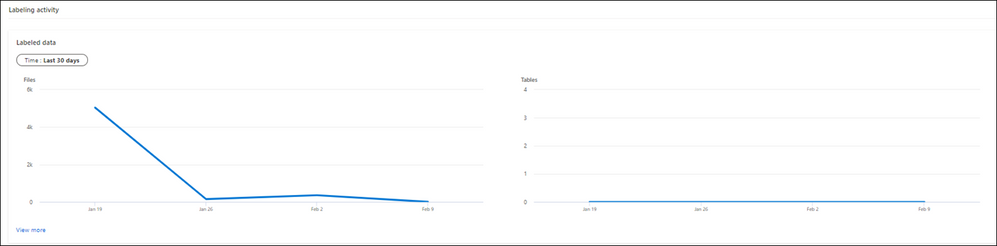
You can also view quickly what the trend related to label assignments is over the last 24 hours, 7 or 30 days on your files and tables.
To obtain more detailed information, you can click on view more on any of the titles.
Supported data types for Sensitivity Labels in Azure Purview
We currently support Automatic Labeling in Azure Purview for the following data types:
|
Data type |
Sources |
|
Automatic labeling for files |
- Azure Blob Storage - Azure Data Lake Storage Gen 1 and Gen 2 |
|
Automatic labeling for database columns |
- SQL server - Azure SQL database - Azure SQL Database Managed Instance - Azure Synapse - Azure Cosmos DB |
You can review the list later as we will add support for more data types in near future.
Summary and Call to Action
Through close integration with Microsoft Information Protection offered in Microsoft 365 Azure Purview enables direct ways to extend visibility into your data estate, and classify and label your data.
We would love you hear your feedback and know how Azure Purview helped tracking your sensitive data estate using automatic labeling.
- Create an Azure Purview account now and extend your M365 Sensitivity Labels across your files and database columns in Azure Purview.
- Use Sensitivity Labels Insights to get a bird’s eye view of your data estate by the sensitivity labels.
- Learn more about Azure Purview Autolabeling and Sensitivity Label Insights.
- Provide your feedback.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.