- Home
- Azure
- Azure PaaS Blog
- API Management Policy to perform Azure Storage File Shares operations
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
APIM Policy to perform Azure Storage File Shares operations
In Azure API Management, policies are a powerful capability of the system that allow publishers to change the behavior of APIs through configuration. Policies are a collection of Statements that are executed sequentially on the request or response of an API.
Reference Article: https://docs.microsoft.com/en-us/azure/api-management/api-management-howto-policies
Azure APIM policy expressions can also be used to perform operations such as Get, Create, Update and Delete on Azure Storage File Shares. In order to achieve this, we would require an inbound policy in the API operation configuration.
The steps for setting up the same are as below
Steps to add inbound policy to create a file in File Shares –
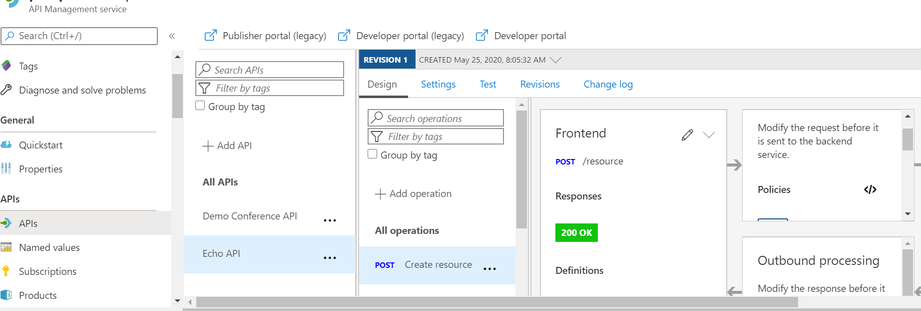
- Go to the API Management Service and select the APIs blade. Then choose the target API from the All APIs list.
-
This will populate the underlying Operations associated with the chosen API.
For this demo, we are using the sample Echo API which can be imported to your APIM service using the OpenApiSpecification URL linked below:
https://conferenceapi.azurewebsites.net/?format=json
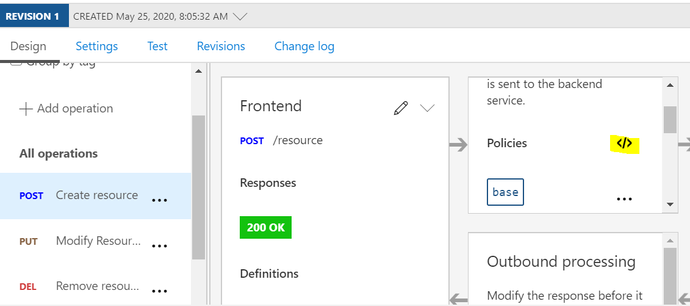
Select POST (Create Resource) from the API operations list, as highlighted in the screenshot below:
- Click on the </> sign to enter Edit mode and insert the new policy like in the below screenshot.
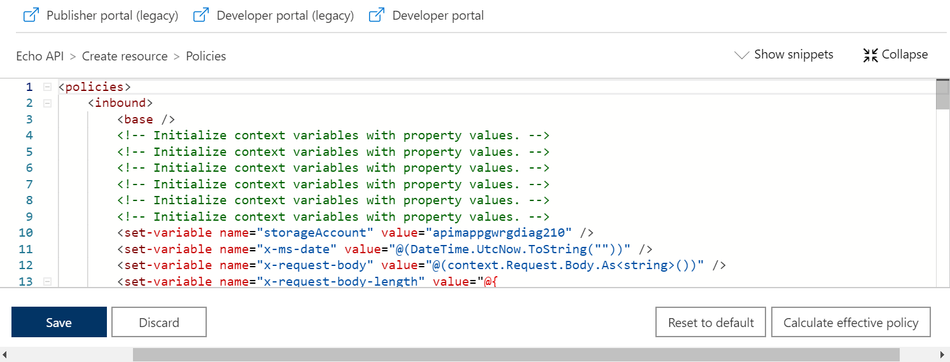
- Copy the below policy definition and paste in between the <inbound ></inbound> tags. Update the highlighted values with your Storage account details and save. Please make sure all the required headers are in the same format as below.
<inbound>
<base />
<!-- Initialize context variables with property values. -->
<set-variable name="storageAccount" value="NameOfYourStorageAccount" />
<set-variable name="x-request-body" value="@(context.Request.Body.As<string>())" />
<set-variable name="x-request-body-length" value="@{
return (string)context.Request.Headers.GetValueOrDefault("Content-Length","0");
}" />
<send-request mode="new" response-variable-name="tokenstate" timeout="2" ignore-error="true">
<set-url>@{
return string.Format("https://{0}.file.core.windows.net/NamOfYourFileShares/FileNamewithextension?SASToken ",(string)context.Variables["storageAccount"]);
}</set-url>
<set-method>PUT</set-method>
<set-header name="x-ms-type" exists-action="override">
<value>file</value>
</set-header>
<set-header name="x-ms-file-permission" exists-action="override">
<value>inherit</value>
</set-header>
<set-header name="x-ms-file-attributes" exists-action="override">
<value>none</value>
</set-header>
<set-header name="x-ms-file-creation-time" exists-action="override">
<value>now</value>
</set-header>
<set-header name="x-ms-file-last-write-time" exists-action="override">
<value>now</value>
</set-header>
<set-header name="x-ms-content-length" exists-action="override">
<value>65336</value>
</set-header>
</send-request>
</inbound>
4. After saving the policy definition, maneuver to the Test tab of the same API. Select the updated API operation and click on Send. Upon successful authentication, you would receive a 200 OK response and the Ocp-Apim Trace would show a response code 201(Created).
- The new created file can be viewed in the File Shares –
- In case, we want to do the error handling we can add the on-error section to track the error responses as well. We need to add this block after outbound closing tag. This will give use information about the related errors. Reference link for APIM error handling- https://docs.microsoft.com/en-us/azure/api-management/api-management-error-handling-policies
<on-error>
<set-header name="ErrorSource" exists-action="override">
<value>@(context.LastError.Source)</value>
</set-header>
<set-header name="ErrorReason" exists-action="override">
<value>@(context.LastError.Reason)</value>
</set-header>
<set-header name="ErrorMessage" exists-action="override">
<value>@(context.LastError.Message)</value>
</set-header>
<set-header name="ErrorScope" exists-action="override">
<value>@(context.LastError.Scope)</value>
</set-header>
<set-header name="ErrorSection" exists-action="override">
<value>@(context.LastError.Section)</value>
</set-header>
<set-header name="ErrorPath" exists-action="override">
<value>@(context.LastError.Path)</value>
</set-header>
<set-header name="ErrorPolicyId" exists-action="override">
<value>@(context.LastError.PolicyId)</value>
</set-header>
<set-header name="ErrorStatusCode" exists-action="override">
<value>@(context.Response.StatusCode.ToString())</value>
</set-header>
<base />
</on-error>
Sample response for an unauthorized operation upon integrating error-handling:
Similarly, we can perform other operations like UPDATE and GET by modifying the required headers into the policy.
Reference link for File Share operation APIs - https://docs.microsoft.com/en-us/rest/api/storageservices/operations-on-files
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.