- Home
- Azure
- Azure Observability
- Query Log Analytics Workspace for IP
Query Log Analytics Workspace for IP
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Aug 14 2019
12:43 PM
- last edited on
Apr 07 2022
06:02 PM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 14 2019
12:43 PM
- last edited on
Apr 07 2022
06:02 PM
by
TechCommunityAP
I want to query a specific log analytics workspace for an IP address .
- Labels:
-
Azure Log Analytics
-
Azure Monitor
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 15 2019 02:13 AM
You could do a simple (but inefficient) search - please edit to match your IP address.
search "192.168"
If you know the Table that contains the data that really helps? This next query brings back all the Tables that contain the IP address, if you don't already know them, that way we can now just search within a Table to improve the query time efficiency.
search "192.168"
| summarize count() by Type
The results of query #2, the Type Column list the Tables that have 192.168* in them.
| Type | count_ |
|---|---|
| WindowsFirewall | 97742 |
| NetworkMonitoring | 125670 |
| AzureNetworkAnalytics_CL | 40 |
Now we know the three Tables that have that IP Address, you can just get (for example) 10 rows of data that match that IP.
WindowsFirewall
| search "192.168"
| limit 10
Results of Query 3 (I just show one row for clarity):
| $table | TenantId | SourceSystem | Computer | TimeGenerated | CommunicationDirection | FirewallAction | Protocol | SourceIP | DestinationIP | RemoteIP | SourcePort | FullDestinationAddress | DestinationPort | RequestSizeInBytes | Info | MG | TimeCollected | ManagementGroupName | MaliciousIP | IndicatorThreatType | Description | TLPLevel | Confidence | Severity | FirstReportedDateTime | LastReportedDateTime | IsActive | ReportReferenceLink | AdditionalInformation | MaliciousIPLongitude | MaliciousIPLatitude | MaliciousIPCountry | Type | _ResourceId |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| WindowsFirewall | b438b4f6-912a-46d5-9cb1-b44069212abc | OpsManager | ContosoAppSrv1 | 2019-08-15T06:33:10Z | SEND | ALLOW | ICMP | 10.6.0.28 | 192.168.1.4 | 192.168.1.4 | null | 192.168.1.4 | null | null | 00000000-0000-0000-0000-000000000001 | 2019-08-15T08:59:58.86Z | AOI-b438b4f6-912a-46d5-9cb1-b44069212abc | null | null | null | WindowsFirewall | /subscriptions/e4272367-5645-4c4e-9c67-3b74b59a6982/resourcegroups/contosoazurehq/providers/microsoft.compute/virtualmachines/contosoappsrv1 |
I can see 3 columns that have that data, you don't say what you want to do with it when found, maybe something like this, which filters on a particular column (DestinationIP) again improving the query execution?
WindowsFirewall
| where DestinationIP == "192.168.1.4"
| summarize count() by Computer
Run the above query from here: Go to Log Analytics and Run Query
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 23 2019 07:30 AM
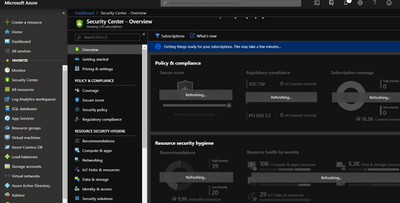
thank you for hyour help. The query can be simple and broad or granular. Also is there a default workspace associated withthe MS Azure security center widget. Where you can see all security alerts for your instance. Where are those logs stored? or is unique for each setup?