- Home
- Azure
- Azure Compute
- Login to Windows virtual machine in Azure using Azure AD authentication (and the pitfalls)!
Login to Windows virtual machine in Azure using Azure AD authentication (and the pitfalls)!
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 05 2022 07:15 AM - edited Aug 09 2022 06:45 AM
Dear Microsoft Azure Friends,
This article is about the login to Windows virtual machine in Azure using Azure Active Directory authentication and what needs to be considered in the process. This article describes the procedure. So far, everything is actually in perfect order.
https://docs.microsoft.com/en-us/azure/active-directory/devices/howto-vm-sign-in-azure-ad-windows
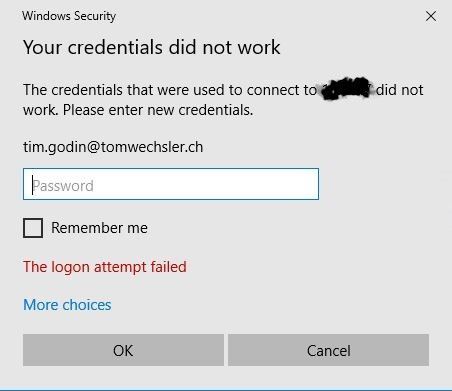
So I have worked through the steps and now I want to log on to the virtual machine with an Azure Active Directory account.
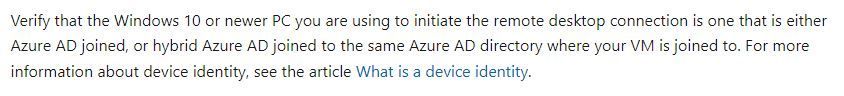
Why does this error message appear now? Have I done something wrong? I am going through all the steps again. No fits. So I take another close look at the article and discover the following:
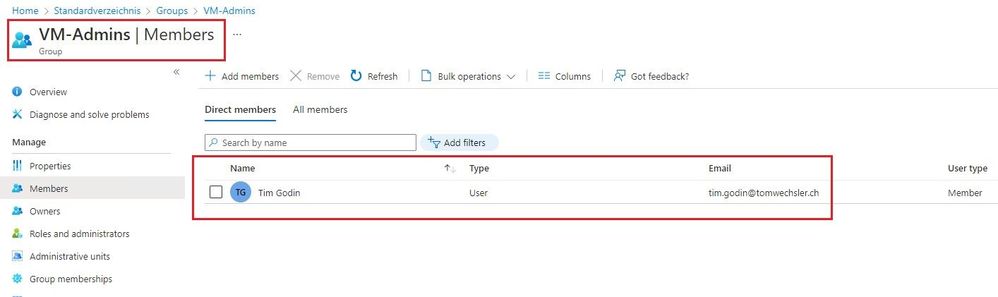
But that's exactly not the case with me. I want to connect from my local system which is not registered or joined in Azure. Let's take it one step at a time. First of all, I create a group in Azure Active Directory. This will contain the account I will use later for the login.
ATTENTION: Use the appropriate Windows OS => Windows Server 2019 Datacenter edition and later or Windows 10 1809 and later
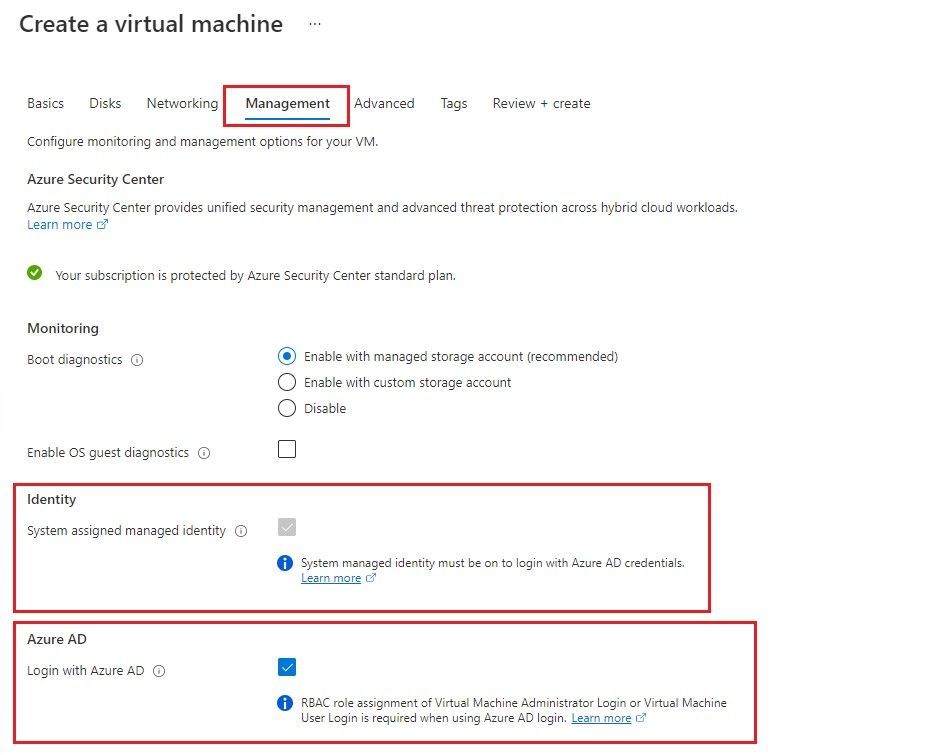
Next I create a new virtual machine with the default settings (including a public IP address and yes this is not good, but this demo absolutely OK). Except for Management I set the following settings.
If you want to work with an existing virtual machine you need to install the extension. You can do this with the Azure Cloud Shell, in a Bash terminal.
az vm extension set \
--publisher Microsoft.Azure.ActiveDirectory \
--name AADLoginForWindows \
--resource-group YourResourceGroup \
--vm-name YourVM
After the virtual machine is created we need to work with Role based Access Control RBAC. There are two roles that can be used.
Virtual Machine Administrator Login
or
Virtual Machine User Login
If you need local admin rights you need the first role. If you want to log in as a standard user, you can work with the second role.
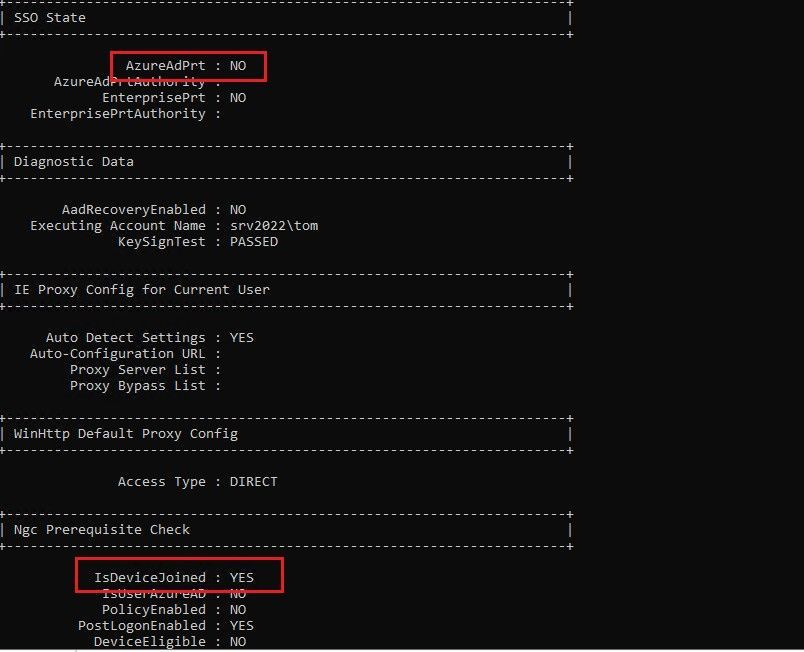
Now we connect to the virtual machine using RDP, but ATTENTION, I use the account I created when I created the virtual machine (not an Azure AD account). In the virtual machine I start the command prompt and use dsregcmd /status. The machine is Azure AD Joined.
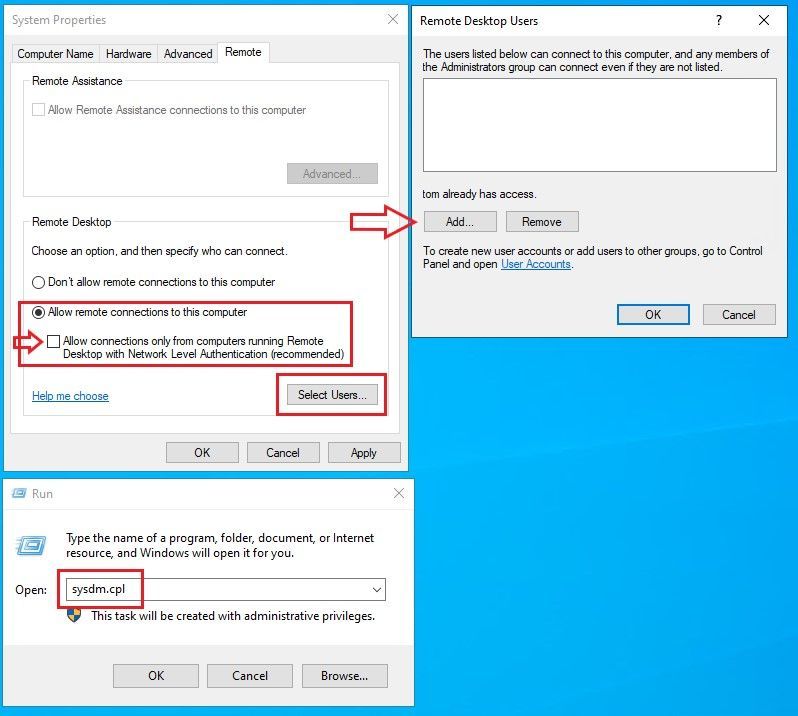
In the virtual machine, navigate to Start and invoke "run". Type sysdm.cpl and navigate to the Remote tab. Remove the "Allow connections..." option and click "Select Users".
When you click on "Locations" you will immediately see that you cannot select an account from Azure AD. We need the command prompt for this.
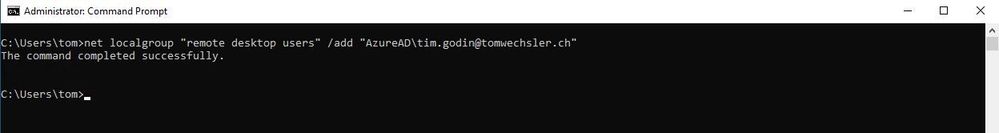
Start the command prompt with elevated privileges and enter the following (customized with your information, of course).
net localgroup "remote desktop users" /add "AzureAD\Email address removed"
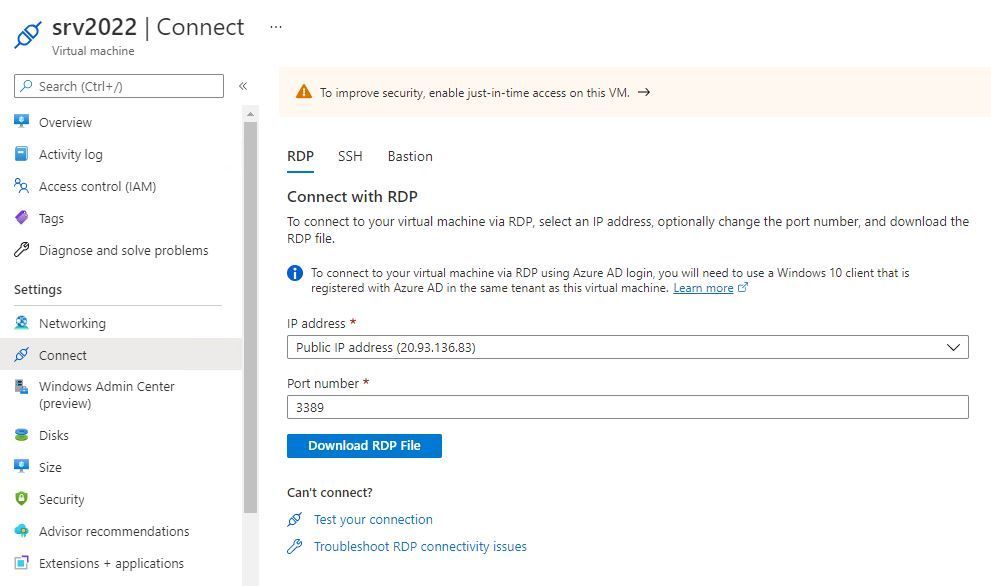
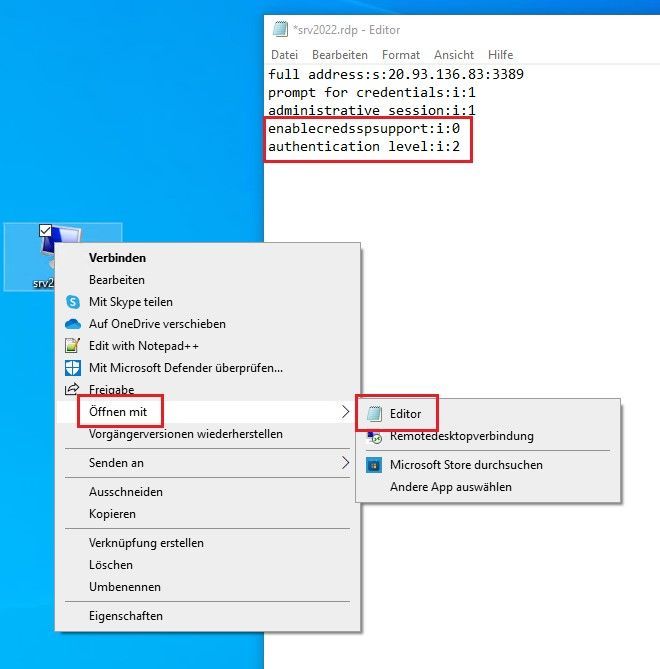
Go back to the Azure Portal to your virtual machine. Download the RDP connection file.
Open this RDP file with an editor and add the following lines.
enablecredsspsupport:i:0
authentication level:i:2
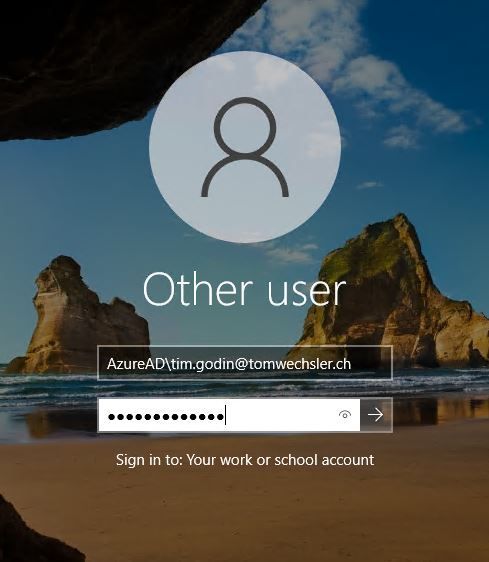
Now double click on the RDP connection file and now use the Azure account for login. AND BINGO, we can now log in to our virtual machine using the Azure Active Directory account! Cool!
I hope this article was useful. Thank you for taking the time to read the article.
Best regards, Tom Wechsler
P.S. All scripts (#PowerShell, Azure CLI, #Terraform, #ARM) that I use can be found on github! https://github.com/tomwechsler
- Labels:
-
Compute
-
Hands-on-Labs
-
virtual machine
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 25 2022 12:41 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 25 2022 10:24 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 05 2022 08:32 AM
@TomWechsler
Thank you for this detailed post! The amount of hoops that you have to jump through is outrageous for what really should be fairly simple authentication.
The fact that we have to disable MFA without W10 Hello for Business deployed is crazy to me, and there are many intricate steps that must be performed "just so" to get this working. Even more outlandish is that the official MS KB article fails to mention a couple of these finer details and will leave you unable to get this working without a significant level of research and troubleshooting.
I wish I would have found your post a week ago! Lifesaver!!!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 05 2022 08:37 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 19 2022 03:38 AM
Reality = Oh man ..
Kidding aside, this is a really helpful article. Thank you!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 19 2022 08:58 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 01 2022 10:53 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 01 2022 10:24 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 23 2022 03:27 PM
I do think it should be noted that these settings do have security implications.
https://docs.microsoft.com/en-us/windows/win32/secauthn/credential-security-support-provider
Caution
CredSSP authentication delegates the user credentials from the local computer to a remote computer. This practice increases the security risk of the remote operation. If the remote computer is compromised, when credentials are passed to it, the credentials can be used to control the network session.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 23 2022 09:54 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 13 2022 09:09 AM
After editing the RDP-file and adding your two lines, I'm getting the following error on my clients: "Remote computer requires network level authentication. That function isn't supported by your computer."
I tried it from "Windows Server 2022" and from "Windows 10". Both systems supporting network level authentication...
Any idea?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 13 2022 09:56 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 14 2022 02:29 AM
thanks a lot for your quick answer! Now it's working without problems... :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 14 2022 07:48 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 09 2022 03:51 AM
Hallo Tom,
super Artikel, danke dafür genau das war heute und gestern mein Thema.
Muss ich das alles auch machen wenn ich in Azure einen eigenen DC mit Domäne betreibe?
danke
Gruß Philipp
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 09 2022 08:40 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 16 2022 08:51 AM
@TomWechsler Good detailed info and I had issue connecting from my local laptop and identified it is because of the GPO on local laptop https://techbrainblog.com/2022/08/12/issue-connecting-azure-vm-using-azure-ad-from-our-laptop/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 02 2024 03:41 AM - edited Apr 02 2024 04:27 AM
With doing the attached steps to add "AADLoginForWindows" under 'Extensions + applications'.
Under the VM > Go to Security heading > Identity > Turn 'System assigned' status to ON.
Then connect to the VM as local admin, run CMD - dsregcmd /status.
AzureADJoined: YES