- Home
- Security, Compliance, and Identity
- Microsoft Defender for Identity
- Sensitive groups
Sensitive groups
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 26 2018 01:50 AM
Has anyone managed to get anything meaningful from Sensitive Groups ? I thought the intent was to "monitor" those groups for membership changes. I have pushed and pulled users in and out of groups (say, Domain Admins) and I never get notified of anything !
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 26 2018 04:07 PM
This detector needs a learning period before it is active.
How long is the system deployed with this version?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 26 2018 09:25 PM
At least 8 weeks. What actually is the detector learning ? "Normal" modifications by expected admins or other sensitive users ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2018 01:35 AM
Generally yes,
wait for 2-3 more weeks, then to invoke the alert, try to modify a sensitive group using an account that does not normally do it...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2018 06:04 AM
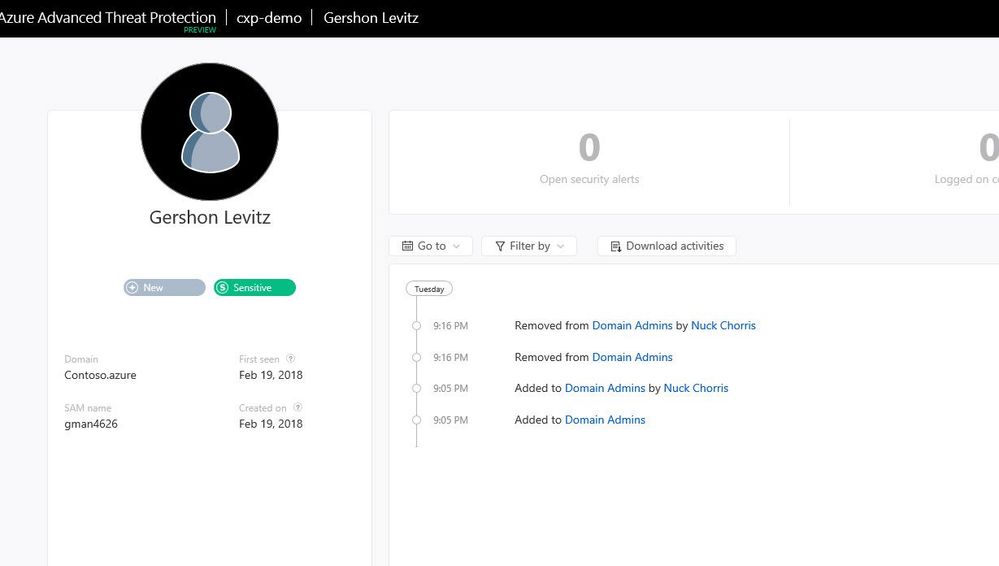
Hi Stuart,
There is a report that will show you all of the sensitive group modifications. Can you run this report and see if it has the modifications you did recently?
Thanks
Gershon
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2018 09:02 AM
The group in question (as a test) was not one that normally gets modified at all....in fact it has probably not been modified for 12 months, by anyone previously.
Yes, was aware of the report.....and there is NOTHING at all in the report, which actually would be more useful to me than a console alert. Why would it not show in the report ? Yes, auditing for group membership is nabbed, and yes, it shows on the event log.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2018 12:27 PM
Which domain group was it?
Keep in mind that in 1.8.* we are using a closed list of groups defined as sensitive.
in future version you will be able to tag yourself which groups are sensitive for you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2018 03:37 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2018 03:52 PM
Sorry, got confused with another thread.
in AATP, you can tag the entities, so it seems you gap is that you need to have at least 10 weeks of learning period.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2018 03:57 PM
10 weeks of learning, for what exactly ? To say that someone "unusual" has modified the group membership ? If this is 10 weeks to appear in the report, is pretty useless, don't you think ? What would be the point of that ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2018 04:15 PM
Yes and No.
Unlike ATA which can alert for abnormal modifications, and report on all modifications,
AATP (for now) can alert for abnormal modifications too (with the same 10 weeks learning period), but it's report will only report on previously alerted modifications, and not all of them like in ATA.
So.. if you wait 2 more weeks, and use an account that did not modify the tagged group during the learning period, you should see an alert...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 13 2018 10:43 AM
Hi Stuart,
We've reviewed the sensitive groups report and I'm pleased to let you know that all changes to the sensitive groups will now be included in the report (not just the anomalies). We expect to release the code to enable this in our next update cycle on Sunday February 18th.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 21 2018 01:05 AM
Did this make it in, as it does not seem to be working ?
Repro:
Add group to entity list
Schedule a report for sensitive groups(daily)
wait a few hours
add some random user to group
await next daily report to show said user was added
Is my expectation correct ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 21 2018 10:08 AM
Hi Stuart,
Can you make sure that the Group Events are logged?
To turn them on, please do the following:
- On the DC, open gpme.msc.
- Navigate to : Domain Controllers.<domain name> --> Default Domain Controllers Policy.
- In that policy, navigate to the following path to configure the DC for those event auditing:
- Computer Configuration --> Policies --> Windows Settings --> Security Settings --> Local Policies --> Audit Policy
- Set the following values to "Success,Failure" :
+ Audit Account logon events
+ Audit account management
+ Audit directory service access
+ Audit logon events - gpupdate.
After that, please do the group changes in the AD. You can make sure the events are created by opening the Event Viewer (Windows Logs -> Security)
Finally, try to download the report.
If it won't work, please PM me your workspace ID (and name) and the time range (UTC) of the group members change.
Thanks,
Gal
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 25 2018 05:23 AM
In the Azure ATP console can you see the changes in the entity profile(s) of the objects in questions?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 25 2018 09:49 PM
The report works fine and Stuart got a report with attached file few days ago.
Few things to clarify regarding the detector (i.e., when the Security Alert will be triggered and will be seen in the Timeline):
- There is a learning period of 4 weeks on each DC, starting from the first group membership change (add) event.
- The admin didn’t make any change to any group on any DC during the last 10 weeks.
- Only on adding members to a group (events 4728, 4732, 4756).
- Only on sensitive group changes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 09 2020 01:51 PM
@Gal Bruchim @Eli Ofek I'm in a similar situation so I have some questions to clarify me the detector behaviour:
- if the group (i.e. Domain Admins) is modified always by the same account no alert is triggered, if another user modify the group membership I receive the alert. Is this correct?
- The learning period (4 weeks) starts from the first group membership change (add) event after the sensor installation. Is this correct?
- could you explain me better "The admin didn’t make any change to any group on any DC during the last 10 weeks."?
Thanks a lot
Mike