- Home
- Security, Compliance, and Identity
- Microsoft Defender for Identity
- How Microsoft Advanced Threat Analytics detects golden ticket attacks
How Microsoft Advanced Threat Analytics detects golden ticket attacks
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Oct 05 2017
10:10 AM
- last edited on
Nov 30 2021
10:10 AM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 05 2017
10:10 AM
- last edited on
Nov 30 2021
10:10 AM
by
TechCommunityAP
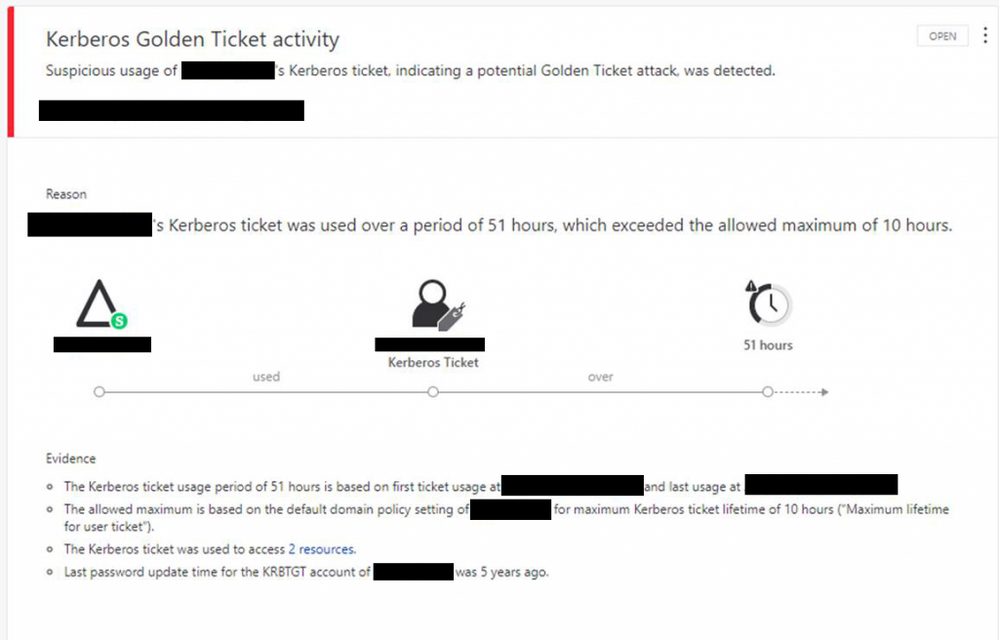
If you’re in the business of threat detection, you are probably familiar with the term “golden ticket”. For those less familiar, a golden ticket is the name of a Kerberos ticket that is manually created by an attacker after gaining access to your environment’s encryption “master key”. A golden ticket allows an attacker to masquerade as any user or gain the permissions of any role at any time they want, giving them full control over your environment.
Being able to detect this kind of attack has historically been difficult, because the adversary is leveraging credentials with the same key your Active Directory uses.
Read about in the Enterprise Mobility & Security blog.