- Home
- Security, Compliance, and Identity
- Microsoft Entra
- Re: Powershell CMDlets for MFA Settings?
Powershell CMDlets for MFA Settings?
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Feb 13 2018
12:09 PM
- last edited on
Jan 14 2022
05:35 PM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 13 2018
12:09 PM
- last edited on
Jan 14 2022
05:35 PM
by
TechCommunityAP
Does anyone know if there are Powershell Cmdlets available to allow inspection of a user's MFA settings related to which verification options were configured and which option is considered primary? I am mostly focused on Office 365, but I think that this is an Azure AD question in general.
Here's the use case that I am considering. We have a number of Office 365 users with MFA enabled. There was configuration guidance given at setup time, but not all users chose to follow that guidance. Specifically, many chose SMS notification, but our facility is notorious for poor cellular reception. Mobile app is preferred in this environment. In some cases, they deviated from the suggested method intentionally and, other times, unintentionally. This leads to support calls and it would be very useful for the support tech to know up front which methods are configured and which is the user's primary verification method.
I've looked at the Azure AD module, but haven't found what I'm looking for yet.
Thanks,
Andy Baerst
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 20 2020 10:37 AM
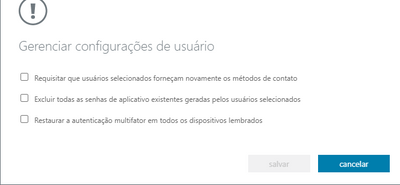
Hi, is there a way to remove the authentication once it's set?
If I by accident enable this on a user, the user is unable to remove the authentication method within Office 365, since it does require minimum one selection.
As shown in your screen shot, those won't appear on a user account that haven't been enabled.
Kind Regards,
Kaspar D.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 20 2020 10:54 AM
@Indira1390 You first have to create your input user list using something like this:
Get-MsolUser -EnabledFilter EnabledOnly -All | Export-csv "C:\downloads\userlist.csv"Then, you can create the MFA details for each user:
$filepath1 = import-csv "C:\downloads\userlist.csv"
$filepath2 = 'C:\downloads\MFA-Results.csv'
ForEach ($item in $filepath1)
{
$user = $item.("UserPrincipalName")
Get-MsolUser -UserPrincipalName $user | Where {$_.UserPrincipalName} | Select UserPrincipalName, DisplayName, Country, Department, Title, @{n="MFA"; e={$_.StrongAuthenticationRequirements.State}}, @{n="Methods"; e={($_.StrongAuthenticationMethods).MethodType}}, @{n="Default Method"; e={($_.StrongAuthenticationMethods).IsDefault}} | Export-Csv -Path $filepath2 -Append
}
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 20 2020 11:03 AM
@Kaspar_Danielsen The simplest method is via portal.azure.com. Navigate to Azure Active Directory->Users, then click Multi-Factor Authentication in the upper menu bar. Search for the username, then select it. You can then click Disable under "quick steps".
If you're using Conditional Access policies to enforce MFA, then the settings above are not used. In this case, you can remove MFA via PowerShell:
#Connect to Azure ADConnect-MsolService#Disable MFA for a user $mfa = @() Set-MsolUser -UserPrincipalName User@domain.com -StrongAuthenticationRequirements $mfa
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 20 2020 02:53 PM - edited Mar 20 2020 03:21 PM
Hi Gary,
Thank you for taking the time to answer my question.
I'm connected and ran the command. It accepted it, but both options for SMS and Call is still listed. In other words, it didn't make a change for some reason.
I don't use this command or use Office 365 to enable/disable MFA.
Set-MsolUser -UserPricipalName User@domain.com -StrongAuthenticationRequirements $mfa
When you run this command, it does show 2 or more options for SMS/Call/App etc. I wish to erase those with a command line, since it's not possible to do that manually in the users profile.
$User = Get-MSolUser -UserPrincipalName User@domain.com
$User.StrongAuthenticationMethods
Kind Regards,
Kaspar Danielsen
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 11 2020 08:23 AM
I am using below logic to extract user MFA details and default method configured., We use combined registration SSPR +MFA.
#Define global variable
$Results = New-Object System.Collections.ArrayList
# Get User list from a text file, expect user name as UserPricipalName
$Userlist = get-content d:\users.txt
Write-host "Total $(($Userlist).count) users"
#Checking each user Strong Authentication Method
$Userlist | foreach {
Write-host "Checking user: $($_) MFA status....."
$User = get-msoluser -UserPrincipalName $_
$UserStrongDetails = $User.StrongAuthenticationMethods
$UserStrongDetailsCount =$User.StrongAuthenticationMethods.count
If($UserStrongDetails){
For ($i=0; $i-lt $UserStrongDetailsCount; $i++) {if(($UserStrongDetails[$i].IsDefault) -eq $true) {
$DefaultMethod =$null
$DefaultMethod = $UserStrongDetails[$i].MethodType
break }
}
$Preresult =@{
'AAD-DisplayName' = $user.DisplayName
'AAD-UserPrincipalName' = $user.UserPrincipalName
'AAD-UsageLocation' = $user.UsageLocation
'AAD-MobilePhone' = $user.MobilePhone
'AAD-OfficePhoneNumber' = $user.PhoneNumber
'MFA-Mobile' = $user.StrongAuthenticationUserDetails.PhoneNumber
'MFA-AlternativePhoneNumber' = $user.StrongAuthenticationUserDetails.AlternativePhoneNumber
'MFA-Email' = $user.StrongAuthenticationUserDetails.Email
'MFA-DefaultMethod' = $DefaultMethod
}
}
else
{
$DefaultMethod =$null
$Preresult = @{
'AAD-DisplayName' = $user.DisplayName
'AAD-UserPrincipalName' = $user.UserPrincipalName
'AAD-UsageLocation' = $user.UsageLocation
'AAD-MobilePhone' = $user.MobilePhone
'AAD-OfficePhoneNumber' = $user.PhoneNumber
'MFA-Mobile' = "Not-Defined"
'MFA-AlternativePhoneNumber' = "Not-Defined"
'MFA-Email' = "Not-Defined"
'MFA-DefaultMethod' = "Not-Defined"
}
}
$Results += New-Object -TypeName PSObject -Property $Preresult
}
$Results | Select-Object AAD-DisplayName,AAD-UserPrincipalName,AAD-UsageLocation,AAD-MobilePhone,AAD-OfficePhoneNumber,MFA-Mobile,MFA-AlternativePhoneNumber,MFA-Email,MFA-DefaultMethod | Export-Csv -notypeinformation -Path "d:\AzureMFAUserDetails.csv"
_Sudhish Kumar
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 17 2020 09:37 PM
What i´m trying to do is more simples, but i´m unable to do:
1) Read UPNs form a textFile or csv, one UPN per line
2) set Auth methods
I´m trying this one, but it does nothing:
$listacsv = import-csv c:\temp\list.txt
foreach($upn in $listacsv) {
$method1 = New-Object -TypeName Microsoft.Online.Administration.StrongAuthenticationMethod
$method1.IsDefault = $true
$method1.MethodType = "PhoneAppNotification"
$method2 = New-Object -TypeName Microsoft.Online.Administration.StrongAuthenticationMethod
$method2.IsDefault = $false
$method2.MethodType = "TwoWayVoiceMobile"
$methods = @($method1, $method2)
Set-MsolUser -UserPrincipalName $upn -StrongAuthenticationMethods $methods
}
But insted of the sinple UPN, the returns is:
@{testuser@MYdomain.com}
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 21 2020 01:24 PM
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 22 2020 08:25 AM - edited Oct 22 2020 08:26 AM
Here is the script which does exactly what you need
https://docs.microsoft.com/en-us/samples/azure-samples/azure-mfa-authentication-method-analysis/azur...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 22 2020 08:59 AM
Here is the script which should meet your requirements
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 05 2021 07:28 AM
@Micki Wulffeld - thanks for this.
Does anyone know if it is possible to retain SMS as a unusable authentication method for a user when switch from SMS to PhoneAppOTP/PhoneAppNotification via Powershell?
At the moment when a new default sign in method (other than SMS) is defined via set-msol command it disables two-step verification for SMS rendering it void as a alternative authentication method until the user reactivates it via mysignins.microsoft.com/security-info.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 28 2021 12:18 PM
Pessoal, boa tarde!
Estou precisando criar um script na onde seja possível alterar os seguintes itens abaixo. Poderiam me ajudar? Estou procurando alguma página para orientação e não achei...
Obrigado!
- « Previous
-
- 1
- 2
- Next »