- Home
- Security, Compliance, and Identity
- Microsoft Entra
- Use FIDO2 as MFA token
Use FIDO2 as MFA token
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Sep 28 2021
09:13 AM
- last edited on
Jan 14 2022
03:24 PM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 28 2021
09:13 AM
- last edited on
Jan 14 2022
03:24 PM
by
TechCommunityAP
We are trying to replace the need to have a phone number (cellphone or office phone or authenticator app) for many of our users that refuse to use a personal phone for authentication. This is also for those users we need to setup their PC ahead of time so will not have their personal cellphones with us to authenticate during all of the setup.
We do not have P2 licenses so I cannot see a way to disable the MFA during registration (ie after we authenticate the user to Azure AD it requires the setup).
We purchased a FIDO2 USB and have enabled it in Azure but that seems to only be for passwordless security and we're still getting prompted to setup MFA. There is no option in the MFA dropdown for FIDO2 so I'm clearly missing something.
For users that will not have cellphone to authenticate to, can we configure the user to override the registration policy and only use the FIDO2 USB key if we don't have a P2 license (the option to disable the policy is greyed out)?
If we have to use a P2, can we only upgrade our Global Admin accounts to set tenant wide settings or will we literally have to upgrade every user to a P2 (which will cost us an extra $25,000 a year and is way over kill for our needs)?
We want to be secure but we don't want to have to pay $25,000 to do so. We've not had this issue when we were AD Hybrid but that local server is being tossed when we move.
- Labels:
-
Azure Active Directory (AAD)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 28 2021 10:19 AM
@luvsql Hello, it sounds to me as if you should use the (preview) Temporary Access Pass feature.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 28 2021 10:31 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 28 2021 10:54 AM
@luvsql I think I need more detailed information. What subscription do you have today? AAD P1 using CA or simply Security defaults with enforced MFA for all users? Intune and enrollment involved? What registration policy do you refer to? Can't be the MFA registration policy at least as that part of AAD P2.
The TAP is for the FIDO2 scenarios as yours making it possible to add a key to the dropdown, where it's missing right now. FIDO2 satisfy MFA but cannot be used as a second factor (at least not yet as far as I know).
Give it a try?
Temporary Access Pass is now in public preview - Microsoft Tech Community
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 28 2021 11:03 AM - edited Sep 28 2021 11:05 AM
Hi Christian,
Our user base comprises of mostly Microsoft 365 Business Standard and some Office 365 E3 licenses, which gives us the Azure AD that we use now. I know it's limited as it pertains to Domain policies, but it's still allowing us to secure with MFA etc.
We do have many users with corporate cellphones with MFA and the authenticator app and it works well, however, we do have 20% of our Employees that do not have a corporately paid cellphone (nor a desk phone) and they do not want to use for authentication (and we can't force them to). We have to pre-configure new Employees ahead of time and am trying to find a solution for these types of users that we can't use the standard authentication methods with.
When we setup a new user in Azure AD directly, there is a default policy (Security > MFA Registration Policy) that is forcing a newly authenticated laptop to setup MFA and the FIDO2 is not an option since that's setup in a different area and is linked to the passwordless feature.
We can't disable this policy for some reason (even though it says "This view is for Azure AD Premium P2 customers to setup MFA registration policy. Other customers can only disable policies here.") so am trying to find a workaround. There is no option to disable. If we disabled this registration policy then we skip right to the FIDO2 passwordless. As soon as you reboot after authenticating a device the MFA pops up.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 28 2021 01:05 PM - edited Oct 04 2021 05:19 AM
Solution@luvsql Hello again, I had to try it using security defaults as I'm pretty sure you're using that. You have no Intune, Conditional access or MFA registration policy in your subscriptions.
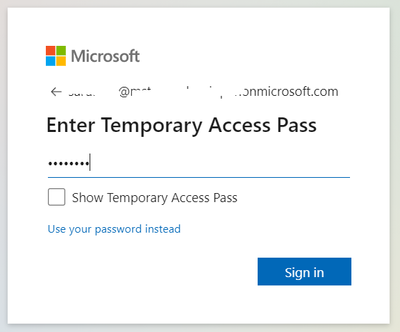
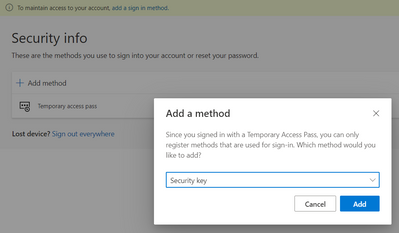
So, when simply using security defaults with enforced MFA you get the prompt to add security info/details, and can skip this for 14 days. When enabling the Temporary Access Pass policy and activating that for a newly created user in Azure AD it instead becomes the first prompt.
This is how it looks like and takes you to https://aka.ms/mysecurityinfo page where one can configure additional options, such as the security key. I could not proceed as I do not have a key to put in the laptop.
*My reply is being updated as you can actually use TAP to add a security key (as the pictures show) with security defaults. For the sake of it I even asked Microsoft who verified the method.
To wrap up the above.
1. Enable security defaults.
2. Enable TAP and assign to user.
3. User logs in using TAP and adds FIDO2 key.
4. Next sign-in when prompted for MFA user uses FIDO2 key (as FIDO2 satisfies MFA).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 28 2021 01:11 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 28 2021 01:58 PM - edited Oct 04 2021 05:10 AM
@luvsql When enabling security defaults, if having AAD Free for example, you're pushing MFA for all users. It's a great feature but not a flexible solution as you can only toggle on or off. To toggle off to onboard the few users is not an option obviously. If using AAD P1 you get conditional access and can be more granular.
I will do some more digging around this and update if necessary. Perhaps you should reach out to the official support going forward?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 29 2021 06:04 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 29 2021 06:53 AM - edited Oct 04 2021 05:22 AM
@luvsql My suggestion would be to upgrade to AAD P1 (for the conditional access) so you're not being forced using MFA for all users and at the same time being kind of "locked in" only having the option to toggle it on/off for all.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 29 2021 07:07 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 29 2021 07:35 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 29 2021 09:04 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 29 2021 12:13 PM
Since Microsoft Authenticator can work on WIFI for Push notification; and when there is no Internet, you can use OTP.
There is another mystery for me for Azure AD license. The document seems indicate if you don't have a P1 license, then the only option to allow MFA for none-admin user is to use "security defaults". But my test shows even without Premium license, I can still enable MFA per user bases. The only difference is the user without Premium license can only use Microsoft Authenticator for MFA, they can't use SMS/phone call options.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 29 2021 12:44 PM - edited Sep 29 2021 12:49 PM
That’s actually one way to go in this use case. You could turn off security defaults and use the legacy per-user MFA if there’s no way of upgrading to Business Premium. And check the Service settings tab for available methods.
https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-mfa-userstates
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 29 2021 12:49 PM
Before we just didn't enforce MFA until after we had their devices setup as we only needed a password, but now in Azure, there is a Registration policy that prompts the MFA on laptop.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 29 2022 12:33 AM
@luvsql So the discussion stops here ? Did you find your solutions? Did you un-select the password write back option within Azure. This also enforce the registration of a mobile number or installing the app.
For my knowlegde, if you have enable 1 p1 license within your tenent you have the option to do conditional access to enable modern MFA. This can also be a trial license. FIDO authentication works with the basis security license, so if you don't need conditional access it will work for al employees.
TAP works great with the OOBE, so if there is a new user and you grand him/her a TAP before the login the first time. The can login without registrating any MFA and than redirect this user to mysignins.microsoft.com/security-info to register there FIDO device.
If you have some bugs to spare you can always add a proper IAM profider. You will stil need the p1 license but than you can redirect the user to other provider (like Entrust) for a beter user experience when enrolling FIDO keys.
Last warning- Microsoft is telling, many years now, that you have to enable the p1 license to each user when you want to be compliant!
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 28 2021 01:05 PM - edited Oct 04 2021 05:19 AM
Solution@luvsql Hello again, I had to try it using security defaults as I'm pretty sure you're using that. You have no Intune, Conditional access or MFA registration policy in your subscriptions.
So, when simply using security defaults with enforced MFA you get the prompt to add security info/details, and can skip this for 14 days. When enabling the Temporary Access Pass policy and activating that for a newly created user in Azure AD it instead becomes the first prompt.
This is how it looks like and takes you to https://aka.ms/mysecurityinfo page where one can configure additional options, such as the security key. I could not proceed as I do not have a key to put in the laptop.
*My reply is being updated as you can actually use TAP to add a security key (as the pictures show) with security defaults. For the sake of it I even asked Microsoft who verified the method.
To wrap up the above.
1. Enable security defaults.
2. Enable TAP and assign to user.
3. User logs in using TAP and adds FIDO2 key.
4. Next sign-in when prompted for MFA user uses FIDO2 key (as FIDO2 satisfies MFA).