- Home
- Security, Compliance, and Identity
- Microsoft Entra
- Grant user consent for the delegated Graph API permissions without the UI flow
Grant user consent for the delegated Graph API permissions without the UI flow
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 03 2022 10:14 PM
There are two types of the Graph API permissions we can grant for an AD application.
1. Application permissions
2. User Delegated permissions
For the application permissions:
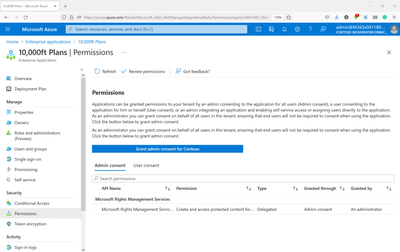
AAD portal provides UI to Grand the Admin consent:
For the user delegated permissions:
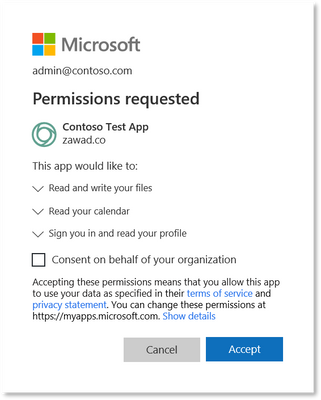
For the delegated permissions to provide the consent, user need to login to the application requires the access and using the UI flow grant the permissions.
This is possible for the application which has the web UI, but for the backend without any UI this is not possible.
Questions:
1. Can we avoid the UI flow for granting the consent for the user delegated permissions?
2. Is there a way we can grant consent for the user delegated permissions from the Azure AD portal like we do for the Admin consent?
3. If it is not supported from the AD portal, is there a Graph APIs to grant the permissions?
4. If it is supported by the Graph APIs links to the documentation/example will help.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 03 2022 11:44 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 04 2022 01:41 AM
Consent should never be fully-automatable in any case.
Compliance, as a key component of good governance, should be auditable and approvers should be accountable. Full automation of such a key concept would take us backwards 10+ years in the technology systems space, and from a commercial perspective, we'd be grilled by risk-aware business stakeholders, insurers, etc.
I'm wondering what the problem you're trying to solve is? Particularly in the context that someone with the appropriate formal authority from the customer tenant could be configured within Azure to be able to approve this - or any other - application for all of their users.
Grant tenant-wide admin consent to an application - Azure AD | Microsoft Docs
Cheers,
Lain
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 17 2024 12:58 AM - edited Jan 17 2024 01:45 AM
Hi @LainRobertson and @Vasil_Michev
I have too facing same issue while grant admin access. Let me explain clearly.
I am curious about the significance of admin consent and would like to understand how it can be granted programmatically for application permissions. Are there any examples illustrating the process, especially for permissions like "Audit Log Read All" through Microsoft Graph API?
I am not able to give grant admin access for my permissions as "Audit Log Read All" . Not able to give through api without login.
I tried Post man and Code also. end with fails.
POST MAN Issues : Bad Request or
please provide me any new features Microsoft support for give admin consent. Graph API Links or documentations