- Home
- Security, Compliance, and Identity
- Microsoft Entra
- Device registration and security/MFA registration
Device registration and security/MFA registration
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Mar 27 2020
01:02 PM
- last edited on
Jul 24 2020
01:16 AM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 27 2020
01:02 PM
- last edited on
Jul 24 2020
01:16 AM
by
TechCommunityAP
I would like to better understand how the AAD device registration works.
In AAD we see byods being registred in AAD when installing configuring Outlook or Teams. Is registration also triggered when configuring other applications (eg OneDrive, Word...)? Is this a setting we can configure?
Upon registration of their byod device, users are requested for additional security registration (mfa). Is this a setting we can configure?
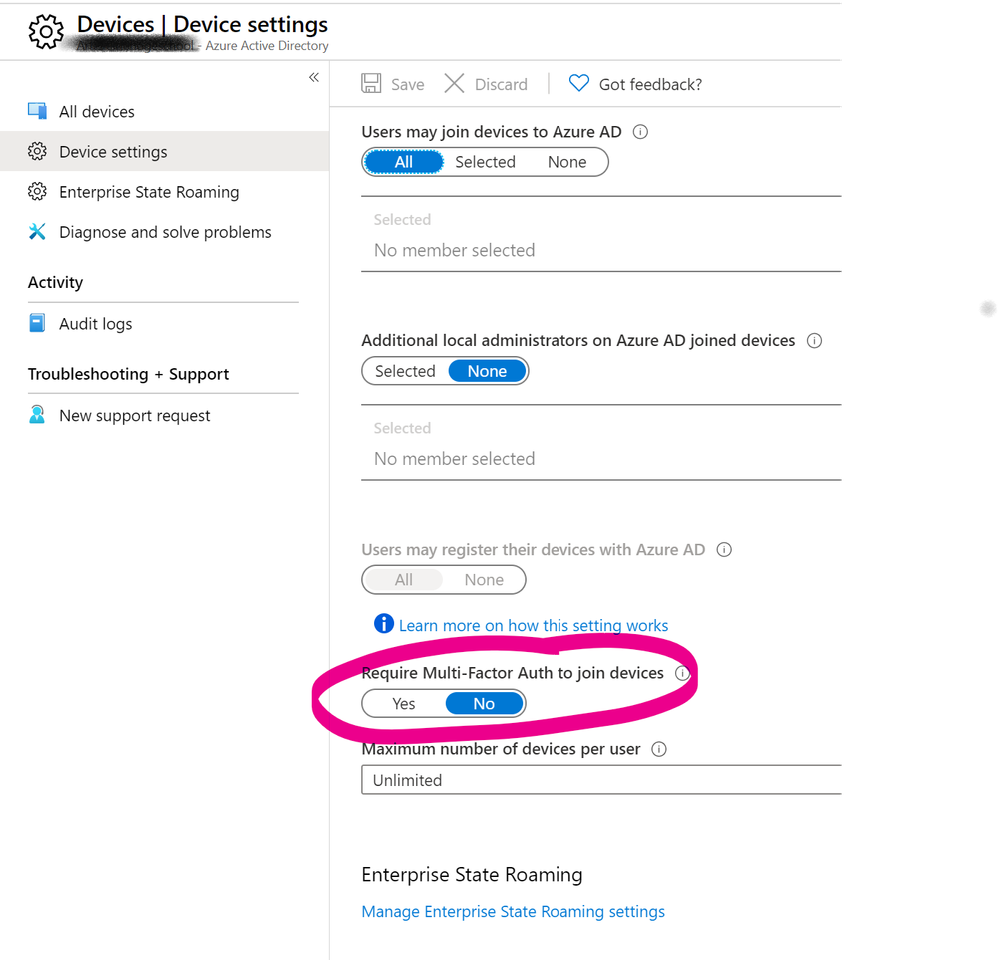
"Require Multi-Factor auth to join devices" in AAD is set to NO.
Thanks!
- Labels:
-
Identity Management
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 28 2020 08:15 PM
I think this particular setting cab controlled from different spots, like Identity Protection, Conditional Access or All tenant (you showed in your Screenshot).
Could you check in Intune Profile or Conditional Access?
Moe
https://docs.microsoft.com/en-us/azure/active-directory/identity-protection/howto-identity-protectio...
https://docs.microsoft.com/en-us/mem/intune/enrollment/multi-factor-authentication
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 29 2020 01:46 AM
I have not found any way to disable this behaviour of BYOD when using new versions of Office. The only way to skip Azure AD Registration is to let the user cancel the wizard of registration.
The only downside I see is that you get a bunch of ”unknown personal devices” in your Azure AD.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 30 2020 05:12 AM
Thank you for the suggestions, @Moe_Kinani and @Jonas Back
We have defined a few conditional access policies, but none of them requires mfa registration. There is only a limited group of users required to use mfa to log on, that's it.
No specific policies are defined in intune.
User based MFA is disabled for all our users.
MFA registration in Azure Identity protection is also disabled.
Maybe I should open a support ticket.
Bart
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 30 2020 06:29 AM
@bart vermeersch What does Azure AD Sign-in logs say? This might tell you why MFA is required.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 30 2020 11:04 AM
@Jonas Back not really, it's not mfa that is required, it's the mfa registration that is requested.
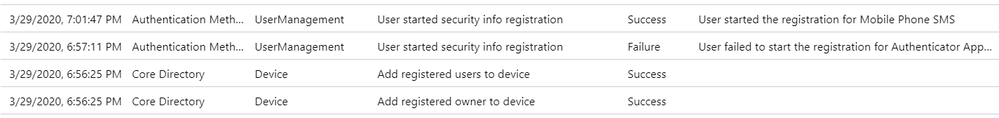
We always see a user registering his device (eg when configuring Teams or Outlook) followed by mfa registration:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 31 2020 12:42 AM
Unless the user OOBE joined their own device at the time of setup.
BYOD or connecting to Outlook or Teams on devices usually show up as Azure AD registered and not as Azure AD Joined. If MAM enrollment is enabled.
If you enabled MAM enrollment most of the time those policies are App protection policies for Windows 10 without enrollment.
Conditional Access can still be enforced for MFA on non domain joined devices.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 01 2020 09:12 AM
@bart vermeerschHave you ever sorted out what is causing this MFA registration request? We are seeing the same thing and this thread seems to be the only place I can find any mention of this behavior.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 01 2020 02:30 PM
Solution@bflick I think I do. The key thing is a user is not using his password to log in to his device (but using PIN, Windows Hello...) , to be able to perform SSO towards Azure services, this isn't sufficient, you need a password or some additional factor. This triggers device registration. It is the device registration that needs the mfa (not yet sure why exactly).
So to be tested, if you use password to log in to Windows 10 you will not start the device/mfa registration, but SSO will be possible. If you do not use a password to log in to Windows 10 and skip the device/mfa registration you won't get SSO for Teams and Outlook.
If the user logs into the machine via a new generation credential (PIN, Hello, ..) that is not already included in the existing PRT or there is no existing PRT on the device then the Azure AD MAM plugin will trigger device registration via a request which includes the “amr_values=ngcmfa” parameter and this will be the source of the MFA.
From MS support
- The user is connecting from an Azure AD registered device via a PRT which only contains the password claim for the registration authentication method used(Registration_amr). This means that the device was previously workplace joined to Azure AD without MFA being required as per your current configuration in which MFA is not required. This evaluation is done based on the device authentication request sent to Azure AD.
- The MFA requirement is enforced by the Azure AD WAM plugin(Microsoft Authentication broker) via the following request parameters “amr_values=ngcmfa”. This is occurring because the user signed into the machine using a new generation credential like a PIN or fingerprint. At this time, because the user signed into the Windows device via a different authentication method than the one included in the PRT(which was password), the authentication broker forces the user to configure MFA so that it can refresh the existing PRT record on the device with the new authentication method used.
Considering the above information, this behavior is by design and to be expected due to the PRT token refresh process and you can find it better detailed in the following articles:
How is a PRT renewed? - https://docs.microsoft.com/en-us/azure/active-directory/devices/concept-primary-refresh-token#how-is...
When does a PRT get an MFA claim? - https://docs.microsoft.com/en-us/azure/active-directory/devices/concept-primary-refresh-token#when-d...
Regards,
Bart
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 01 2020 02:30 PM
Solution@bflick I think I do. The key thing is a user is not using his password to log in to his device (but using PIN, Windows Hello...) , to be able to perform SSO towards Azure services, this isn't sufficient, you need a password or some additional factor. This triggers device registration. It is the device registration that needs the mfa (not yet sure why exactly).
So to be tested, if you use password to log in to Windows 10 you will not start the device/mfa registration, but SSO will be possible. If you do not use a password to log in to Windows 10 and skip the device/mfa registration you won't get SSO for Teams and Outlook.
If the user logs into the machine via a new generation credential (PIN, Hello, ..) that is not already included in the existing PRT or there is no existing PRT on the device then the Azure AD MAM plugin will trigger device registration via a request which includes the “amr_values=ngcmfa” parameter and this will be the source of the MFA.
From MS support
- The user is connecting from an Azure AD registered device via a PRT which only contains the password claim for the registration authentication method used(Registration_amr). This means that the device was previously workplace joined to Azure AD without MFA being required as per your current configuration in which MFA is not required. This evaluation is done based on the device authentication request sent to Azure AD.
- The MFA requirement is enforced by the Azure AD WAM plugin(Microsoft Authentication broker) via the following request parameters “amr_values=ngcmfa”. This is occurring because the user signed into the machine using a new generation credential like a PIN or fingerprint. At this time, because the user signed into the Windows device via a different authentication method than the one included in the PRT(which was password), the authentication broker forces the user to configure MFA so that it can refresh the existing PRT record on the device with the new authentication method used.
Considering the above information, this behavior is by design and to be expected due to the PRT token refresh process and you can find it better detailed in the following articles:
How is a PRT renewed? - https://docs.microsoft.com/en-us/azure/active-directory/devices/concept-primary-refresh-token#how-is...
When does a PRT get an MFA claim? - https://docs.microsoft.com/en-us/azure/active-directory/devices/concept-primary-refresh-token#when-d...
Regards,
Bart