Howdy folks,
I’m excited to announce that Azure AD authentication to Windows Virtual Machines (VMs) in Azure is now available in public preview—giving you the ability to manage and control who can access a VM.
Deployment of Windows VMs in Azure is becoming very common and a challenge everyone faces is securely managing the accounts and credentials used to login to these VMs. Typically, people create local administrator accounts to login to these VMs and it becomes difficult to manage these accounts as people join or leave teams.
To make things simple people often follow the risky practice of sharing admin account passwords among big groups of people. This makes it very hard to protect your production Windows VMs and collaborate with your team when using shared Windows VMs.
Now, organizations can utilize Azure AD authentication over a Remote Desk Protocol (RDP) for their Azure VMs running Windows Server 2019 Datacenter edition or Windows 10 1809 and later.
Using Azure AD to authenticate to VMs provides the ability to centrally control and enforce policies using tools like Azure Role-Based Access Control (RBAC) and Azure AD Conditional Access to allow you to control who can access a VM.
There are many benefits of using Azure AD authentication to login to Windows VMs in Azure, including:
- Utilizing the same federated or managed Azure AD credentials you normally use.
- No longer having to manage local administrator accounts.
- Using Azure RBAC to grant the appropriate access to VMs based on need and remove it when it is no longer needed.
- Requiring AD Conditional Access to enforce additional requirements such as:
- Multi-factor authentication (MFA)
- Sign-in risk
- Automating and scaling Azure AD join for Azure based Windows VMs.
You can use Azure Portal, AZ CLI, or PSH to enable this capability. Below is a quick example of how to do this from Azure Portal.
Using Azure Portal create VM experience to enable Azure AD login
You can enable Azure AD login for Windows Server 2019 Datacenter or Windows 10 1809 and later VM images.
To create a Windows Server 2019 Datacenter VM in Azure with Azure AD login:
- Sign in to the Azure portal, with an account that has access to create VMs, and select + Create a resource.
- In Search the Marketplace search bar, type Windows Server.
- Click Windows Server and from Select a software plan drop-down, select Windows Server 2019 Datacenter.
- Click Create.
- On the Management tab, under the Azure Active Directory, toggle Login with AAD credentials (Preview) to On.
- Make sure System assigned managed identity under the Identity section is set to On. This action should happen automatically once you enable Login with Azure AD credentials.
Go through the rest of the experience of creating a VM. During this preview, you’ll have to create an administrator username and password for the VM.

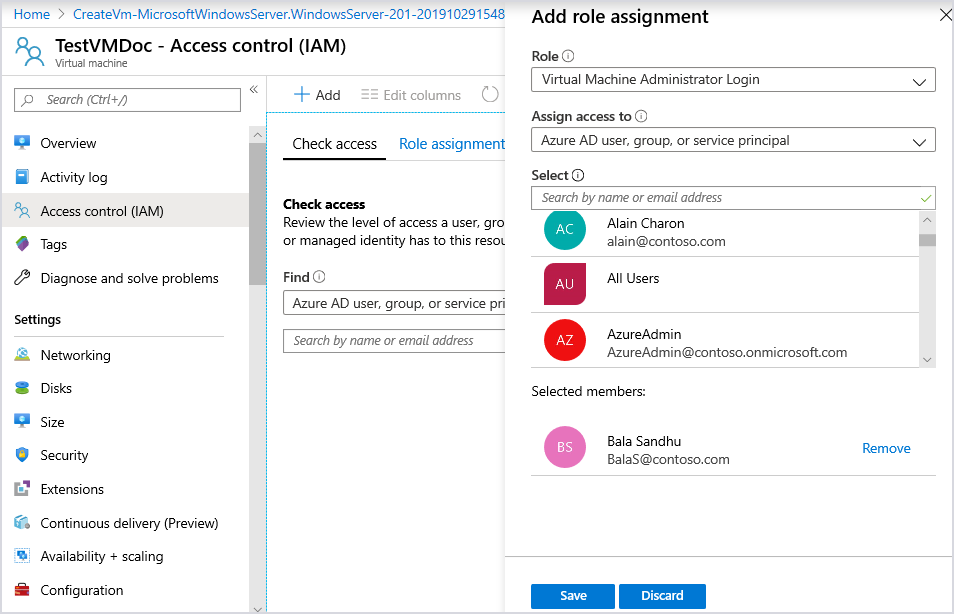
Using Azure AD portal experience to configure role assignment for the VM
To use your Azure AD credentials for Windows VMs in Azure, you must belong to Virtual Machine Administrator Login or Virtual Machine User Login role.
To configure role assignments for your Azure AD enabled Windows Server 2019 Datacenter or Windows 10 1809 and later VM images:
- Navigate to the specific Virtual Machine overview page.
- Select Access control (IAM) from the menu options
- Select Add, Add role assignment to open the Add role assignment pane.
- In the Role drop-down list, select a role such as Virtual Machine Administrator Login or Virtual Machine User Login.
- In the Select field, select a user, group, service principal, or managed identity. If you don't see the security principal in the list, you can type in the Select box to search the directory for display names, email addresses, and object identifiers.
- To assign the role, select Save.
After a few moments, the security principal is assigned the role at the selected scope.
You can check out our documentation to learn more about this feature and its prerequisites. Please let us know what you think in the comments below. We look forward to hearing from you!
Best regards,
Alex Simons (@Alex_A_Simons )
Corporate VP of Program Management
Microsoft Identity Division