- Home
- Azure
- Apps on Azure
- Access to Web App behind a private endpoint
Access to Web App behind a private endpoint
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jan 28 2021 05:15 AM
Hello everyone,
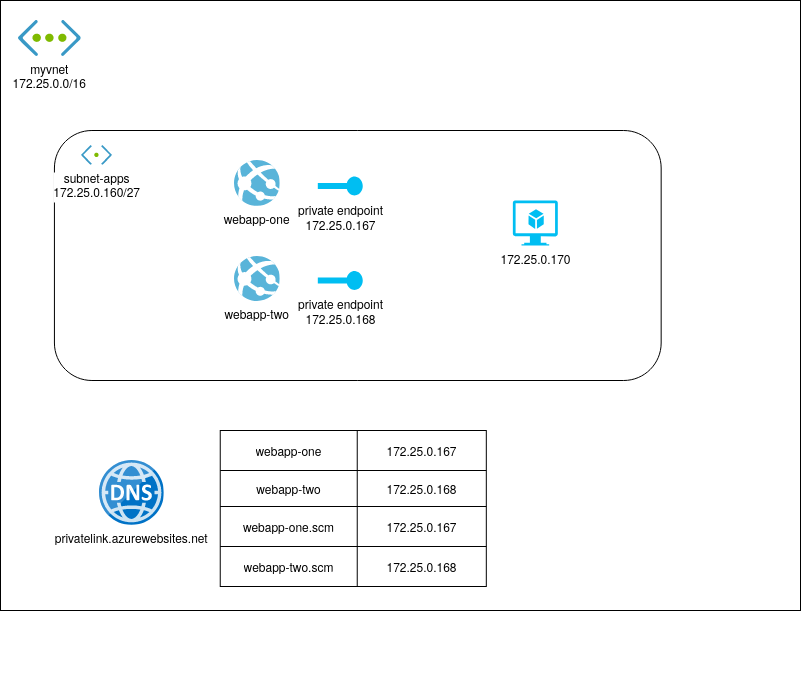
I deployed two web apps and a virtual machine and configured the resources to use the same virtual network (myvnet). The (Windows) web apps have private endpoint connections configured with names in a private DNS zone "privatelink.azurewebsites.net".
I can properly access the web apps from the virtual machine: The names [webapp-one / webapp-two].azurewebsites.net are resolved to the internal ip addresses of the private endpoints as the vm uses the nameserver 168.63.129.16.
But the web apps cannot access each other. In the code I try a HTTP Get request from the webapp-one application to "https://webapp-two.azurewebsites.net". This does not work and as far as I debugged this problem it seems that the name resolution is working properly. Instead of the internal ip address I get the external address (13.69.xx.yy).
Does anyone have an idea where to look?
Thanks in advance,
Matthias
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 10 2021 05:17 AM
Azure DNS Private Zones
After your app integrates with your VNet, it uses the same DNS server that your VNet is configured with. By default, your app won't work with Azure DNS Private Zones. To work with Azure DNS Private Zones, you need to add the following app settings:
- WEBSITE_DNS_SERVER with value 168.63.129.16
- WEBSITE_VNET_ROUTE_ALL with value 1
These settings will send all of your outbound calls from your app into your VNet in addition to enabling your app to use Azure DNS private zones. These settings will send all the outbound calls from your app into your VNet. Additionally, it will enable the app to use Azure DNS by querying the Private DNS Zone at the worker level. This functionality is to be used when a running app is accessing a Private DNS Zone.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 11 2021 11:05 AM
Hi
You are getting (13.69.xx.yy) because you are not reaching the private endpoint
To be able to reach the private endpoint you will need to integrater your app to the virtual network
https://docs.microsoft.com/en-us/azure//app-service/web-sites-integrate-with-vnet
In the link above you will see this :
After your app integrates with your VNet, it uses the same DNS server that your VNet is configured with. By default, your app won't work with Azure DNS Private Zones. To work with Azure DNS Private Zones, you need to add the following app settings:
- WEBSITE_DNS_SERVER with value 168.63.129.16
- WEBSITE_VNET_ROUTE_ALL with value 1
If you want to make calls to Private Endpoints, then you need to ensure that your DNS lookups will resolve to the private endpoint. To ensure that the DNS lookups from your app will point to your private endpoints you can:
- integrate with Azure DNS Private Zones. If your VNet doesn't have a custom DNS server, this will be automatic
- manage the private endpoint in the DNS server used by your app. To do this you need to know the private endpoint address and then point the endpoint you are trying to reach to that address with an A record.
- configure your own DNS server to forward to Azure DNS private zones