- Home
- Windows
- Windows security
- Hardening Windows 10 on an IT Pro's laptop
Hardening Windows 10 on an IT Pro's laptop
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 08 2018 10:28 AM - edited Apr 09 2018 01:50 AM
Hi
I have just bought a new Windows 10 Pro laptop for work as a freelance IT Consultant and I figured this would be good time adopt some of the latest best practices, pertinent to securing my machine. Given, this machine is also for personal use, so I am looking to balance convenience against security and privacy in the event of loss or theft.
I have found some extensive posts on the subject including the one shown below:
I would however, like to hear any comments anyone has: from bitlocker and beyond....
- Labels:
-
security best practices
-
Window 10
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 13 2018 04:13 PM - edited Apr 16 2018 10:59 AM
Solutiona clean install of Windows 10 is pretty good, that said, I do have the following advice:
- It is important to properly configure User Account Control on all machines; out of the box it is very insecure meaning anything can bypass it to grab admin privileges.
- It is important to make sure that Secure Boot is enabled on all machines.
- BitLocker is an obvious one, enable it on all machines.
- You may want to use Windows Defender Firewall to block all inbound connections on the private and public profiles, its very effective for protecting devices in public places and usually has no negative impact but should be assessed per requirements.
- You should deploy the uBlock Origin browser extension to all browsers, it blocks a significant amount of malware and greatly reduces the bandwidth used by your org; for the record, Chrome and Edge are much more secure than other browsers.
- Also remember to properly patch, if Windows, Defender, or Browser are out of date then you WILL be targeted.
Following the above will significantly benefit you and your users and can be done by anybody without any extra cost; I hope that's useful for you
Edit: oh, and if you're ever able to: I recommend you look into Windows 10 S (soon to be called Windows Pro in S Mode)
yes, it gets a lot of stick for restricting you to Edge and Store apps but that thing is rock solid; even if you never ever use it, it's the best example of Device Guard Code Integrity in action and how powerful it can be when properly configured
Edit: from 1803 Hypervisor enforced Code Integrity (HVCI) will be enabled by default via clean install, you can enable it on previous versions by following these instructions: https://docs.microsoft.com/en-gb/windows/security/threat-protection/enable-virtualization-based-prot...
HVCI is a feature that helps defend against kernel level malware; I initially didn't mention it because I'm not sure what the real world benefits are and I'm aware that it can cause instability and performance problems, however since Microsoft seems to be pushing for its implementation I felt it was worth adding. (I imagine they may also do the same for DMA Protection in the future)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 16 2018 07:13 AM
Hi
Thanks very much for your feed back - you are very well informed. You have also stuck the balance I was looking for, between security and convenience.
I have just got my laptop from the supplier so other than Office 2016 via The Office 365 Portal it is a clean build. I have a list of tools, utilities, PowerShell modules I want to install but I will hold off until the machine is hardened.
I will look at the Windows Defender Firewall and see how it compares with the Firewall that comes with my current AV ( who were recently in the news for the wrong reasons ;) ).
Bitlocker - think I won't bother with my boot up (C:) just my data drive so my code (repos) , OneDrives etc unless you think I should do all drives (note will need to verify TPM status with PowerShell beforehand)
I also thought of some anti-theft protection such as Prey Project
In addition, picking a decent VPN when I am working away, such as Express VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 16 2018 08:17 AM - edited Apr 16 2018 08:31 AM
nearly all AV firewalls layer on top of the windows filtering engine anyway, it usually doesn't make a difference which you use, I suggest that you use which ever you find most convenient to manage
I highly recommend BitLocker on all drives, Windows will not only accumulate a significant amount of data over time that can be used to identify and break into your devices/drives/accounts, but it also caches file data locally, even if it is stored on encrypted drives; to be absolutely clear: data stored on any drive will leak onto the C: drive
Also, before you enable BitLocker I recommend that you configure the "Require additional authentication at startup" local group policy setting first:
- set the policy to "Enabled"
- if your device doesn't have a TPM, tick the "Allow BitLocker without a compatible TPM" checkbox; this enables you to set up BitLocker with a password, preventing the "missing TPM" error
- if your device has a TPM, set the second drop down box to "Require startup PIN with TPM" and set the other three to "Do not allow"; this enables you to set up Bitlocker with a PIN, preventing the insecure "automatic unlock" aka "TPM only" configuration
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 16 2018 09:04 AM
Ok, You have convinced me: BItLocker universal it will be. I will report back once I have set the startup policy and enabled it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 16 2018 11:20 AM
I'm glad to help
IT security is more important than ever but it should never stop you from doing your job
I'm also glad that you openly asked for outside knowledge/experience, very professional
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 24 2018 01:50 PM - edited Apr 24 2018 01:55 PM
Hi
On my laptop which does have TPM 2.0 : does this look ok?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 25 2018 10:48 AM - edited May 03 2018 07:56 AM
yep! that's exactly correct
now when enabling BitLocker this policy will force you to set a TPM based pin; that pin will have the brute-forcing protections of the TPM, which is the best possible protection for your data if the device is ever stolen
you only need to set up this pin for the OS drive though, after that your data drives can be set up as auto unlock drives (they're unlocked when the OS drive is unlocked and are essentially linked, they are secure)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 25 2018 12:36 PM
Hi
Thanks very much. I did google but all I could find is the non-tpm configuration. Anyway, I gather the "Hello" Pin doesn't have be long: https://docs.microsoft.com/en-us/windows/security/identity-protection/hello-for-business/hello-why-p...
Good news on the auto unlock on the data drives. Ok I will go forth and Bitlock my world!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 25 2018 04:29 PM - edited Apr 25 2018 04:41 PM
yep, I would say that 6 digits is "the standard"
4 digit pins are "gently discouraged" but not uncommon
TPM/hello pins literally exist to give you the benefits of a good complex password but without the inconvenience
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 26 2018 07:39 AM
If you want to go for more than just "kind of secure, unless it's inconvenient" consider leveraging Client Hyper-V to use a hypervisor boundary to protect your sensitive config from your productivity / riskier usage.
We talk about Privileged Access Workstations here: http://aka.ms/cyberpaw - Jian Yan has been working on this model and talk about an updated architecture here: https://blogs.technet.microsoft.com/datacentersecurity/2017/10/13/privileged-access-workstationpaw/
We also document our security baselines here: https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-security-baselines
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 26 2018 12:33 PM
Yep, I think that' son @Deleted security todo list which I am slowly going through , starting with Bitlocker. One thing I did was turn was allowing complex passwords prior to enabling Bitlocker. Oddly I didn't get much feedback regarding Drive C whereas Drive D I got the full progress dialog. Seems to be working well and will test hibernation recovery at some stage.
As for your suggestion, Are there any downsides to this as I want to work seamlessly with PowerShell, Azure, REST calls etc
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 26 2018 02:55 PM
When encrypting the C drive it'll ask you to reboot, and the process will start after you next log in. Other drives will start encrypting immediately, that might explain the missing progress dialog.
Chris' suggestion is not something I've mentioned. I've had successful implementation of that sort of model as the level of role, domain, or infrastructure segregation, but as a single user on a single machine it would essentially mean trying to keep all your more "dodgy stuff" to one VM whilst your "sensitive stuff" is in other VMs, potentially a VM for each contract/client/environment. I feel like the concept is aspirational but in reality creates a lot of management overhead, interrupts workflow, and leads to a false sense of security.
That said, I'm glad to see your input Chris and ultimately I may be misunderstanding; I'd love to learn more
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 26 2018 03:21 PM
We'd certainly like to hope that PAWs are not just aspirational - it's a key aspect of our Securing Privileged Access Roadmap: https://docs.microsoft.com/en-us/windows-server/identity/securing-privileged-access/securing-privile...
We've got them deployed for tens of thousands of our own internal users at Microsoft who have privilege in our dev-ops workflows, as well as at hundreds of customers.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 27 2018 12:00 AM
That's really impressive
This is unrelated, but are there any plans to move Windows 10 S to this kind of model by default?
I use Windows 10 S as the host on all my personal machines, and there are non-store programs that I run in Windows 10 Pro guest VMs.
The current advice plastered all over S though is that users take the free upgrade to Pro so they can run non-store programs; wouldn't it be more beneficial to provide users with a lightweight VM to run such "untrusted" software? Potentially similar to how Windows Defender Application Guard functions as a container for Edge?
May 03 2018 07:54 AM - edited May 03 2018 07:55 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 03 2018 07:54 AM - edited May 03 2018 07:55 AM
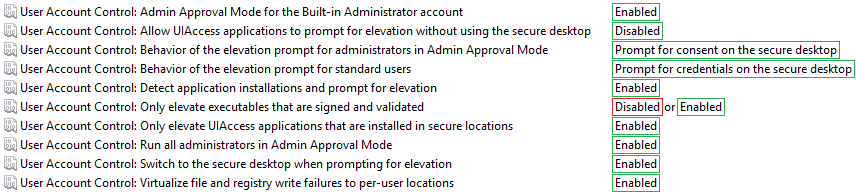
For reference, here is how User Account Control should be configured if using Local Security Policy
Be aware that if you need to elevate unsigned executables you will have set "Only elevate executables that are signed and validated" to "Disabled", otherwise you will receive the "A referral was returned from the server." error when trying to run unsigned executables
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 28 2018 06:48 PM
Hardening of your machine should rely on the Least Privilege principle. Use a non admin account for daily use. Disabling un-used programs, services and firewall rules. Minimizing your attack surface and turning off un-used network facing Windows features.
While I applaud MS for improving protection on kernel things, attackers do not have to necessarily touch the kernel to do damage. I have seen damages to Windows Defender and Windows Edge, just as an example. And their improvements rest on having new hardware, which leaves countless older platforms unprotected. Also their new innovations also relies on Windows Server Active Directory, which no home user has.
And sometimes, even when MS has been notified of working exploits, they fail to make changes to their code. Like Google Project Zero's findings on exploitable WPAD ( Auto Proxy Detection ) and javascript bugs.
These MS techs only know to expound on their latest innovations. They are not incident responders. And they do not know how to harden Windows.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 28 2018 10:22 PM
However, I do agree that BitLocker is the way to go since the thread starter's main concern is theft or lost laptop.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 19 2019 11:32 AM
https://techcommunity.microsoft.com/t5/Windows-10-security/Hardening-Windows-10/m-p/475686
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 05 2019 09:05 AM
in Windows Defender: Memory Integrity and Core Isolation
in Windows settings: DEP for ALL programs instead of only for Windows services.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 13 2018 04:13 PM - edited Apr 16 2018 10:59 AM
Solutiona clean install of Windows 10 is pretty good, that said, I do have the following advice:
- It is important to properly configure User Account Control on all machines; out of the box it is very insecure meaning anything can bypass it to grab admin privileges.
- It is important to make sure that Secure Boot is enabled on all machines.
- BitLocker is an obvious one, enable it on all machines.
- You may want to use Windows Defender Firewall to block all inbound connections on the private and public profiles, its very effective for protecting devices in public places and usually has no negative impact but should be assessed per requirements.
- You should deploy the uBlock Origin browser extension to all browsers, it blocks a significant amount of malware and greatly reduces the bandwidth used by your org; for the record, Chrome and Edge are much more secure than other browsers.
- Also remember to properly patch, if Windows, Defender, or Browser are out of date then you WILL be targeted.
Following the above will significantly benefit you and your users and can be done by anybody without any extra cost; I hope that's useful for you
Edit: oh, and if you're ever able to: I recommend you look into Windows 10 S (soon to be called Windows Pro in S Mode)
yes, it gets a lot of stick for restricting you to Edge and Store apps but that thing is rock solid; even if you never ever use it, it's the best example of Device Guard Code Integrity in action and how powerful it can be when properly configured
Edit: from 1803 Hypervisor enforced Code Integrity (HVCI) will be enabled by default via clean install, you can enable it on previous versions by following these instructions: https://docs.microsoft.com/en-gb/windows/security/threat-protection/enable-virtualization-based-prot...
HVCI is a feature that helps defend against kernel level malware; I initially didn't mention it because I'm not sure what the real world benefits are and I'm aware that it can cause instability and performance problems, however since Microsoft seems to be pushing for its implementation I felt it was worth adding. (I imagine they may also do the same for DMA Protection in the future)