- Home
- Security, Compliance, and Identity
- Security, Compliance, and Identity
- How Azure Security Center aids in detecting good applications being used maliciously
How Azure Security Center aids in detecting good applications being used maliciously
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Aug 15 2017
01:50 PM
- last edited on
May 24 2021
02:32 PM
by
TechCommunityAP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 15 2017
01:50 PM
- last edited on
May 24 2021
02:32 PM
by
TechCommunityAP
We’ve written in the past about how Azure Security Center helps detect malicious activity on compromised VMs, including a post detailing a Bitcoin mining attack and one on an outbound DDoS attack. In many cases, attackers use a set of malicious tools to carry out these and other actions on a compromised machine. However, our team of security researchers have identified a new trend where attackers are using good application to carry out malicious actions. This blog will discuss the use of known hacker tools and those tools that are not nefarious in nature, but are being used maliciously, and how Azure Security Center aids in detecting their use.
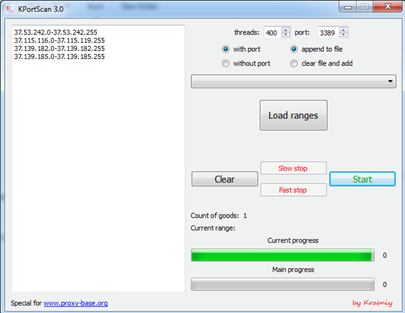
Generally, the first category of tools we see after a brute force attack are the Port and IP address scanning tools. Most of these tools were not written maliciously, but because of their ease of use, an attacker can scan IP ranges and ports to find vulnerable machines that they can target.
Read more about it in the Azure blog.
- Labels:
-
Security and Compliance Center