- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Re: Require MFA for Intune device enrollments
Require MFA for Intune device enrollments
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 19 2019 11:32 PM
Hi,
belonging to the following MS docs i'm wondering why some of my users need to provide MFA while enrolling their device, even if i have not set up the conditional access as descibed in the MS Docs, yet.
https://docs.microsoft.com/en-us/intune/multi-factor-authentication
Thank you in advance.
Regards
Patrick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 20 2019 12:21 AM
Hi @PatrickF11,
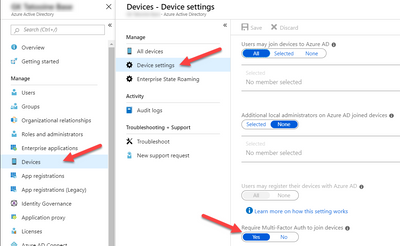
some of them could mean only Windows 10? Then it might be the case that you are enforcing MFA on AADJ like this:
best,
Oliver
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 20 2019 12:45 AM
sorry, i meant iOS & Android Enrollment.
(By the way: The mentioned setting is active in my tenant config.)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 20 2019 12:59 AM
:) ah okay. Android and iOS should not be affected from this setting. Did you have several CA policies active in your tenant? Did you try to use the CA "What if" feature to check if you might be affected under certain conditions which then might include the "Microsoft Intune Enrollment" app as mentioned in the article?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 21 2019 12:42 AM
At this moment there are only 2 CAs active:
One is for administrators and one is for ActiveSync (Blocking of the native ios&android app, to gently "push" the use of the Outlook App. ;)
So at this moment i don't have any idea. :\
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 21 2019 12:46 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 21 2019 12:49 AM
Hi @hskovgaard,
i know that some users use MFA, but they don't appear in this list from your link.
What should account.activedirectory.windowsazure.com effect? When i look into this no user has MFA enabled, even if i know some registered for MFA.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 21 2019 12:54 AM
Another thing to check is to see if there is anything setup in Azure AD Identity Protection regarding MFA?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 21 2019 01:17 AM
@hskovgaard Thank for your explanation.
In Identity Protection i've set up the Sign-in risk policy to require MFA when risk level is high. (We want to "tighten" that to medium risk level.)
At this point we do not enforce our users to register for MFA. (Azure AD Identity Protection -> Configure -> MFA registration)