- Home
- Microsoft Intune and Configuration Manager
- Microsoft Intune
- Re: Intune Compliance Policy: Device not compliant because of missing machine risk score: deactivate
Intune Compliance Policy: Device not compliant because of missing machine risk score: deactivated?
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Feb 28 2019 06:40 AM
Dear all,
I have this curious compliance issue for which I cannot find any information online or on docs.microsoft.com. Any help or suggestions are appreciated.
We are testing Windows Defender ATP in combination with Intune compliance policies on a limited amount of devices. We had a first test group of three devices, and a second test group of four devices. So 7 in total.
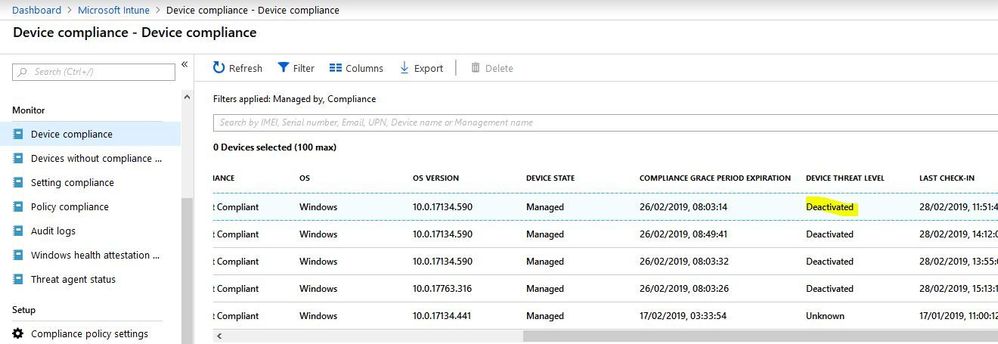
In Intune our 'second wave' of test devices is somehow marked as "non compliant" because a violation of our rule that "Require the device to be at or under the machine risk score = clean, low,...". However, these machines are onboarded in Windows Defender ATP and are showing to have no issues. In Intune the table in Device Compliance -> Device Compliance shows that for these machines the Device Threat Level is "Deactivated". (Our other test machines report "Secured", machines outside the test group are reporting "Unknown".)
I cannot find any documentation where this state of "deactivated" is discussed.
We identified three other differences between or first test group and the second test group:
- License level was on Microsoft E3 for the non-compliant machines, instead of E5
- Windows version was 1803 for the non-compliant machines, instead of 1809
- The very first test group was onboarded in Windows Defender ATP using a script. The second non-comliant group was onboarded using a configuration policy in Intune.
To test if any of these three differences could have caused the issue I did three separate tests:
1) I moved one user to Microsoft E5, as I understand for Windows Defender ATP this is required.
2) I had one other machine upgraded to Windows 10 1809
3) I ran the manual onboarding script once more on a third machine
But none of these machines would be compliant afterwards.
I onboarded the first test group to ATP using a script downloaded from ATP. They were active for a few weeks with just the ATP link. I then assigned both the compliance policy and the final ATP configuration at the same time to this first group.
The second group was onboarded by the ATP configuration policy in Intune. I assigned the identical compliance policy a day later.
I assume that the compliance check fails because the machines do not communicate their threat level (shown as "deactivated" in the Intune portal) properly.
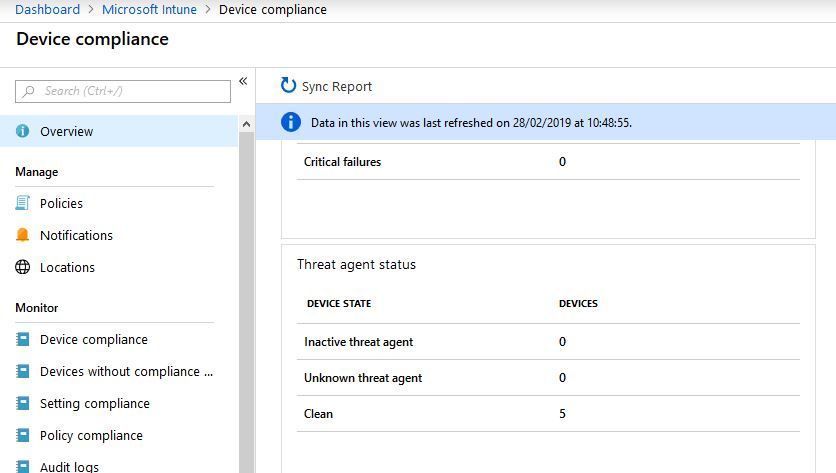
One widget in the device compliance screen does show 5 of the 7 devices to be clean:
I do not understand why it counts 5 devices. What with the remaining two? And if these 5 are indeed clean, why do at least two of them (7 minus 5) report as having a threat level "deactivated" and "non-compliant"?
Does anyone know why the Device Threat Level of the second test group is "deactivated"? What causes this? How can I solve this?
Thanks for your help!
Best regards,
Wim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 06 2019 01:40 PM
I am having a very similar issue. On my Device compliance policy I am showing "Require the device to be at or under the machine risk score" as not compliant. The device appears to be onboarded but is now showing up in the Windows Defender Security Center Portal. Only machines I have onboarded manually with a script appear there. I have gone through the Intune - WDATP onboarding instructions located here https://docs.microsoft.com/en-us/intune/advanced-threat-protection several times and everything seems to be set correctly. If I look on the device WDATP shows that there are no threats and no action needed. Why is the device not showing up in the console and why am I getting the compliance issue?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mar 12 2019 05:41 AM
Thanks for the comment.
After the initial post in this thread I did not make any more changes due to business travel. After about a week suddenly the machines became compliant. Again: with no changes. Could it be that some process needs to run in the course of about a week before a client really is marked as compliant?
Are you seeing this too?
Best regards,
Wim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 23 2019 03:08 PM
Still having issues getting devices to join to WDATP through the Intune process. I have switched to a hybrid deployment because of some of the limitations of transferring all of our GPO settings to Intune. I can join devices using the script. I do not really trust Intune at this point to not mark one of my devices not compliant and cut off the VP while he is out of the office. Not a great feeling. We are going to do more testing with a rollout to IT staff.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 24 2019 01:31 AM
@RyanReynoldsThanks for the feedback. That is indeed not a comfortable situation to be in. I just checked our device list and they are still marked as compliant, with the exception of one device for another reason.
In any case, the behaviour seems flaky to it would be great if this could be addressed by the Intune team.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 27 2019 10:38 PM
I am having the same issue, I have tested this on 6 Win10 computers at this point, it seems that if I Azure AD Domain Join the computers everything works fine, if I Azure AD Register and MDM Manage the device, it will show up as clear or level 1 in WATP poral and as Deactivated in Intune portal.
I've read conflicting information in the documentation, is Azure AD Domain Join mandatory? Seems ridiculous if it is, I mean the Mac client was releases and how are you supposed to deal with BYOD if this is the case? I am working a support case with Microsoft and they are adamant about the fact that MDM Managed devices should report correctly but we have been working the case for 15 days so far and no changes. The strange thing is I can configure ASR, cloud protection, and set any of the other policies with no trouble. This makes it seem it may just not currently work unless the system is Domain Joined and MDM Managed and not Domain Registered and MDM Managed.
If anyone has any details at all, would love to hear them. We have several deals closed with clients to deploy M365 E5 and I want to prepare them if Intune isn't going to show their security status in Intune as this is going to effectively kill our ability to use Conditional Access to limit access based on risk.
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 14 2019 07:34 AM
When looking at the device status of the compliance policy most devices are shown twice. Once with the user 'system account' and once with the regular user of the machine. In the end it does not seem to affect the compliance status of the device itself but it is annoying and makes it very hard to find that one device that is in fact not compliant.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 14 2019 12:50 PM
Mine never went compliant, no idea what the heck, everything else works but not that and I can't get support from Defender ATP team to save my life even with a support contract. Intune guys took me through a million steps and were great but even they say it is a DATP issue so I am just sort of stuck. Overally clearly some major issues with the integration still. @Wim Borgers
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 30 2019 04:50 AM
Hi,
any Updates on this case?
I´ve got a customer with same problems. Device ist not compliant because of: Require the device to be at or under the machine risk score:
Test with different settings (not configured till High) won´t fix this.
Securitycenter shows all devices with no problems.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 31 2019 11:50 PM
@Markus Dinkel, Same issue here, MS ticket has been open for a few weeks, no clear response.
I've tested by joining a device in Azure AD instead of a hybrid join and then the device reports compliant but as stated in previous messages, Azure AD join shouldn't be a requirement.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 03 2019 02:02 AM
@Jerod PowellWe are having the same issue with one of our customers, I have had 4 different Intune teams trying to solve it but it looks to be a bug in Defender ATP portal not showing up a threat for the device which causes this issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 03 2019 01:38 PM
@MyronHelgering I believe the issue typically ends up being the licensed version of Windows 10, we were running Windows Insider builds and for whatever reason they weren't being registered as Windows 10 Enterprise E5, this is what was causing the issue. That said there was no workaround but to load Windows 10 Enterprise E5 without insider builds. This resolved our issue, not an ideal situation though, all sorts of issues we have found with E3 vs. E5 vs. Pro, etc., with Windows 10.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 04 2019 05:07 AM
@Jerod PowellUhmm this doesn't seem to be related to our problems with the Defender ATP policy. None of the devices run insider builds.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 16 2019 08:33 AM
@Jerod Powell, do you have an easy way of checking whether or not a machine is properly recognizing the licensing as Windows 10 Enterprise E5? About 80% of our machines are showing this "Deactivated" status and although I'm fairly confident that it's not an OS license issue for us, I'd like to know if there's a simple way to rule it out for sure.
I do have a support case open with Microsoft, but it's moving very slowly as those things do. They always seem to call with about 5 min to go in the workday. I've begun to accept that this is actually done with intent on their end.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 16 2019 12:25 PM - edited Oct 16 2019 06:55 PM
This posting is provided "AS IS" with no warranties, and confers no rights.
Configure Conditional Access in Microsoft Defender ATP
https://docs.microsoft.com/en-us/windows/security/threat-protection/microsoft-defender-atp/configure...
The way that you join to Azure AD matters for Intune + Conditional Access + Device Compliance + Device Risk to work. Take a look here:
https://microscott.azurewebsites.net/wp-content/uploads/2018/08/enrollmenttypes_Capabilities5.png
At least methods 5, 6, 10 and 11 of joining "Azure AD Join" will work with it.
Managing Windows 10 with Intune – The Many Ways to Enrol
https://microscott.azurewebsites.net/2018/08/31/managing-windows-10-with-intune-the-many-ways-to-enr...
Action Center -> All settings -> Accounts -> Access work or school -> "Connect"
Yes
Device preparation
Device setup
Account setup
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 16 2019 12:50 PM
Licensing requirements
Microsoft Defender Advanced Threat Protection requires one of the following Microsoft Volume Licensing offers:
Windows 10 Enterprise E5
Windows 10 Education E5
Microsoft 365 E5 (M365 E5) which includes Windows 10 Enterprise E5
Microsoft 365 E3 (M365 E3) with Identity and Threat Protection package
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 16 2019 12:53 PM
It's important to note that Azure AD registered devices is not supported in this scenario.
Only Intune enrolled devices are supported.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 16 2019 12:56 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 16 2019 01:01 PM
@Jerod Powell Mine is somewhat ambiguous and simply states "Windows 10 Enterprise". Similarly, under Settings - Update & Security - Activation it states "Windows 10 Enterprise" and "Windows is activated with a digital license". I assume it's the assigned E5 license, but I don't know for certain.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 16 2019 01:06 PM
@Philip Kluss To check if you have Windows 10 E5 (or A5 for EDU's), or MTP E5, are you able to login to SecurityCenter.Microsoft.com and see your Windows 10 1607 or newer enrolled there?