- Home
- Security, Compliance, and Identity
- Microsoft Defender for Endpoint
- Re: Pushing custom Indicator of Compromise (IoCs) to Microsoft Defender ATP
Pushing custom Indicator of Compromise (IoCs) to Microsoft Defender ATP
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 05 2019 06:24 AM - edited May 05 2019 06:27 AM
Submit your own IOCs to Microsoft Defender ATP to create alerts and perform remediation actions.


Many organizations maintain internal lists of attack indicators such as file data, IP address, or URL.
These lists can be derived from an analysis of previous attacks on the company, external intelligence services, or the publication of data on attacks on information sharing tools on the Internet.
In this tutorial, you’ll see how these lists can be used to:
- Generate Microsoft Defender ATP alerts
- Block the execution/usage of items in the list
Let’s start
- Step 1: Add the required permission to write indicators to Microsoft Defender ATP
- Step 2: Enable advanced features in Microsoft Defender ATP
- Step 3: Run tests
Step 1: Add permission to write indicators to MDATP
If you haven’t created an app:
- Create an app using the instructions described in the Hello world blog.
- Then follow the instructions on how to Add Isolation Permission as described below.
If you’ve already created an app that you’re going to reuse for this demonstration:
- Add the “TI.ReadWrite.All” permission as described below.
- We recommend that you follow the detailed steps as described in the “Step 1 - Add the required permission to the application” in the Alert Update API blog .
Add TI writing Permission
- Open Azure portal.
- Navigate to Azure Active Directory > App registrations.
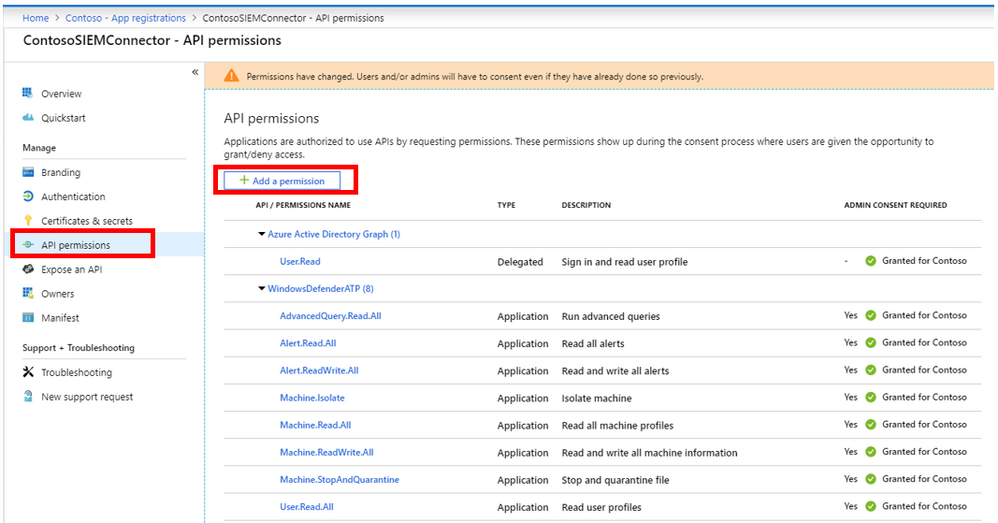
- Under All Applications, find and select the application, for example, ContosoSIEMConnector.
- Click API permissions > Add a permission.
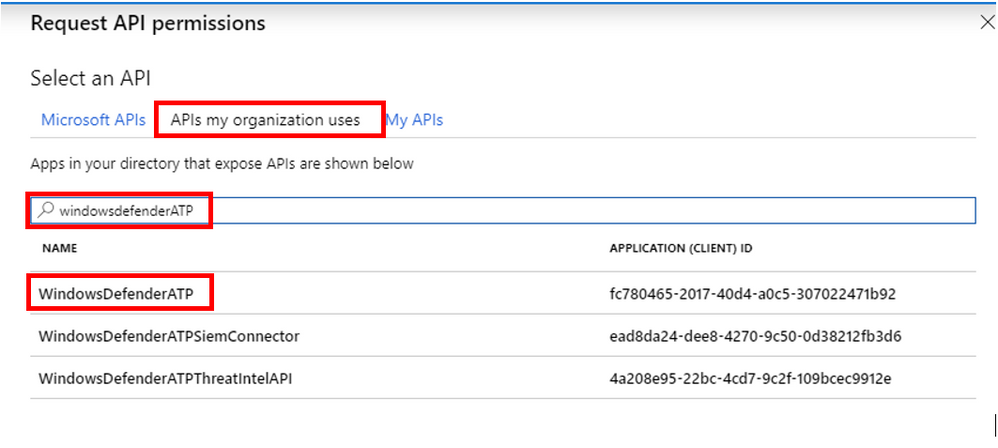
- Click on “APIs my organization uses” and type WindowDefenderATP in the search box. Then chose the “WindowsDefenderATP” API from the list.
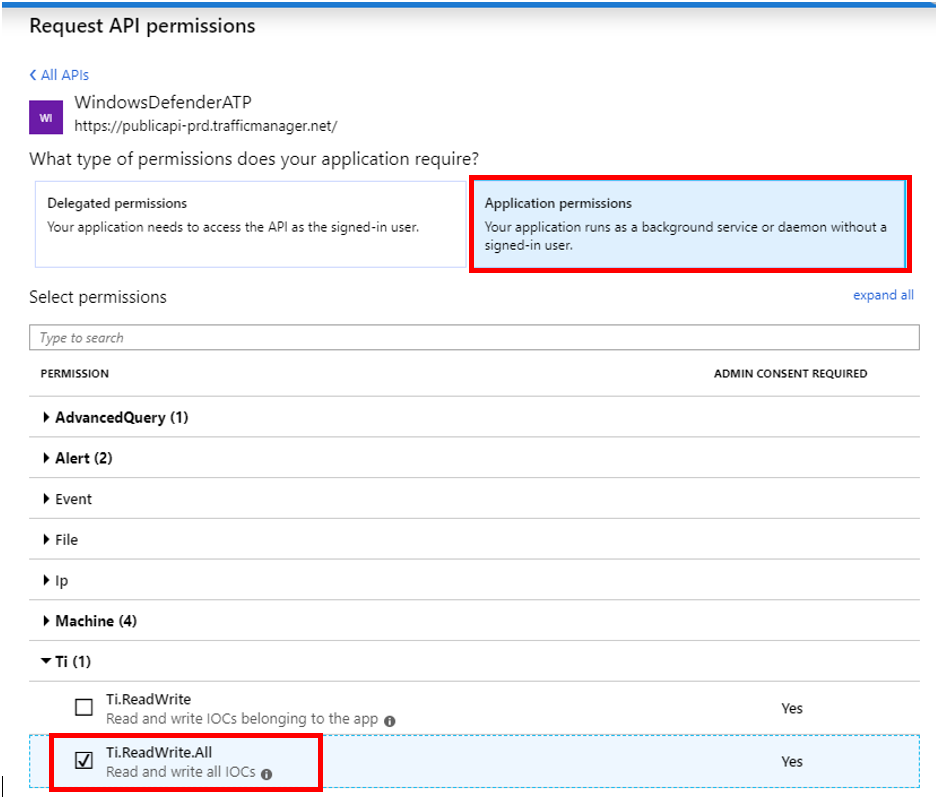
- Click on “Application permission” button and check the “TI.ReadWrite.All” checkbox.
- Click Add Permission.
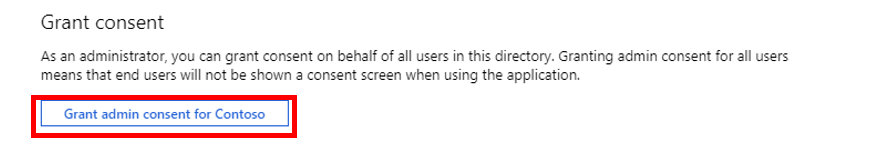
- On the “API Permission” screen, click on “Grant admin consent for…” button.
Done! You have successfully added the required permissions to the application.
Step 2: Enable advanced features in Microsoft Defender ATP
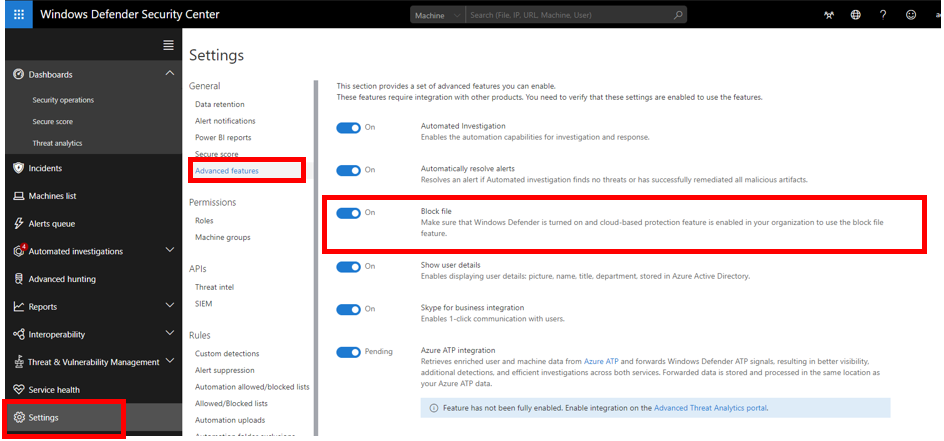
- Open the Settings menu in the Microsoft Defender ATP portal.
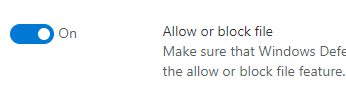
- Click on Advance features button and turn on “Block file” setting.
Done! You have successfully enabled the block feature.
Note: To use the block file feature, you need to make sure Windows Defender Antivirus is turned on and could-based protection feature is enabled in your organization.
Step 3: Run tests
It’s a good idea to run some tests to verify that we have configured the right mechanisms in place.
- Download the “Submit-Indicator.ps1” script from the link at the buttom of this blog.
- Save the script in the same folder you saved the Get-Token.ps1 script from the previous blogs.
- Open a PowerShell console.
- Change directory to the directory you saved the scripts from the previous steps.
- Run a command to submit an indicator in the following format:
PS> .\Submit-Indicator -indicrotType {sha1/sha256/IpAddress/Url}
-action {Alert/AlertAndBlock/Allowed}
-severity {Informational/Low/Medium/High}
-title {the alert’s title}
-description {the alert’s description}
-recommendedAction {the recommended action to remediate the alert}
For example, if we want to get an alert and block the execution of file with
sha1 = “b9174c8a1db96d329071ee46483a447c1d3abdc0” we can run the following command (write the command and parameters in one line):
PS>.\Submit-Indicator.ps1 -indicatorType FileSha1
-indicatorValue b9174c8a1db96d329071ee46483a447c1d3abdc0
-action AlertAndBlock
-severity High
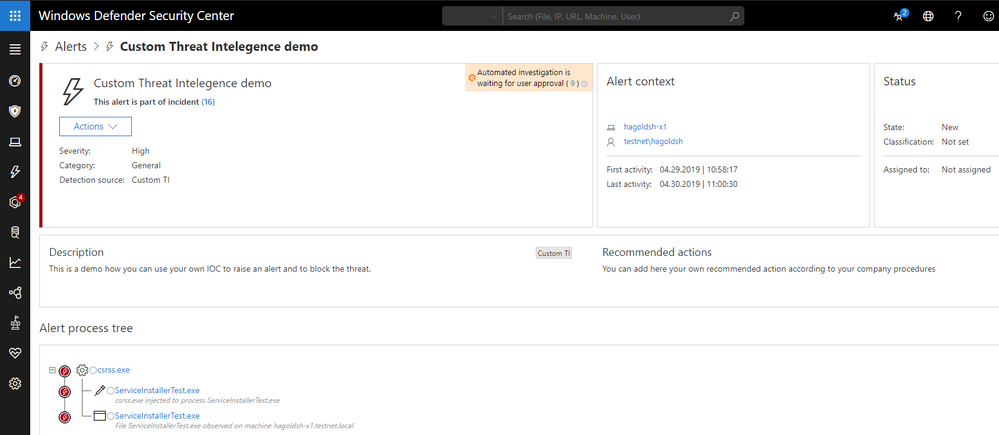
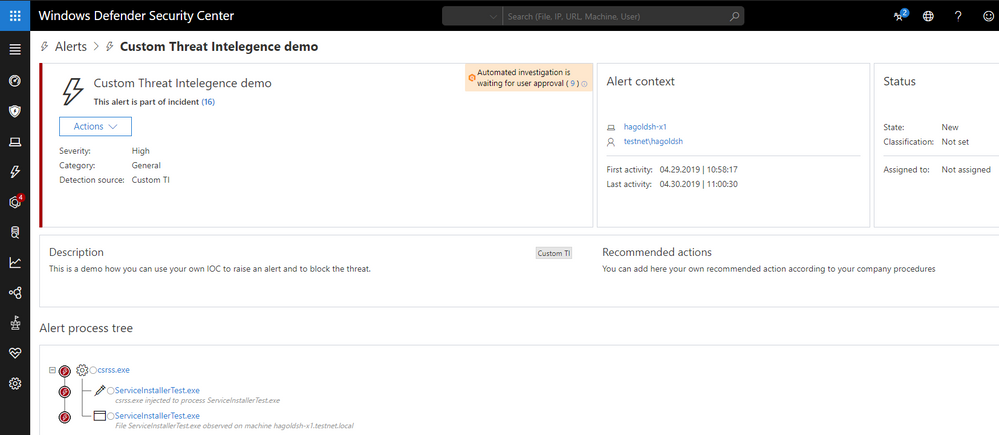
-title "Custom Threat Intelligence demo"
-description "This is a demo how you can use your own IOC to raise an alert and to block the threat."
-recommendedActions "You can add here your own recommended action according to your company procedures"
Done! You have successfully submitted an IOC to Microsoft Defender ATP
If you run a file with a SHA1 that is equal to the submitted SHA1 on a machine with the required Windows Defender Antivirus setting as mentioned above, the file will be blocked and quarantined and you will get a custom alert in Microsoft Defender ATP portal.
Conclusion:
In this blog, we demonstrated how you can easily submit your own IOC to Microsoft Defender ATP and set a remediation action for it.
In the next blog, we are going to demonstrate how we can automate export of IOC from MISP and submit the IOC to MDATP.
Thanks,
@Haim Goldshtein, security software engineer, Windows Defender ATP
@Dan Michelson, program manager, Windows Defender ATP
@Ben Alfasi, software engineer, Windows Defender ATP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 20 2019 02:00 PM
@Haim Goldshtein How is this different from the Indicators section, under Rules, in ATP settings?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 21 2019 10:02 PM
@Haim Goldshtein Great news here - just wondering though how this might/might not tie in to Sentinel?
At some point are these going to be "joined up" or stay separate ??
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 02 2019 02:19 AM
Hi @Vinay Varma
This API gives you a programmatic way to control the lists you maintain under the indicator section.
many organization trying to create automation on repetitive tasks to apply the changes faster and to free their employees to other tasks.
Thanks,
Haim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 02 2019 11:25 PM
@Haim Goldshtein @Dan Michelson
I've followed these instructions from Palo Alto https://live.paloaltonetworks.com/t5/MineMeld-Articles/How-to-Configure-MineMeld-to-Send-Indicators-...
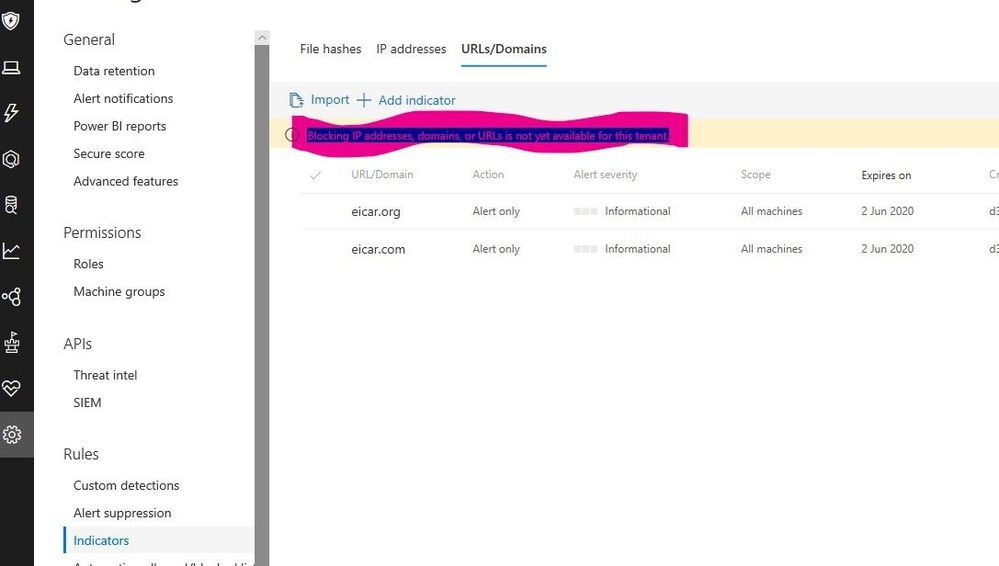
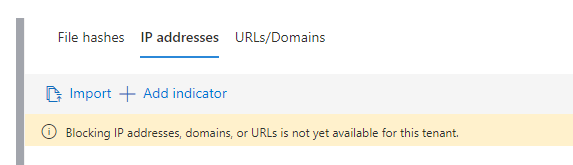
I can see the IOC's pushed into ATP but I see the below within SecurityCenter
I'm sure this functionality has previously worked from when I've manually added IOC's
Any ideas?
Thanks
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 03 2019 09:38 AM
Please check first how many items you are pushing.
Currently, there is a limit of 5K items in the list. If the batch you are trying to push is larger than the remaining room in the list, it may fail.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 03 2019 11:32 AM
I was more referring to the message that I'd crudely highlighted in the screen grab
Blocking IP addresses, domains, or URLs is not yet available for this tenant.
I'm sure I've had the ability to do these previously - at present, I can only block hashes. Is the URL/Domain blocking functionality going to be (re)made available soon?
Thanks
Danny
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 04 2019 05:19 AM
Hi Danny,
Blocking IPs, URL & Domains are features you need to turn on for you tenant.
if the feature is turned off, when going to Indicators page-> IP TAB you will see the following warning message:
to turn on the feature, you should go to Advance Feature tab, and turn Network Protection on:
Thank you for bring that up, I'll add that procedure to the blog.
Please check it and let me know if it works for you.
Thanks,
Haim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 04 2019 07:18 AM
Hey Haim
I don't see that option in Advanced features - is that a preview feature (I do have those enabled)
Thanks
Danny
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jun 04 2019 09:54 AM
@DannyC_Gamma This is something in preview right now. Stay tuned as it is coming.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 02 2019 11:42 PM - edited Jul 02 2019 11:58 PM
Hi Haim,
My message is sightly different would you be able to provide some context. We dont have Azure ATP enabled (yet), everything else is working as expected.
Is this function dependent on Azure ATP by any chance
?
Many Thanks
Mornay
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 07 2019 08:02 AM
Hi @Haim Goldshtein @Dan Michelson Just wondering if there might be anyone from the Defender ATP team at the RSA Conference in Singapore 15th-18th July?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jul 07 2019 02:55 PM
@David Caddick checking
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 12 2019 02:23 AM
@Haim Goldshtein Hi - the option is still not available - and I do not have the possibility to block custom URL or IP addresses. Any status on this issue ???
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Aug 15 2019 07:15 AM
Hi @Ronnie Lykke Madsen. Blocking IPs, domains, or URLs is currently available on limited preview only. This requires sending your custom list to network protection to be enforced which is an option that will be generally available soon. As it is not yet generally available, when Automated investigations finds this indicator during an investigation it will.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 21 2020 10:50 AM
Hello,
Great post. I would like to know if there is a way to check bulk IOCs and see if those IOCs are present in my group of machine? But I dont want to save them or import them it's just checked them if they resides in a machine of my group
Thanks in advance!