- Home
- Security, Compliance, and Identity
- Microsoft Defender for Endpoint Blog
- DynoRoot (CVE-2018-1111) exposed via Advanced Hunting
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
What is DynoRoot?
DynoRoot (CVE-2018-1111) is a remote command injection present in a script included by the DHCP client in Red Hat Enterprise Linux 6 and 7.
It allows a malicious attacker to run arbitrary commands on the attacked machine, in the highest privileges.
How does it work?
In the affected systems, the DHCP client has a script under "/etc/NetworkManager/dispatcher.d/". That script is executed each time NetworkManager receives a DHCP response from a DHCP server.
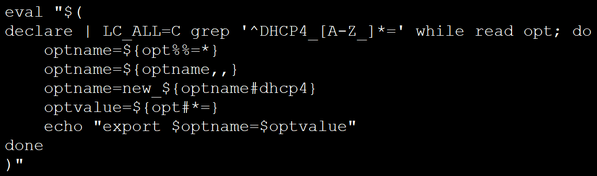
Unfortunately, the script has a command injection, as it evaluates DHCP options sent from a rouge server:
Have I been breached?
In collaboration with our sensor partners, the Windows Defender Advanced Threat Protection team is monitoring your Linux machines. We have released an Advanced Hunting query that you can run to see the processes spawned from DHCP clients, and act appropriately.
I'd like to watch a demo!
Our partners at Ziften and us composed a video showing the attack, as well as the advanced hunting query that shows how to hunt for DynoRoot exploitation.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.