- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- AzureAD group membership as a condition
AzureAD group membership as a condition
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 25 2019 07:23 AM
I am trying to create a playbook that checks a user against an AzureAD group. If the user is a member of the group it will perform one action (open ticket in service now) and if they are not a member it will perform a different one (create a powershell script to reset the password).
I create the check AzureAD group membership action and then create a condition based off that action. when I add the check AzureAD group result to the condition, it automatically places it within a for each loop. The result is, if the user is a member of the group it will successfully execute the True branch of the condition. But if the user is not a member of the group, the check AzureAD group action returns a null value, so the for each action never fires and the false branch of the condition never fires.
I tried to work around this by using the list AzureAD group members action instead. In this case, each member of the group is listed as a result. If the user is a member of the group, it will execute the true branch once and then the false branch one time for each other member of the group.
Is there a workaround for this use case?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 26 2019 08:54 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 29 2019 06:58 AM
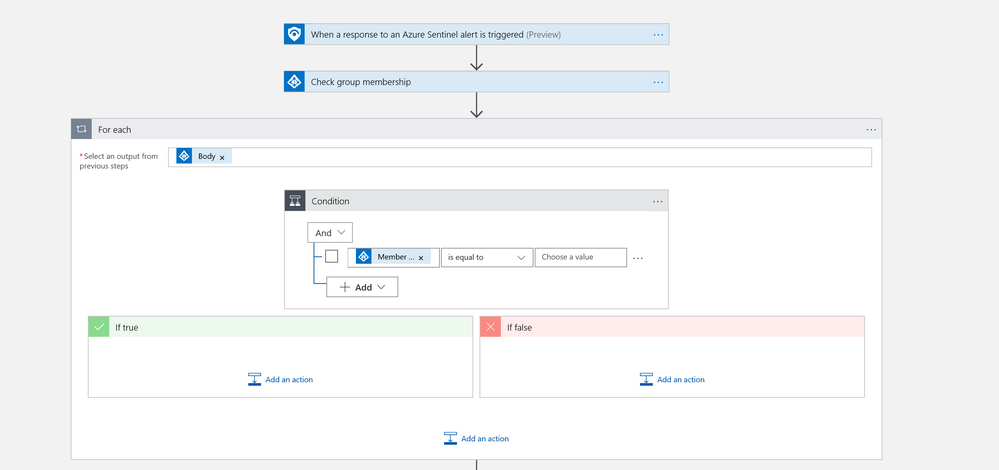
When you're setting up the actions in the playbooks, are you setting up a condition based on the previous data? My example:
1. When Azure Sentinel alert is triggered do the following:
2. Check group Membership with entities from the alert based on X group name.
3. Used the For Each template: If the Body of the message is "True" do the following, if it's "False" do the following. I'm using the connectors within the body.
Hope this helps,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apr 30 2019 10:18 AM
Hi Chris,
That is how I set it up, with one exception. I run a log query against the sentinel alert to get the username. Then I use the username in the check group membership step. Otherwise it is set up like you show. When I run against a user not in the group the false branch does not run. I think it is because the output body of the check membership step shows as "[]". So since it is null it does not execute the next for each step.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 03 2019 01:24 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 05 2019 04:01 AM
First, as discussed in another thread (and for the benefit of others), you don't need to query the Workspace but can rather extract the user names for an alert using the Sentinel connector actions.
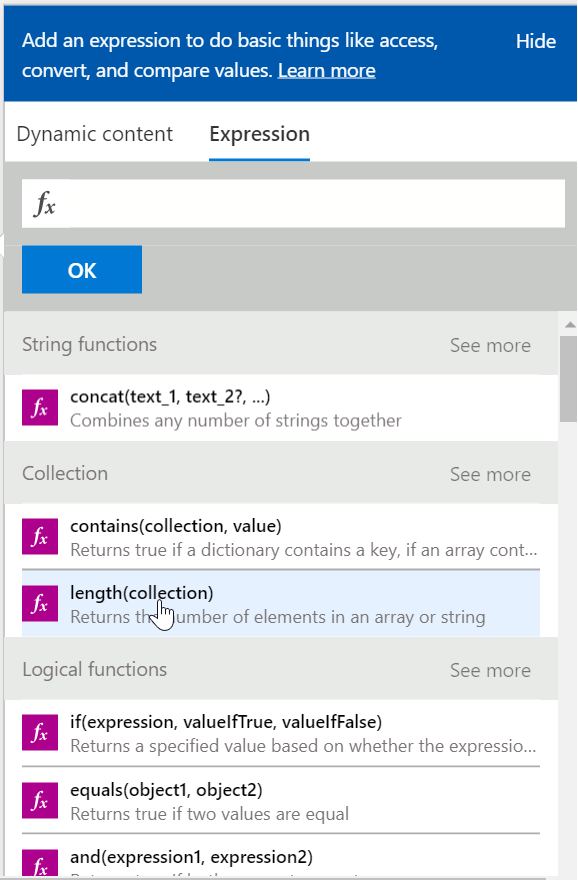
As to your question, did you try to use an expression on the returned value rather than using it directly? I didn't try, but Length below looks promising.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 10 2019 06:35 AM
Interestingly, when I switched the action from querying the alert ID with log analytics to getting the account name from the sentinel alert it allowed me to create the condition under check group membership without putting it in its own for each loop. It wasn't allowing me to do that before. So now I can just create the condition to check whether the body equals the group ID. Tested it out and it works.
Thanks,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May 12 2019 04:30 AM
Good to know. My guess is that the challenge is all JSON transformation. We need to learn more about Logic App JSON handling. We will share our findings.
~ Ofer