- Home
- Security, Compliance, and Identity
- Microsoft Sentinel
- Azure Sentinel Logic App Action Incident ID
Azure Sentinel Logic App Action Incident ID
- Subscribe to RSS Feed
- Mark Discussion as New
- Mark Discussion as Read
- Pin this Discussion for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 23 2019 07:47 AM
I am looking at the Azure Sentinel action in Logic Apps (AKA Playbooks) and I notice that when I try to do something like "Add a Label" or "Write a Comment" most of the fields (Subscription ID, Resource Group, and Workspace ID) can be obtained from the Sentinel trigger but I do not see any place to get the Incident ID.
Would this Logic App be triggered before the Incident is created and that is why there is no Incident ID? In any event, how would you get the Incident ID in order to use these actions? I see there is an entry to get all the Incidents but I don't see any way to accurately figure out which one to use.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 24 2019 11:34 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 24 2019 12:57 PM
Thanks for that information. Any idea why it would throw a
"Key 'Token' not found in connection profile"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 24 2019 01:21 PM
I havent seen that one before. maybe the connection needs to be re-authenticated. Go to the connection object in the resource group. Click Edit API blade. Click Authenticate. Click Save after authenticating.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 24 2019 03:15 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 26 2019 06:03 AM
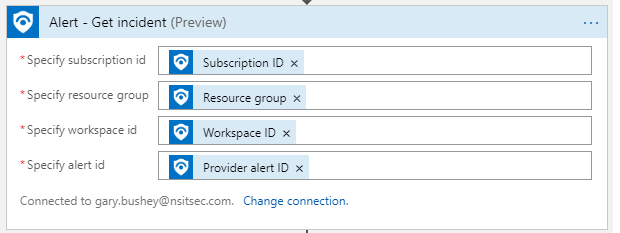
This is my configuration. Am I using the wrong variable for "Specify Alert Id"?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 26 2019 08:57 AM
SolutionYou need to use System Alert ID
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 26 2019 09:35 AM
That did the trick. I must have looked at the list of possible variables a dozen time and missed it every time! Thanks for all of your help!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 26 2019 10:19 AM
Awesome! glad a could help.
if you have cool playbooks feel free to help contribute to the github repo!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 27 2019 12:34 PM
@Nicholas DiCola (SECURITY JEDI) A little more weirdness. I can get my Incident, post a comment back to my Incident, Generate a Service Now Incident, and then post a message to Teams (in that order) just fine. However, if I try to post a comment back to my incident AFTER generating a ServiceNow incident I get the following error message (which talks about changing settings in a webapp that I certainly don't have access to). Any ideas?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 30 2019 08:17 PM
@Gary Bushey Are you able to post a screencap of what your add comment blade looks like? still can't get mine to work.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 22 2019 11:42 AM
@Gary Busheydid you ever get this to work, can get it to write static comments but that's it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 22 2019 01:00 PM
@ryanksmith I have not tried it recently but when I checked last time MS was working on a fix.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oct 24 2019 06:18 AM
@ryanksmith I just tried this again and I was NOT able to get it to work yet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 06 2019 01:45 AM
Any update of the topic ? I just had the same HTTP 400 mentionned above
Here is my Playbook
- Sentinel input
- Mail approval
- Approved: post message on Teams --> It works
- Refused: close the incident --> Same error as @Gary Bushey
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 06 2019 03:41 AM
@ClémentB I have pinged MS about it last week but have not heard anything back from them.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 09 2019 05:40 AM
I just tried this again this morning and it worked! I did completely get rid of the actions and started over but it worked :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 09 2019 05:39 PM
@Gary BusheyTried not luck, are you able to post your work flow, will tr y a few others once I get back into the office on Tuesday
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nov 10 2019 06:45 AM
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 26 2019 08:57 AM
Solution