- Home
- Azure Data
- Azure Database Support Blog
- How to check connectivity to Azure SQL DB, Managed Instance, Azure Database for MySQL and PostgreSQL
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
First published on MSDN on Jul 17, 2017
Scenario:
Sometimes when connection to Azure SQL DB, Managed Instance, MySQL or PostgreSQL on Azure Database failed you want to test the network layer to confirm this is not network issue that prevents you from accessing your Azure DB service.
Note that this is manly relevant for connections originated out of Azure as described here: Ports beyond 1433 for ADO.NET 4.5 However, this test should be successful from within Azure as well.
For Managed Instance read more about connect you application here: Connect your application to Azure SQL Database Managed Instance
Using these tests result in other than success as shown here means you have a network issue with accessing the server.
This test should succeed regardless of the firewall settings on the Azure SQL DB.
More information about troubleshooting connectivity can be found here: Troubleshooting Connectivity Common Scenarios
For Azure SQL DB use port 1433
for Managed Instance please use the FQDN of your instance.
for Managed Instance Public Endpoint please use your endpoint FQDN with TCP port 3342
For Azure Database for MySQL use port 3306
For Azure Database for PostgreSQL use port 5432
Using PowerShell (Recommended)
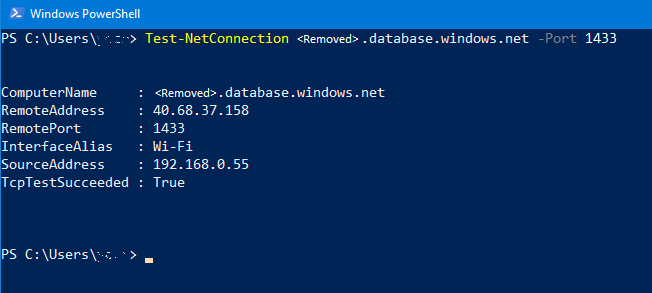
Use the following command to confirm you have true for the TcpTestSucceeded
Test-NetConnection <YourServerName>.database.windows.net -Port <TCPPort>
Using PsPing
Download the PsPing tool.
psping <YourServerName>.database.windows.net:<TCPPort>

Get current outbound IP address
Invoke-WebRequest ipinfo.io/ip | select Content | fl
Note : this method test the outbound IP for for 80 which is used for web browsing, in some scenario depend on your network topology can set different outbound IP for different TCP ports.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.